The PKI Information Distribution Problem
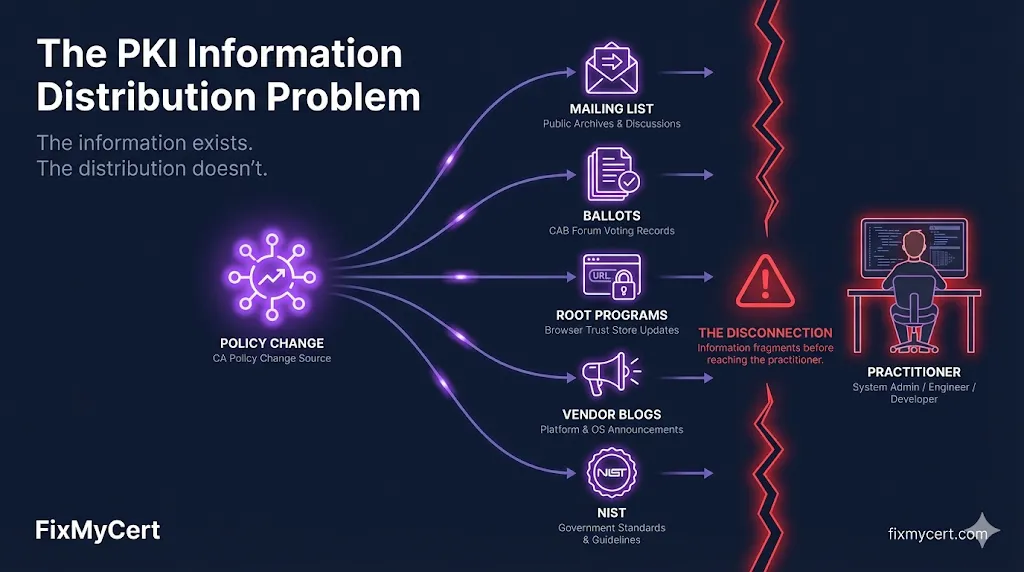
PKI doesn't have an information problem. It has a distribution problem. Every significant policy change gets documented somewhere — but nowhere that practitioners actually look.
I run a PKI compliance platform. I track certificate lifecycle changes, browser root program updates, and CA/Browser Forum ballots as part of my daily workflow.
And I still almost missed a major Chrome policy change.
The change in question: Chrome is sunsetting the clientAuth EKU (Extended Key Usage — the field in a certificate that defines what it's allowed to do) in publicly trusted TLS server certificates. Going forward, public CAs won't be permitted to issue certificates containing both serverAuth and clientAuth EKUs. The browsers are enforcing a strict separation — public PKI is for server authentication only.
Google originally planned to enforce this in mid-2026. Then they pushed the deadline back nine months to March 15, 2027, via the Chrome Root Program Policy v1.8, to give organizations more time to disentangle their mutual TLS (mTLS) architectures.
A nine-month extension on a deadline that directly affects any enterprise using publicly trusted certificates for client, device, or application authentication — and I almost missed it entirely.
I didn't catch it from the Chrome Root Program's own communications. I didn't catch it from the CA/Browser Forum mailing list. I found out from a vendor blog post, during what was supposed to be a thorough, deliberate compliance review.
That experience crystallized something I'd been thinking about for a while: PKI doesn't have an information problem. It has a distribution problem.
The Information Exists — It's Just Buried
Every significant PKI policy change gets documented somewhere. The CA/Browser Forum publishes ballots. Browser root programs post updates to their respective channels. NIST releases guidance. CAs publish advisories.
The issue is where that information lives and how practitioners are expected to find it.
Here's what "staying current on PKI compliance" actually looks like in practice:
- CA/Browser Forum ballots are discussed across mailing list threads that routinely reach 200+ replies spread over months. The final ballot language — the part that actually affects your certificates — is a fraction of the total discussion. Finding the actionable change means reading through procedural debate, editorial suggestions, and cross-references to other ballots.
