Back to Demos
1/54
FundamentalsBeginner
Encryption Fundamentals
Learn symmetric vs asymmetric encryption fundamentals. Interactive demo shows AES, RSA, and why TLS uses both.
Interactive Demo

Encryption Basics
Step 0 of 6
Ready to start
Alice
SHARED KEY
Bob
Advantages
- ✓ Fast: Extremely efficient (AES, ChaCha20).
- ✓ Low Overhead: Great for encrypting large files or streams.
Disadvantages
- ✗ Key Distribution: How do you send the key without it being stolen?
- ✗ Scalability: Need a unique key for every person you talk to.
The Best of Both Worlds: How TLS Does It
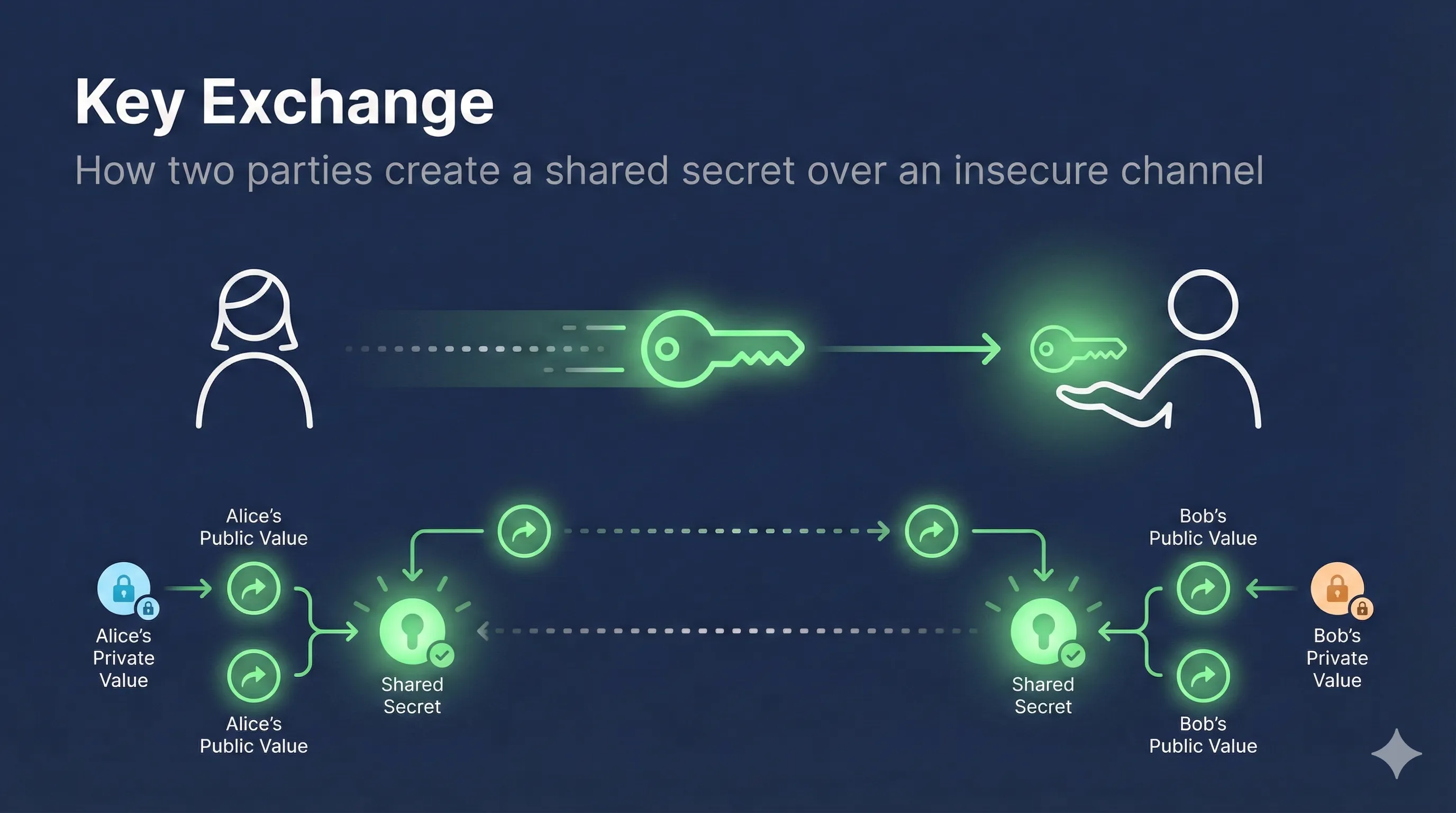
Problem: Symmetric is fast but hard to share keys. Asymmetric is safe but too slow.
