Your Internal CA Doesn't Have a CPS. Here's Why That's a Problem.
When most people hear "Certificate Practice Statement," they think of DigiCert, Sectigo, or Let's Encrypt — the public CAs that issue certificates for websites. Those CAs are required to publish a CPS. Browser root programs demand it. Auditors verify it. If they don't follow it, they get distrusted (ask Entrust how that went).
But here's what nobody talks about: your internal CA needs one too.
If you're running Microsoft ADCS, EJBCA, AWS Private CA, or any other private Certificate Authority, you're issuing certificates that your users, devices, and systems depend on every single day. Wi-Fi authentication. VPN access. Code signing. Device identity. Smart card login. Internal TLS.
And most of you are doing it with zero documented governance.
The Governance Gap Is Massive
Let's look at what the research actually says:

The Keyfactor/Ponemon Institute research paints a bleak picture of enterprise PKI governance. Across multiple years of surveys covering thousands of IT and security professionals, the findings are consistent: most organizations are flying blind.
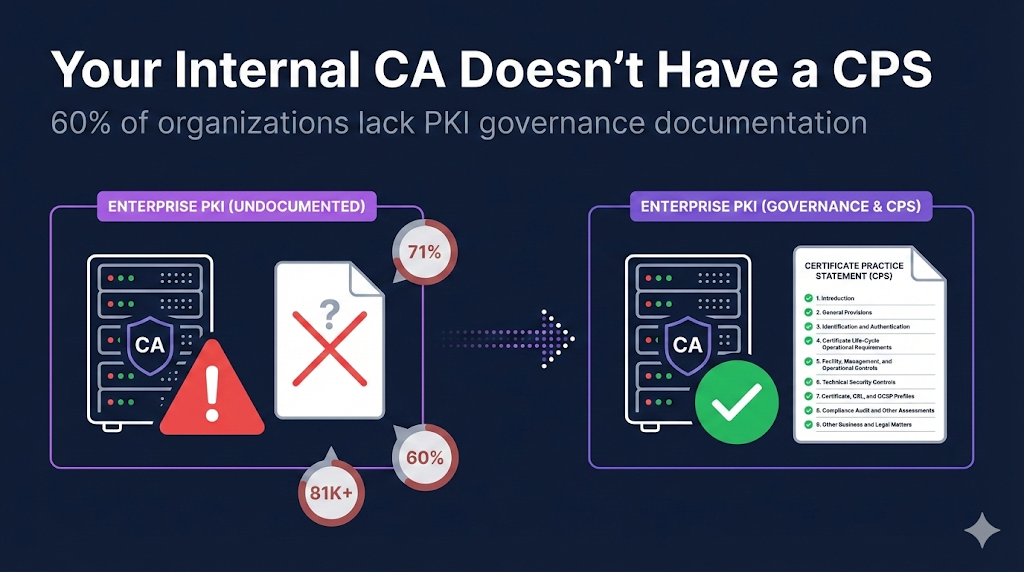
60% of organizations either have no strategy for managing cryptography and machine identities, or only a limited strategy that covers certain applications. That's not a typo — six out of ten organizations running PKI don't have a comprehensive plan for it.
Only one-third have what researchers call a "mature cryptographic center of excellence" — meaning the other two-thirds lack the organizational structure to even set PKI policy, let alone enforce it.
71% don't know how many keys and certificates they have. The average organization manages over 81,000 internally trusted certificates. If you don't know what you have, you definitely don't have documented policies governing how those certificates are issued, revoked, and managed.
74% report that digital certificates have caused unanticipated downtime or outages. And 56% specifically cite certificate expiration or configuration errors as the cause.
Microsoft — the company whose Active Directory Certificate Services is probably the most widely deployed enterprise CA in the world — acknowledges in their own documentation that it is "quite common to delay creating a CP/CPS until after some CAs are already deployed in the environment." They also call out "a common error for organizations during PKI solutions deployment is the lack of PKI governance or oversight."
When the vendor who built the tool is publicly saying most people don't govern it properly, that should get your attention.
"But We're Not a Public CA. Why Do We Need a CPS?"
Fair question. Here's the answer: because every compliance framework you care about expects it.
