Quick Answer: What is a Cipher Suite?
A cipher suite is a set of cryptographic algorithms that work together to secure a TLS connection. It specifies how your data will be protected, including key exchange, authentication, encryption, and integrity verification.
The cipher suite you choose directly impacts your security. Using weak or outdated cipher suites can leave your connections vulnerable to attacks.
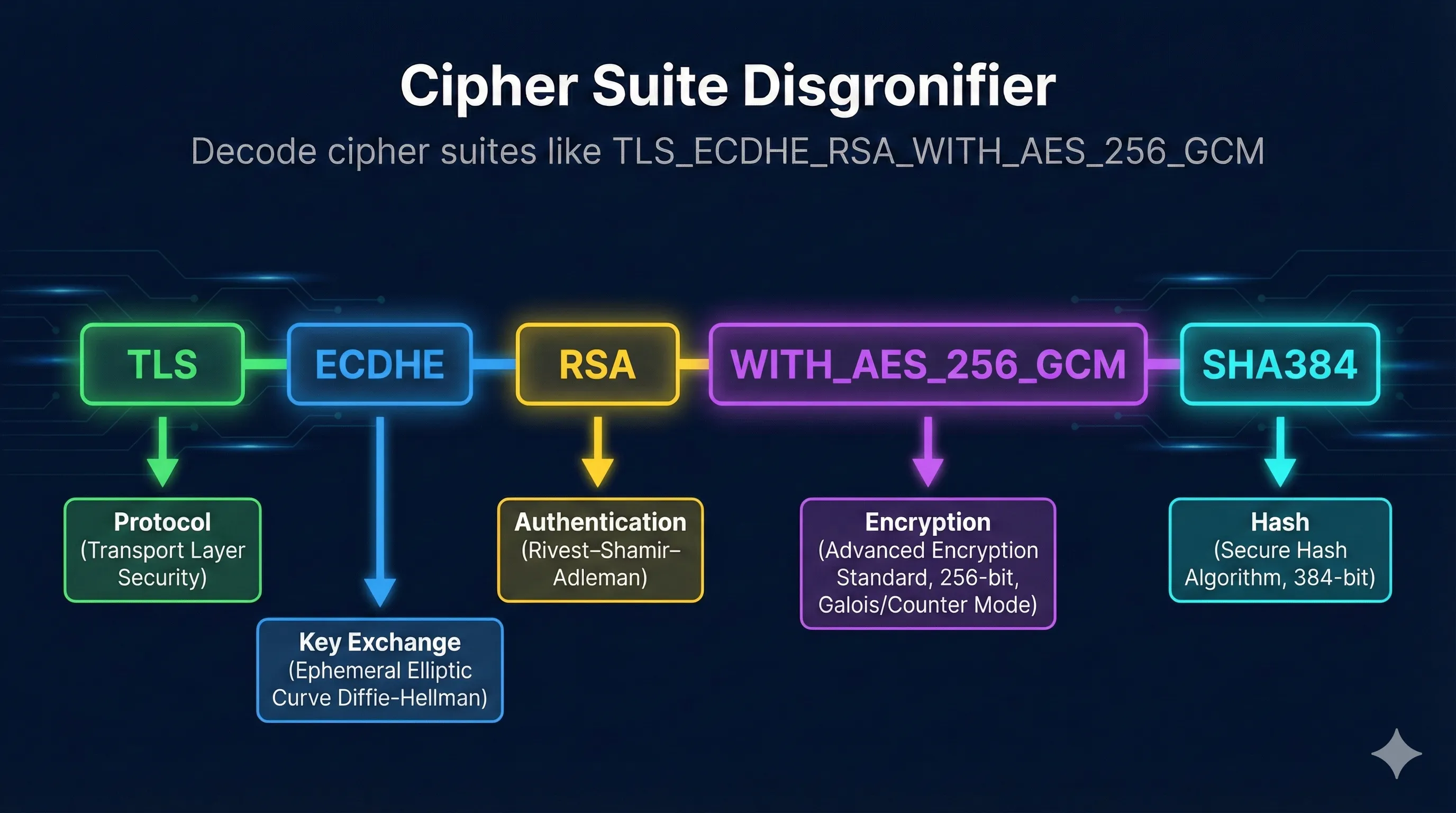
Anatomy of a Cipher Suite String
Let's break down the components of a typical TLS 1.2 cipher suite string:
Key Exchange Algorithms
The key exchange algorithm determines how both parties securely agree on a shared secret for encrypting the session. This is the most critical component for forward secrecy.