- Browser root program updates ship through separate channels with no unified changelog. Chrome posts to one place. Mozilla posts to another. Apple and Microsoft have their own cadences. A change in one program might contradict or extend a deadline in another.
- NIST publications like SP 800-57 (key management), SP 800-52 (TLS guidelines), and SP 800-131A (algorithm transitions) update on their own schedule, with revision notes that assume you've read every prior version.
- Vendor blogs and advisories are often the fastest way to learn about changes — but they filter information through a commercial lens. They'll highlight what affects their product. They won't necessarily cover what affects your environment.
There is no single feed a practitioner can subscribe to that answers the question: "What changed this month that affects my certificates?"

Case in Point: The clientAuth Sunset Cascade
The clientAuth EKU sunset is a perfect example of the distribution problem in action. Chrome set the policy. Then every major CA had to respond — on their own timeline, through their own channels, with their own nuances:
DigiCert extended their hard sunset date from May 2026 to March 1, 2027, aligning just ahead of Chrome's deadline. Sectigo will permanently remove clientAuth from newly issued certificates by February 2027 — but they already phased it out as a default inclusion in late 2025, meaning it can still be manually requested during the transition window. Let's Encrypt has already removed clientAuth from their default classic profiles, but support for dedicated client profiles will continue through the 2027 timeline.
Three CAs. Three different approaches. Three different transition periods. Published across three different sets of documentation, blog posts, and support articles.
If your infrastructure relies on publicly trusted certificates for client authentication — mutual TLS between services, device authentication, application-level identity — those workflows will break once your current certificates expire after the March 2027 cutoff. The migration path is clear: move client authentication workloads to a private CA or a dedicated internal PKI. But knowing that you need to migrate requires first knowing the deadline changed, then knowing how your specific CA is handling the transition, then mapping that against your renewal schedule.
That's three layers of information discovery just for a single policy change. And this is one of the more well-publicized ones.
The People Who Need This Most Have the Least Time for It
Here's what makes the distribution problem especially damaging: the people managing certificates day to day are rarely the same people monitoring policy mailing lists.
A sysadmin renewing certificates is spending maybe 5% of their time on certificate management. They're not subscribed to mdsp@groups.google.com. They're not reading CA/Browser Forum ballot discussions. They might not even know those channels exist.
An enterprise security architect setting PKI policy has more awareness but less bandwidth — they're managing firewall rules, IAM configurations, and incident response alongside certificate governance.
The practitioners who need plain-language answers about certificate policy changes are almost never in the rooms (or on the mailing lists) where those changes get debated.
Why This Is Getting Worse, Not Better
Three forces are compounding the distribution problem right now:
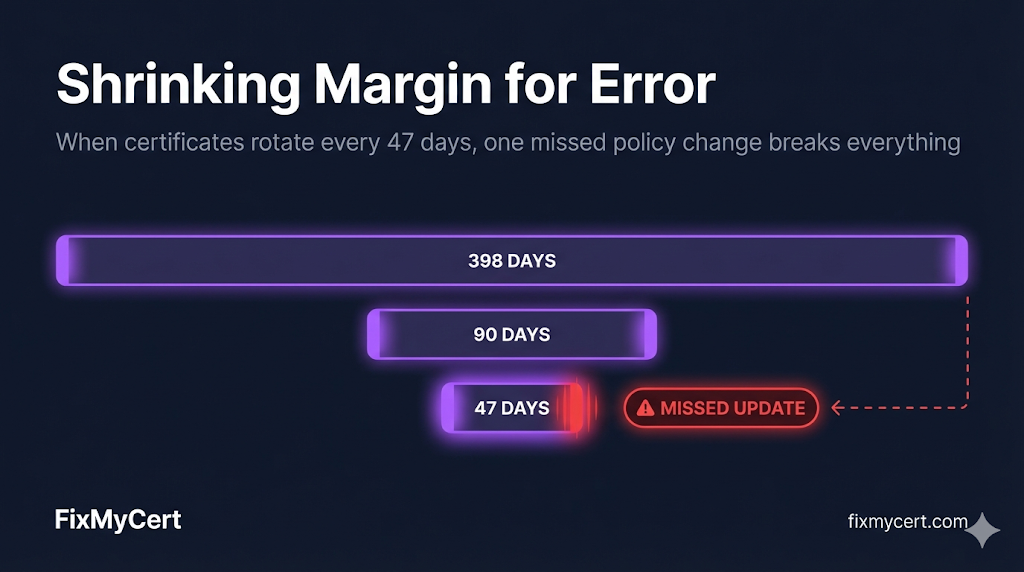
Shorter certificate lifecycles. With 47-day TLS certificates on the horizon under SC-081, the margin for error on compliance changes drops to near zero. Missing a policy update when certificates last a year is recoverable. Missing one when certificates rotate every 47 days means your automation is silently issuing non-compliant certificates before anyone notices.
