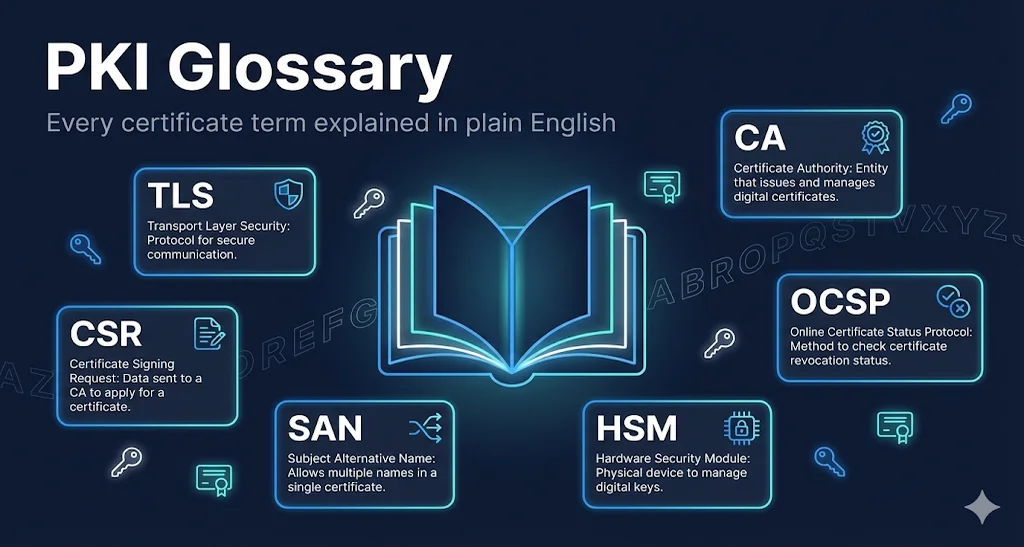
PKI Glossary
Plain English definitions for certificates, cryptography, and security terms
A
ACME
(Automatic Certificate Management Environment)Protocol that automates certificate issuance and renewal. Used by Let's Encrypt and other CAs to enable automated certificate management without human intervention.
AIA
(Authority Information Access)Certificate extension that tells clients where to find the issuing CA's certificate and OCSP responder. Essential for building and validating certificate chains.
C
CA
(Certificate Authority)A trusted organization that issues digital certificates. CAs verify the identity of certificate requesters and digitally sign certificates to vouch for their authenticity.
CAA
(Certificate Authority Authorization)DNS record that specifies which Certificate Authorities are allowed to issue certificates for a domain. Helps prevent unauthorized certificate issuance.
Certificate Chain
The sequence of certificates from an end-entity (leaf) certificate through intermediate CA(s) to a trusted root CA. Browsers follow this chain to verify trust.
Certificate Pinning
Security technique where an application only accepts specific certificates or public keys, rather than any certificate signed by a trusted CA. Largely deprecated due to operational challenges.
Certificate Transparency
(CT)Public logging system where CAs must record all issued certificates. Allows domain owners to detect mis-issued certificates for their domains.
Cipher Suite
A combination of algorithms used in a TLS connection: key exchange, authentication, encryption, and message authentication. Example: TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
Common Name
(CN)The primary identity field in a certificate, traditionally containing the domain name. Now largely replaced by Subject Alternative Names (SANs) for domain validation.
CRL
(Certificate Revocation List)A list published by a CA containing serial numbers of revoked certificates. Clients download CRLs to check if a certificate has been revoked.
CSR
(Certificate Signing Request)A message sent to a Certificate Authority containing your public key and identity information (domain, organization). The CA uses this to create your signed certificate.
D
DER
(Distinguished Encoding Rules)Binary format for encoding certificates. Unlike PEM, DER files are not human-readable. Common file extensions: .der, .cer
Diffie-Hellman
(DH)Key exchange algorithm that allows two parties to establish a shared secret over an insecure channel. ECDHE (Elliptic Curve Diffie-Hellman Ephemeral) is the modern variant.
Digital Signature
Cryptographic proof that a message was created by a specific sender and hasn't been altered. Created by encrypting a hash of the message with the sender's private key.
DV
(Domain Validation)The simplest certificate validation level. CA only verifies the requester controls the domain (via email, DNS, or HTTP challenge). No organization verification.
E
ECC
(Elliptic Curve Cryptography)Public key cryptography using elliptic curves. Provides equivalent security to RSA with smaller key sizes (256-bit ECC ≈ 3072-bit RSA).
ECDHE
(Elliptic Curve Diffie-Hellman Ephemeral)Modern key exchange algorithm combining ECC with Diffie-Hellman. The 'Ephemeral' means new keys are generated for each session, enabling Perfect Forward Secrecy.
EKU
(Extended Key Usage)A certificate extension that specifies the permitted uses for a certificate, such as server authentication, client authentication, code signing, or email protection. Applications check the EKU to ensure a certificate is authorized for its intended purpose.
EV
(Extended Validation)Highest certificate validation level. CA performs extensive verification of the organization's legal identity. Once displayed a green bar in browsers (no longer).