Auditors Are Asking
Whether you're going through SOC 2, ISO 27001, PCI DSS, or WebTrust, auditors expect documented controls around how certificates are issued and managed. A CPS structured per RFC 3647 is the industry-standard way to document those controls.
Walk into an audit and say "we have an ADCS server and it issues certs" — you'll get findings. Walk in with a documented CPS that maps your practices to RFC 3647 sections — you're speaking the auditor's language.
Regulators Are Expecting It
NIST SP 800-57 Part 2 is explicit: any organization employing cryptography to provide security services needs key management policy, practices, and planning documentation. That's not limited to public CAs. That's any organization using PKI.
The Federal PKI requires CPS documentation that maps to the Common Policy Framework for any CA that wants to participate. AWS recommends CP/CPS documentation in their Private CA best practices. These aren't suggestions — they're the professional standard.
Incident Response Depends On It
When something goes wrong — a key compromise, a rogue certificate, a CA server breach — the first question is: "What are our procedures?" If the answer is "we don't have any documented," you've turned an incident into a crisis.
A CPS defines your revocation timelines, your notification procedures, your escalation paths, and your recovery processes. Without it, you're making critical decisions under pressure with no playbook.
People Leave. Documentation Stays.
Every organization has that one PKI person — the one who set up ADCS five years ago and knows where all the bodies are buried. What happens when they leave?
Research consistently shows that only 45% of organizations have sufficient staff dedicated to PKI deployment. The knowledge is concentrated in too few people, and when those people move on, the institutional knowledge walks out the door. A CP/CPS is how you capture that knowledge in a form that survives personnel changes.
Who Specifically Needs This?
Let's get concrete about which organizations should have CP/CPS documentation:
Any organization running Microsoft ADCS — You're running a Certificate Authority. Act like it. Document your certificate templates, issuance procedures, revocation policies, and key management practices.
Financial institutions — Banks, credit unions, insurance companies. PCI DSS requires documented cryptographic key management procedures. Your examiners expect it. Your risk committee should demand it.
Healthcare organizations — If you're using certificates for EHR authentication, clinical system access, or device identity, HIPAA's security rule expects you to have documented policies governing those credentials.
Government agencies and contractors — Federal PKI participation requires it. FedRAMP assessments expect it. Even if you're not cross-certifying with the Federal Bridge, NIST guidance applies to you.
IoT manufacturers and operators — If you're issuing device certificates at scale, your customers and partners need assurance that you have documented practices governing issuance, revocation, and key protection.
Any organization with more than a handful of internal certificates — The Keyfactor research found the average org manages 81,000+ internally trusted certificates. At that scale, undocumented PKI isn't just risky — it's negligent.
The RFC 3647 Framework Makes This Easier Than You Think
Here's the good news: you don't need to invent a structure from scratch.
RFC 3647 defines a nine-section framework that every CPS follows — from DigiCert's hundred-page document down to a small enterprise's internal policy. The sections cover:
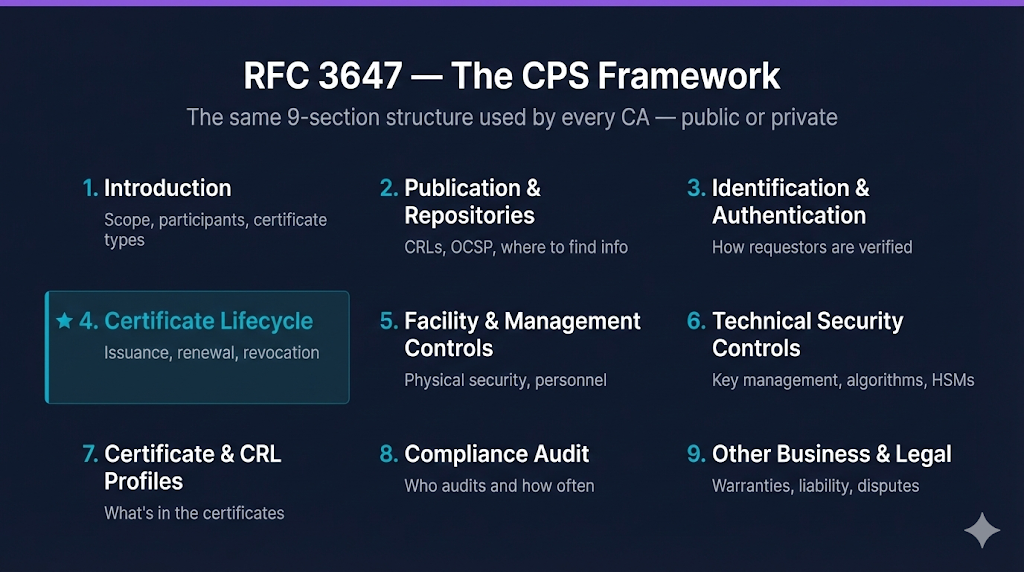
1. Introduction — Scope, participants, certificate types
2. Publication & Repositories — Where to find CRLs, OCSP endpoints
3. Identification & Authentication — How you verify certificate requestors
4. Certificate Lifecycle — Issuance, renewal, revocation procedures