| Algorithm | Forward Secrecy | Security | Recommendation |
|---|---|---|---|
| ECDHE | Yes | Strong | Best choice - use this |
| DHE | Yes | Good (if 2048+ bit) | Acceptable, but slower than ECDHE |
| RSA | No | Weak | Avoid - no forward secrecy |
| PSK | Depends | Depends | For IoT and constrained devices |
What is Forward Secrecy?
Forward secrecy ensures that if an attacker later obtains your server's private key, they still cannot decrypt past sessions. ECDHE (Ephemeral) generates new keys for each session, so there's no long-term secret to compromise.
Authentication Methods
The authentication component specifies how the server proves its identity to the client using its certificate.
| Method | Key Size | Performance | Notes |
|---|---|---|---|
| RSA | 2048-4096 bits | Slower signatures | Most common, widely supported |
| ECDSA | 256-384 bits | Faster signatures | Modern, smaller keys, same security |
| Ed25519 | 256 bits | Fastest | Newer, not yet widely adopted in TLS |
Encryption Algorithms
The encryption algorithm (symmetric cipher) protects the actual data being transmitted. This is where the "fast" encryption happens after the handshake.
| Cipher | Key Sizes | Security | Notes |
|---|---|---|---|
| AES-256 | 256 bits | Strong | Industry standard, hardware accelerated |
| AES-128 | 128 bits | Strong | Slightly faster, still very secure |
| ChaCha20 | 256 bits | Strong | Great for mobile (no AES hardware) |
| 3DES | 168 bits | Weak | Deprecated - Sweet32 attack |
| RC4 | 40-256 bits | Broken | NEVER USE - multiple attacks |
Cipher Modes (GCM vs CBC)
The cipher mode determines how the encryption algorithm is applied to data. This is crucial for security.
GCM (Galois/Counter Mode)
- AEAD (Authenticated Encryption)
- Built-in integrity protection
- Parallelizable (fast)
- No padding oracle risks
Recommended - use this
CBC (Cipher Block Chaining)
- Needs separate MAC
- Padding oracle vulnerabilities
- Sequential (slower)
- BEAST, Lucky 13 attacks
Legacy - prefer GCM
What is AEAD?
Authenticated Encryption with Associated Data (AEAD) combines encryption and integrity checking in one operation. GCM and ChaCha20-Poly1305 are AEAD modes. They ensure data hasn't been tampered with during transmission.
Hash Functions
The hash function is used for key derivation and message authentication (in non-AEAD modes).
| Hash | Output Size | Status |
|---|---|---|
| SHA384 | 384 bits | Strong - recommended |
| SHA256 | 256 bits | Strong - widely used |
| SHA-1 | 160 bits | Deprecated |
| MD5 | 128 bits | Broken - never use |
TLS 1.3 Cipher Suites
TLS 1.3 simplified cipher suites significantly. Key exchange is now built into the protocol (always ECDHE or DHE), and only AEAD ciphers are allowed.
TLS 1.3 Cipher Suite Format
Notice: No key exchange or authentication in the name! TLS 1.3 always uses ephemeral Diffie-Hellman for forward secrecy, so it's not specified in the cipher suite.