H
HSM
(Hardware Security Module)Physical device that securely stores cryptographic keys. Keys never leave the HSM—cryptographic operations happen inside. Used to protect CA root keys.
HSTS
(HTTP Strict Transport Security)HTTP header that tells browsers to only connect via HTTPS. Prevents downgrade attacks and accidental HTTP connections.
I
Intermediate Certificate
A certificate that sits between the root CA and end-entity certificates in the chain. Root CAs issue intermediates, which then issue end-entity certificates. Protects the root key.
J
JKS
(Java KeyStore)Java's proprietary keystore format for storing certificates and private keys. Being replaced by PKCS#12 in newer Java versions.
K
Key Pair
A mathematically linked public key and private key. Data encrypted with the public key can only be decrypted with the private key, and vice versa.
Keystore
A file or database that stores private keys and their associated certificates. In Java, typically a JKS or PKCS#12 file.
L
Leaf Certificate
The end-entity certificate at the bottom of a certificate chain. This is the certificate installed on a server or used by an application. Also called 'server certificate' or 'end-entity certificate.'
M
mTLS
(Mutual TLS)TLS connection where both client and server authenticate with certificates. Standard TLS only authenticates the server; mTLS adds client certificate authentication.
O
OCSP
(Online Certificate Status Protocol)Real-time protocol for checking if a certificate has been revoked. Client sends certificate serial number to OCSP responder, gets back 'good,' 'revoked,' or 'unknown.'
OCSP Stapling
Optimization where the server fetches its own OCSP response and 'staples' it to the TLS handshake. Improves privacy and performance vs. client-side OCSP checking.
OID
(Object Identifier)A globally unique numeric identifier used to name objects in certificate standards. OIDs follow a hierarchical tree structure (like 1.3.6.1.5.5.7.3.1 for Server Authentication) and are defined by standards bodies like ISO, ITU-T, and IANA.
OV
(Organization Validation)Middle-tier certificate validation. CA verifies domain ownership AND the organization's legal existence. Organization name appears in certificate but no special browser UI.
P
PEM
(Privacy-Enhanced Mail)Text format for certificates and keys, enclosed in '-----BEGIN CERTIFICATE-----' headers. Base64-encoded DER with headers. Most common format on Linux/Unix.
Perfect Forward Secrecy
(PFS)Property where compromise of long-term keys doesn't compromise past session keys. Achieved using ephemeral key exchange (ECDHE). If server key is stolen, past traffic stays encrypted.
PFX / PKCS#12
Binary format that bundles a certificate with its private key (and optionally the chain) in a single password-protected file. Common on Windows. Extensions: .pfx, .p12
Private Key
The secret half of a key pair. Must be kept confidential. Used to decrypt data encrypted with the public key and to create digital signatures.
Public Key
The shareable half of a key pair. Distributed freely (often inside a certificate). Used to encrypt data for the key owner and to verify their digital signatures.
R
Root Certificate
A self-signed certificate at the top of a certificate chain. Root certificates are pre-installed in operating systems and browsers as 'trust anchors.'
Root Store
The collection of trusted root certificates in an operating system, browser, or application. Chrome, Mozilla, Apple, and Microsoft each maintain their own root stores.
RSA
Widely-used public key cryptography algorithm named after creators Rivest, Shamir, and Adleman. Common key sizes: 2048-bit, 4096-bit.
S
SAN
(Subject Alternative Name)Certificate extension listing all identities the certificate is valid for. Can include multiple domain names, IP addresses, email addresses. Modern certificates rely on SANs rather than Common Name.
SCEP
(Simple Certificate Enrollment Protocol)Protocol for automated certificate enrollment, commonly used for network devices and MDM (mobile device management).
Self-Signed Certificate
A certificate signed by its own private key rather than a CA. Not trusted by browsers/systems by default. Appropriate for testing, internal services, or when you control the trust store.
SHA-256
Cryptographic hash function producing a 256-bit digest. Part of the SHA-2 family. Standard for certificate signatures after SHA-1 deprecation.
SNI
(Server Name Indication)TLS extension that allows a client to specify which hostname it's connecting to during the handshake. Enables multiple HTTPS sites on a single IP address.
SSL
(Secure Sockets Layer)Predecessor to TLS. All SSL versions (1.0, 2.0, 3.0) are deprecated and insecure. 'SSL' is still commonly used to mean 'TLS' in casual conversation.
T
TLS
(Transport Layer Security)Cryptographic protocol securing communications over networks. Current versions: TLS 1.2 and TLS 1.3. Successor to SSL.
TLS Handshake
The process where client and server negotiate TLS version, cipher suite, authenticate (via certificates), and establish session keys before transmitting encrypted data.
Trust Store
A file or database containing trusted CA certificates (typically roots and intermediates). Used to validate certificate chains. In Java, often a separate JKS file.
W
Wildcard Certificate
A certificate valid for a domain and all its single-level subdomains. *.example.com covers www.example.com, api.example.com, but NOT example.com or sub.api.example.com.
X
X.509
The standard format for public key certificates used in TLS/SSL. Defines the structure and fields of digital certificates including subject, issuer, validity period, and extensions.
SSL/TLS & PKI FAQ
Quick answers to the most common certificate and security questions