What Is Post-Quantum Cryptography?
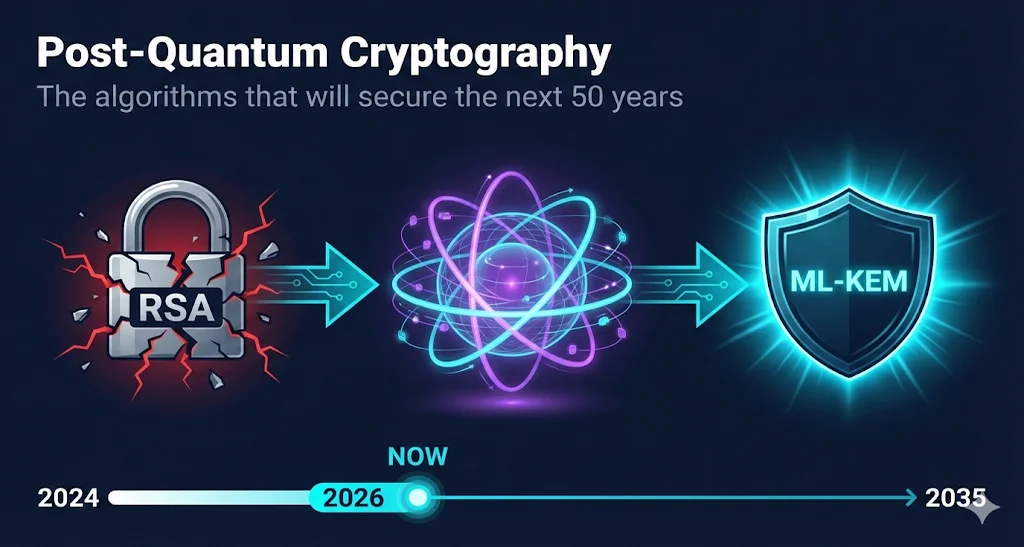
Post-quantum cryptography (PQC) refers to cryptographic algorithms designed to resist attacks from both classical computers AND future quantum computers.
The Problem
RSA, ECC, and Diffie-Hellman algorithms that secure virtually all internet communications today can be broken by a sufficiently powerful quantum computer using Shor's algorithm.
The Solution
New algorithms based on mathematical problems that quantum computers can't efficiently solve—lattice-based, hash-based, and code-based cryptography.
The timeline: NIST spent 8 years evaluating 82 submissions from cryptographers worldwide. In August 2024, they finalized the first three standards. Your organization needs to transition before January 2035.
The "Harvest Now, Decrypt Later" Threat
You might think: "Quantum computers are decades away. Why worry now?"
Because adversaries are already harvesting encrypted data today, planning to decrypt it once quantum computers arrive. This is called the "Harvest Now, Decrypt Later" (HNDL) attack.
What's at risk:
- TLS certificates (your web traffic)
- Code signing certificates (software integrity)
- S/MIME certificates (email encryption)
- Document signing (legal validity)
- VPN tunnels (network security)
The Math That Matters:
- 10-30 yearsData encrypted today may need to remain confidential
- 10-20 yearsQuantum computers capable of breaking RSA-2048 may arrive
- 5-10 yearsMigration to PQC algorithms takes for large organizations
- Result:You're already behind schedule.
"The time to start transitioning is now, even though a cryptographically relevant quantum computer may be years or decades away."— NIST IR 8547
NIST's Post-Quantum Cryptography Standards
After 8 years of global evaluation, NIST finalized three standards in August 2024, with a fourth in 2025:
ML-KEM
FIPS 203 - FinalizedModule-Lattice Key Encapsulation Mechanism (formerly CRYSTALS-Kyber)
ML-DSA
FIPS 204 - FinalizedModule-Lattice Digital Signature Algorithm (formerly CRYSTALS-Dilithium)
SLH-DSA
FIPS 205 - FinalizedStateless Hash-Based Digital Signature Algorithm (formerly SPHINCS+)
FN-DSA
FIPS 206 - FinalizedFFT-based NTRU Digital Signature Algorithm (formerly FALCON)
Coming Soon
| Algorithm | Expected | Notes |
|---|---|---|
| HQC | 2027 | Backup KEM using different math than ML-KEM |
Good News: Symmetric Crypto Is Safe
Not everything needs to change. Symmetric cryptographic algorithms are NOT significantly vulnerable to quantum attacks:
Safe (Keep Using)
- AES-128, AES-256 (encryption)
- SHA-256, SHA-384, SHA-512 (hashing)
- HMAC (message authentication)
- SHA-3, ChaCha20
Vulnerable (Must Replace)
- RSA (key exchange and signatures)
- ECDSA, EdDSA (signatures)
- ECDH, DH (key exchange)
- DSA (signatures)
Why the difference?