Available TLS 1.3 Cipher Suites
| Cipher Suite | Use Case |
|---|---|
| TLS_AES_256_GCM_SHA384 | General purpose, maximum security |
| TLS_AES_128_GCM_SHA256 | General purpose, slightly faster |
| TLS_CHACHA20_POLY1305_SHA256 | Mobile devices, no AES hardware |
Recommended Configurations
Modern Configuration (TLS 1.3 + TLS 1.2)
# Nginx - Modern configuration ssl_protocols TLSv1.2 TLSv1.3; ssl_ciphers ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305; ssl_prefer_server_ciphers off;
Apache Configuration
# Apache - Modern configuration SSLProtocol all -SSLv3 -TLSv1 -TLSv1.1 SSLCipherSuite ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305 SSLHonorCipherOrder off
Cipher Suites to Avoid
- *_RSA_* (RSA key exchange) - No forward secrecy
- *_CBC_* - Padding oracle vulnerabilities
- *_3DES_* - Sweet32 attack
- *_RC4_* - Broken, multiple attacks
- *_SHA (SHA-1) - Deprecated hash
- *_MD5_* - Broken hash
- *_EXPORT_* - Weak export ciphers
- *_NULL_* - No encryption
Testing Server Cipher Suites
Using OpenSSL
# See which cipher suite was negotiated openssl s_client -connect example.com:443 </dev/null 2>/dev/null | grep "Cipher" # List all supported ciphers openssl s_client -connect example.com:443 -cipher 'ALL' 2>/dev/null | grep "Cipher" # Test a specific cipher suite openssl s_client -connect example.com:443 -cipher 'ECDHE-RSA-AES256-GCM-SHA384' # List available TLS 1.3 ciphers openssl ciphers -v -s -tls1_3
Using nmap
# Enumerate all supported cipher suites nmap --script ssl-enum-ciphers -p 443 example.com
Online Tools
- SSL Labs: ssllabs.com/ssltest - Comprehensive server analysis
- testssl.sh: Command-line tool for detailed analysis
Related Resources
How TLS Works
Understand how cipher suites are negotiated in the handshake.
TLS Version Comparison
How cipher suites differ between TLS 1.2 and TLS 1.3.
Encryption Basics
Learn about AES, ChaCha20, and symmetric encryption.
Forward Secrecy
Why ECDHE cipher suites are essential for security.
Hash Functions
Understand the MAC algorithms used in cipher suites.
RSA vs ECC
Compare authentication algorithms in cipher suites.
Encrypted Client Hello (ECH)
ECH encrypts the ClientHello that carries cipher suite preferences — the next evolution of TLS privacy.
Frequently Asked Questions
Should I prefer AES-128 or AES-256?
Both are secure for the foreseeable future. AES-128 is slightly faster, while AES-256 provides a larger security margin. For most applications, either is fine. If you're concerned about quantum computing, AES-256 offers more resistance.
What's the difference between ECDHE and DHE?
Both provide forward secrecy, but ECDHE (Elliptic Curve) is faster and uses smaller keys for equivalent security. A 256-bit ECDHE key provides roughly the same security as a 3072-bit DHE key. Prefer ECDHE unless you have specific compatibility requirements.
Why is RSA key exchange bad?
RSA key exchange encrypts the pre-master secret with the server's public key. If an attacker later obtains the server's private key (through a breach, court order, or cryptanalysis), they can decrypt all recorded past sessions. ECDHE generates fresh keys each session, so even a compromised private key can't decrypt old traffic.
When should I use ChaCha20 instead of AES?
ChaCha20-Poly1305 is ideal for devices without AES hardware acceleration (like many mobile and IoT devices). On desktop/server CPUs with AES-NI instructions, AES-GCM is typically faster. Many servers are configured to prefer ChaCha20 for mobile clients and AES for desktop clients.
Should I set ssl_prefer_server_ciphers?
With modern configurations, setting this to "off" is often recommended. This allows clients to choose their preferred cipher, which may be optimized for their hardware (e.g., ChaCha20 on mobile). Only enable server preference if you have legacy clients that might negotiate weak ciphers.
Want to go deeper?
Cipher suites are just one piece of the TLS puzzle. If you want to understand how they fit into the bigger picture—with real packet analysis—I highly recommend Practical TLS by Ed Harmoush. It's the most comprehensive TLS course available—with real Wireshark captures, hands-on labs, and explanations that actually make sense.
Disclosure: I earn a commission if you purchase through this link, at no extra cost to you.
Decode Any Cipher Suite
Use our interactive tool to break down any cipher suite string and understand its security rating, components, and recommendations.
Launch Cipher Suite Decoder