More regulatory sources. PKI compliance isn't just about the CA/Browser Forum anymore. Depending on your environment, you might need to track Mozilla's root store policy, Apple's requirements, Chrome's root program, PCI DSS certificate requirements, WebTrust audit criteria, ETSI standards, and sector-specific regulations. Each has its own publication cadence, format, and distribution channel.
Post-quantum transition planning. The NIST post-quantum standards (FIPS 203/204/205) are driving a wave of algorithm deprecation timelines. Tracking which algorithms are deprecated, when, and by which authority — RSA to ML-KEM transitions alone touch key management, certificate issuance, and TLS configuration simultaneously — adds another layer of monitoring that didn't exist two years ago.
What Solving This Actually Looks Like
The distribution problem doesn't get solved by creating another mailing list or another vendor newsletter. It gets solved by doing the translation work that sits between raw policy changes and practitioner action.
That means:
Plain-language breakdowns of what changed, written in terms practitioners actually use. Not "Ballot SC-081v3 amends section 6.3.2 of the TLS Baseline Requirements" — instead, "TLS certificate maximum lifetimes are dropping to 47 days by March 2029. Here's the phase-in schedule and what it means for your renewal automation."
Cross-referencing across sources. When Chrome changes a clientAuth deadline, connecting that to how it interacts with Mozilla's root store policy and what it means for enterprises running mTLS. One change, one place, all the context.
Defining terms in the same sentence they appear. PKI documentation is full of terms like DCV (Domain Control Validation — the process of proving you control a domain before a CA will issue a certificate) and OCSP (Online Certificate Status Protocol — a method for checking whether a certificate has been revoked in real time). Every practitioner deserves to understand these concepts without hunting through RFCs.
This is what I built FixMyCert to do. Not vendor marketing. Not gated whitepapers. Practitioner-focused guidance in plain language, covering the full landscape — from CA/Browser Forum ballots to browser root programs to NIST publications — so you don't have to monitor a dozen different channels to know what affects your certificates.
The Bottom Line
If someone whose job is tracking PKI compliance changes can miss a nine-month deadline extension during a focused review session, the system is broken. Not the person — the system.
The information exists. The distribution doesn't.
That's the gap. And that's what we're here to close.
Start here
The FixMyCert Compliance Hub tracks CA/Browser Forum requirements, Chrome Root Program deadlines, Mozilla Root Store policies, and more — all in one place, in plain language.
View the Compliance Hub →Have you been blindsided by a certificate policy change you should have known about? Connect with me on LinkedIn — I'd genuinely like to hear your story. It helps me build better coverage.
Related FixMyCert Resources
PKI Compliance Hub
Track every CA/B Forum, Chrome Root Program, and Mozilla Root Store deadline in one place.
Explore GuideClientAuth EKU Sunset Guide
The full timeline and migration path for the clientAuth EKU removal from public certificates.
Explore Guide47-Day Certificate Timeline
The complete timeline for shorter certificate lifetimes and what each milestone means.
Explore GuidePost-Quantum Cryptography Guide
NIST FIPS 203/204/205 standards and the algorithm transition timeline.
Explore