Solution: Use Asymmetric encryption just once to exchange a Symmetric key. Then use that Symmetric key for the rest of the conversation.
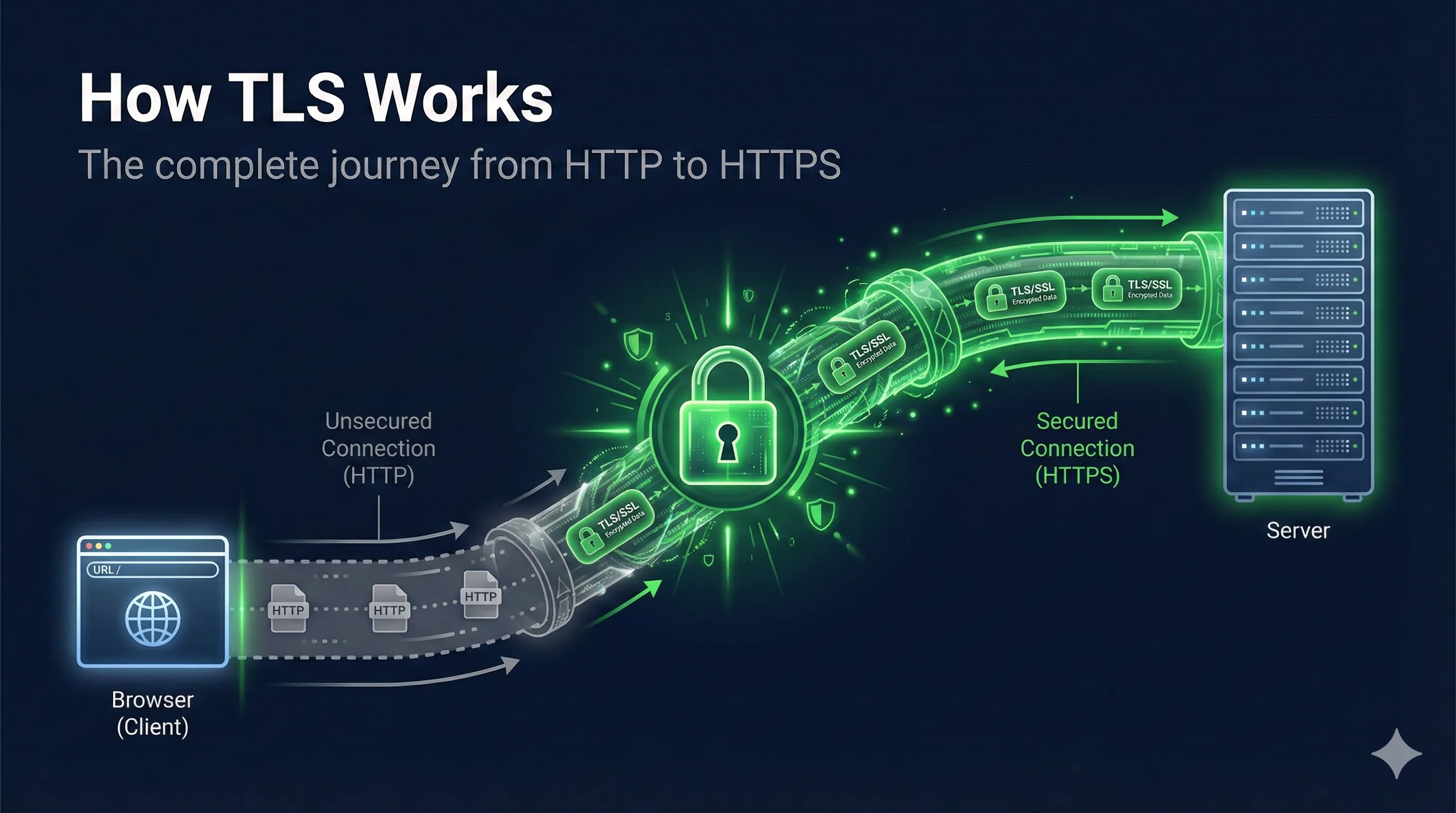
1. ClientHello (I support RSA/ECC)
2. ServerHello (Here is my Public Key)
3. Client Encrypts "Session Key" with Server's Public Key
4. Server Decrypts with Private Key
5. Both switch to AES-256 (Symmetric) using Session Key 🚀
2. ServerHello (Here is my Public Key)
3. Client Encrypts "Session Key" with Server's Public Key
4. Server Decrypts with Private Key
5. Both switch to AES-256 (Symmetric) using Session Key 🚀
Handshake
Asymmetric (Secure Key Exchange)
Data Transfer
Symmetric (Fast & Efficient)
Want to learn more?
Read our complete guide on symmetric vs asymmetric encryption