5. Facility & Management Controls — Physical security, personnel controls
6. Technical Security Controls — Key management, algorithms, HSMs
7. Certificate & CRL Profiles — What's in the certificates you issue
8. Compliance Audit — Who audits and how often
9. Other Business & Legal — Warranties, liability, disputes
For a public CA, every section is heavily detailed. For your enterprise, some sections might just say "No stipulation" — and that's fine. The framework is designed to be adaptable. The point is that you've thought through each area and documented your decisions.
The beauty of this standardized structure is that it makes your documentation comparable to any other organization's. When auditors see RFC 3647 format, they know exactly where to find what they're looking for.
What "Good" Looks Like
A solid enterprise CP/CPS doesn't need to be a hundred pages. It needs to answer these questions clearly:
Certificate Issuance: Who can request certificates? What approval process exists? What certificate types do you support? What validation do you perform?
Key Management: Where are CA keys stored? How are they protected? Who has access? What happens during a key ceremony?
Revocation: When do you revoke certificates? How quickly? Who can request revocation? How do you distribute revocation information?
Roles and Responsibilities: Who administers the CA? Who audits it? Is there separation of duties? What happens when personnel change?
Disaster Recovery: What if the CA is compromised? What if the HSM fails? What's your backup and restoration process?
Audit and Compliance: How do you verify your own compliance? How often? Who reviews the results?
If you can answer these questions in a structured, RFC 3647-aligned document, you're ahead of the vast majority of enterprise PKI operators.
Stop Going Into Audits Empty-Handed
The compliance gap in enterprise PKI governance is real, it's widespread, and it's getting more consequential as certificate volumes grow and lifespans shrink. The organizations that figure this out now will have a massive advantage when auditors come knocking — or when the next incident hits.
We built Compliance-in-a-Box specifically for this problem. It includes four PKI compliance document templates:
Certificate Policy template — RFC 3647-structured, ready to customize for your organization's specific requirements and risk profile
Certificate Practice Statement template — Detailed operational procedures documentation covering all nine RFC 3647 sections
Key Ceremony Script — Step-by-step procedures for CA key generation with proper multi-party controls and audit trail
Audit Checklist — Comprehensive review checklist aligned to your CP/CPS commitments
All four documents are structured per RFC 3647 and designed to be customized — not generic boilerplate, but professional starting points that save you weeks of work compared to writing from scratch.
Want to Learn More?
- What is a CPS? — Our complete guide to Certificate Practice Statements
- PKI Compliance Hub — Track CA/Browser Forum deadlines and browser root program policies
- PKI Compliance Checklist — Quick-reference checklist for PKI compliance requirements
Sources: Keyfactor/Ponemon Institute — 2019 Impact of Unsecured Digital Identities, 2021 State of Machine Identity Management; Keyfactor/Vanson Bourne — 2024 PKI & Digital Trust Report (1,200 respondents across 11 industries); Microsoft Learn — Securing PKI: PKI Process Security; AWS — Private CA Best Practices; Entrust/Ponemon — 2022 Global PKI and IoT Trends Study (2,500+ respondents, 17 countries).
Related FixMyCert Resources
What is a CPS?
Our complete guide to Certificate Practice Statements and the RFC 3647 framework.
Explore GuideCompliance-in-a-Box
Audit-ready CP/CPS templates, key ceremony script, and audit checklist.
Explore GuidePKI Compliance Checklist
Quick-reference checklist for PKI compliance requirements.
Explore