Quantum computers use Shor's algorithm to break algorithms based on integer factorization (RSA) and discrete logarithms (DH/ECDH/ECDSA). Symmetric algorithms use different math that quantum computers can't efficiently attack.
Where Are We Now?
FIPS 203, 204, 205 published
FIPS 206 published, HQC selected
First PQC certificates available
Backup KEM option ready
112-bit algorithms deprecated
Full transition required
Your Post-Quantum Migration Checklist
You don't need quantum computers to exist to start preparing. Here's what to do now:
Phase 3: Testing & Early Deployment
NOW - 2026- Deploy hybrid TLS - ML-KEM alongside classical algorithms
- Validate interoperability - Browsers, clients, servers
- Performance testing - PQC algorithms have different characteristics
- Update certificate policies - Prepare for PQC certificate issuance
- Pilot PQC certificates - First commercial certs now available
Crypto-Agility is Key
The biggest lesson from PQC: your systems should be able to swap cryptographic algorithms without a complete rebuild. If you're locked into RSA forever, you have a bigger problem than quantum computers.
The Hybrid Approach: Belt and Suspenders
During the transition, many organizations will use "hybrid" cryptography—combining classical and post-quantum algorithms together.
Example Hybrid TLS Key Exchange:
Why Hybrid?
- If ML-KEM has an undiscovered weakness, X25519 protects you
- If quantum computers arrive early, ML-KEM protects you
- You get the security of both until confidence in PQC grows
Current Hybrid Support:
X25519Kyber768 (preliminary ML-KEM)
X25519Kyber768
ML-KEM in AWS-LC
Planning for 2026
Check your browser: Visit pq.cloudflareresearch.com to see if your browser already supports post-quantum key exchange.
What Changes for TLS/SSL Certificates?
Certificates themselves will change to use PQC algorithms:
Current Certificates
Future PQC Certificates
Key Differences:
| Aspect | RSA-2048 | ML-DSA-65 |
|---|---|---|
| Public key size | 256 bytes | ~1,952 bytes |
| Signature size | 256 bytes | ~3,293 bytes |
| Security level | 112-bit classical | 128-bit quantum |
Larger Sizes Matter:
- Increased TLS handshake overhead
- More data in certificate chains
- May require infrastructure updates
Frequently Asked Questions
When will quantum computers break current encryption?
Nobody knows for certain. Estimates range from 10-30 years. But the "harvest now, decrypt later" threat means adversaries are collecting encrypted data today to decrypt later. Long-lived secrets are already at risk.
Is AES-256 quantum-safe?
Yes. Symmetric algorithms like AES are not significantly weakened by quantum computers. A 256-bit AES key provides 128-bit security against quantum attacks, which is still extremely strong.
Should I wait for the industry to figure this out?
No. NIST explicitly recommends starting now. The migration will take years, and early adopters will have smoother transitions. Begin with discovery and planning immediately.
What about my existing certificates?
Existing RSA/ECC certificates remain valid until they expire. The urgency is about new certificate issuance and long-term encrypted data, not immediately replacing every certificate.
Will my HSMs support PQC?
Most HSM vendors are adding PQC support. Check with your vendor for their roadmap. This is a critical planning consideration.
What if NIST's algorithms are broken later?
This is why NIST standardized multiple algorithms and continues evaluating alternatives. SLH-DSA uses different math than ML-DSA specifically as a backup. Crypto-agility lets you adapt.
Related Resources
Crypto Agility Guide
Build systems that can rapidly adopt post-quantum algorithms.
Encryption Basics
Understand the cryptographic foundations that PQC replaces.
RSA vs ECC
Compare current algorithms vulnerable to quantum attacks.
PKI Compliance Hub
Track PQC migration deadlines and compliance requirements.
Certificate Lifecycle
Plan certificate renewals around algorithm migration timelines.
Learn More
Official NIST Resources:
- NIST Post-Quantum Cryptography Project
- FIPS 203: ML-KEM Standard
- FIPS 204: ML-DSA Standard
- FIPS 205: SLH-DSA Standard
- NIST IR 8547: Transition to Post-Quantum Cryptography