Why Two-Tier?
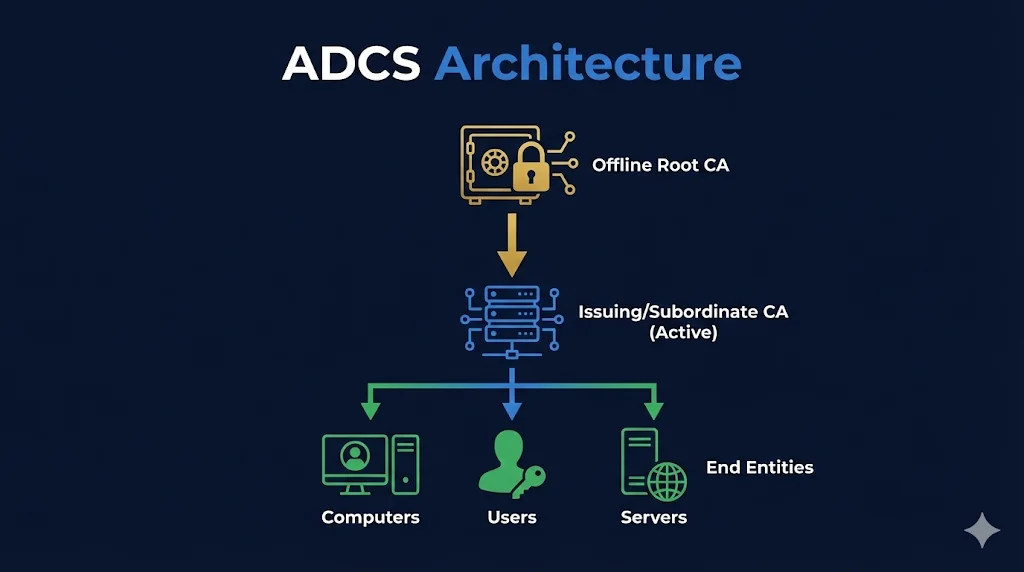
A properly designed ADCS deployment uses a two-tier hierarchy: an offline Root CA that stays powered off (protected), and an online Issuing CA that handles day-to-day certificate operations.
The Root CA's private key is the "master key" to your entire PKI. If compromised, every certificate in your organization is suspect.
| One-Tier (Bad) | Two-Tier (Good) |
|---|---|
| Root CA online, issuing certs | Root CA offline, in a safe |
| Root key exposed to network | Root key air-gapped |
| Compromise = game over | Compromise issuing CA = reissue from root |
| Simple but risky | More work but recoverable |
Architecture Diagram
Click on any component to learn more about it:
Additional Components
CDP/AIA (CRL Distribution Points / Authority Information Access)
Where CRLs and CA certificates are published. Usually HTTP and LDAP locations that clients check to verify certificate revocation status.
OCSP Responder
Optional component for real-time revocation checking. Faster than downloading CRLs, but adds infrastructure complexity.
NDES (Network Device Enrollment Service)
SCEP protocol support for network devices. Allows routers, switches, and mobile devices to request certificates without Active Directory. Learn more →
Web Enrollment
Browser-based certificate requests. Useful for manual enrollment when autoenrollment isn't appropriate. Note: Can be a security risk (see ESC8 attack).
Enterprise vs Standalone CA
| Feature | Enterprise CA | Standalone CA |
|---|---|---|
| Active Directory | Requires AD DS | No AD required |
| Templates | Uses templates | No templates |
| Autoenrollment | Supported | Manual only |
| Best For | Issuing CA | Root CA |
Best Practice: Use a Standalone CA for your offline Root (no AD dependency), and an Enterprise CA for your Issuing CA (enables templates and autoenrollment).
Next Steps
Related Resources
What is ADCS?
Introduction to Active Directory Certificate Services and when to use it.
Certificate Templates
Learn how templates define certificate properties and permissions.
Autoenrollment
Configure automatic certificate deployment via Group Policy.
ADCS Security
Understand ESC attacks and how to secure your PKI infrastructure.
CA Hierarchy Guide
Deep dive into Root CA, Subordinate CA, and chain of trust concepts.
Certificate Lifecycle
Understand the complete certificate lifecycle from issuance to renewal.