Back to Demos
8/54
FundamentalsAdvanced
TLS Cipher Suite Decoder
Decode cipher suite strings like TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384. Understand key exchange, encryption, and MAC.
Interactive Demo
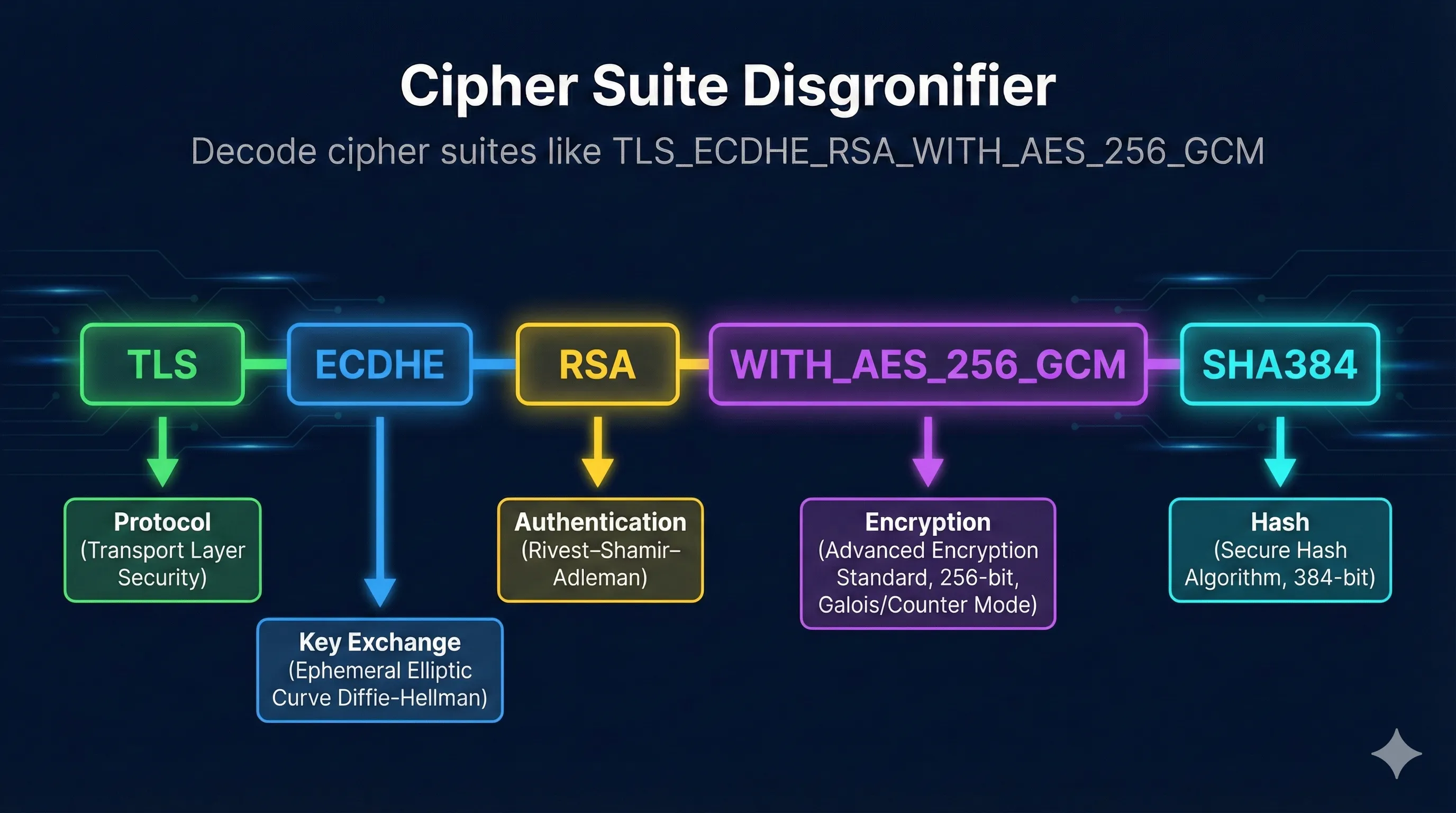
Cipher Suite Disgronifier
Break down intimidating cipher suite strings into understandable pieces
Step 0 of 6
The Disgronifier - break down cipher suites
The Disgronifier
TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
Security Rating: SECUREA
Forward Secrecy-ECDHE provides ephemeral keys
Strong Encryption-AES-256 is industry standard
AEAD Mode-GCM provides authenticated encryption
Strong Hash-SHA384 is collision-resistant
RSA Auth-Consider ECDSA for better performance
Recommended for: Production servers, general use
Component Deep Dives
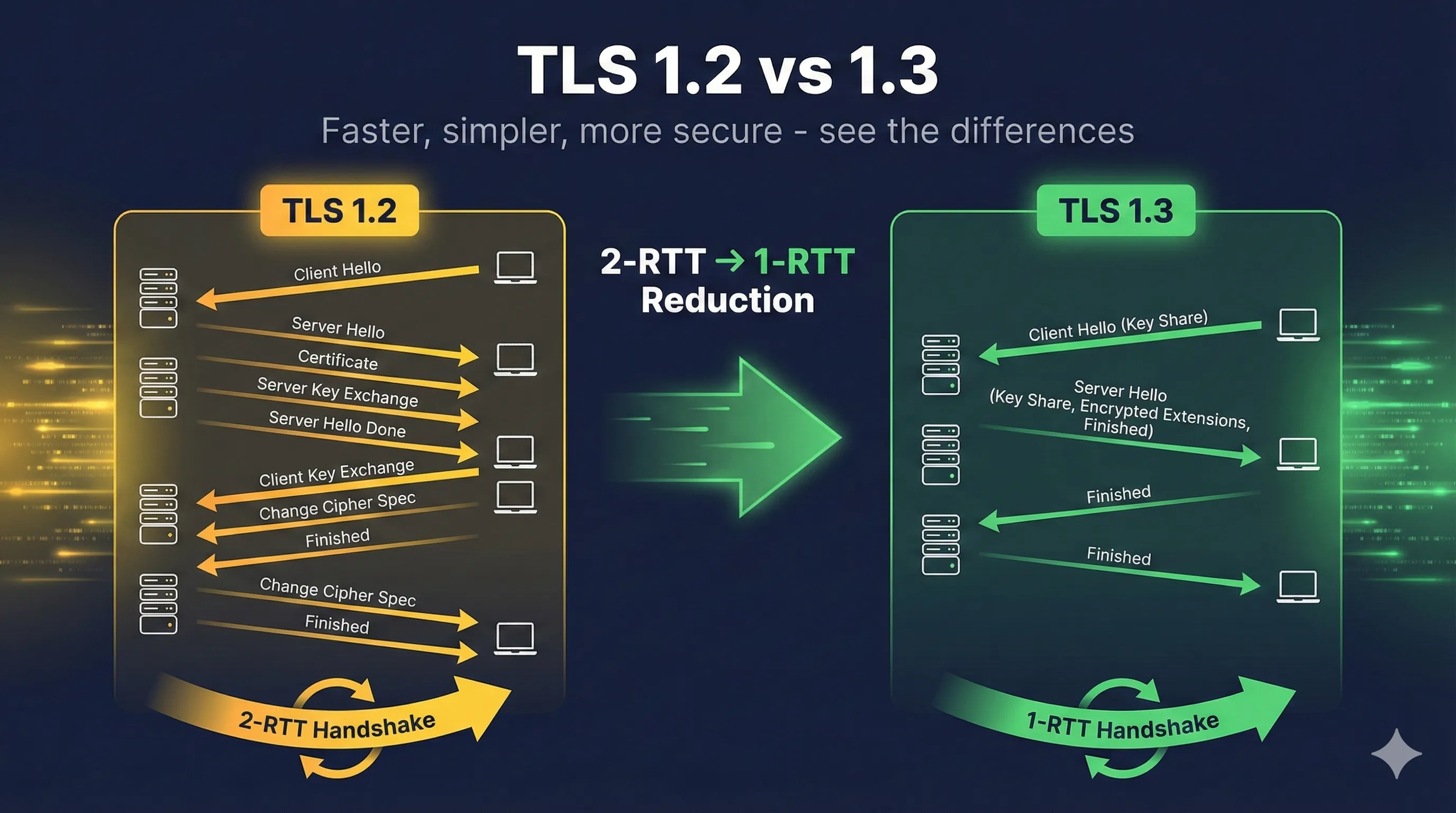
TLS 1.3 Simplified Format
TLS 1.2 Format (verbose):
TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
7 components to understand
TLS 1.3 Format (simplified):
TLS_AES_256_GCM_SHA384
Just cipher + hash! Key exchange is always ephemeral.
TLS 1.3 Only Allows:
TLS_AES_256_GCM_SHA384
AES-256, strongest
TLS_AES_128_GCM_SHA256
AES-128, faster
TLS_CHACHA20_POLY1305_SHA256
Great for mobile
TLS_AES_128_CCM_SHA256
IoT/constrained
Key Insight:TLS 1.3 removed all the bad options. You can't accidentally pick a weak cipher - they simply don't exist in TLS 1.3.
Recommended Server Configuration
Nginx (Modern)
ssl_protocols TLSv1.2 TLSv1.3; ssl_ciphers ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384; ssl_prefer_server_ciphers off;
Apache
SSLProtocol all -SSLv3 -TLSv1 -TLSv1.1 SSLCipherSuite ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384 SSLHonorCipherOrder off
Check Your Cipher Suites
# Test what cipher suites a server supports nmap --script ssl-enum-ciphers -p 443 example.com # OpenSSL test specific cipher openssl s_client -connect example.com:443 -cipher 'ECDHE-RSA-AES256-GCM-SHA384'
ASecure
BGood
CLegacy
DWeak
FBroken
Want to learn more?
Read our complete guide on understanding cipher suites