Back to Demos
9/54
FundamentalsAdvanced
TLS Version Comparison
Compare TLS 1.0, 1.1, 1.2, and 1.3. Understand security improvements and migration requirements.
Interactive Demo
TLS 1.2 vs TLS 1.3 Comparison
Understanding why TLS 1.3 is faster and more secure
Step 0 of 7
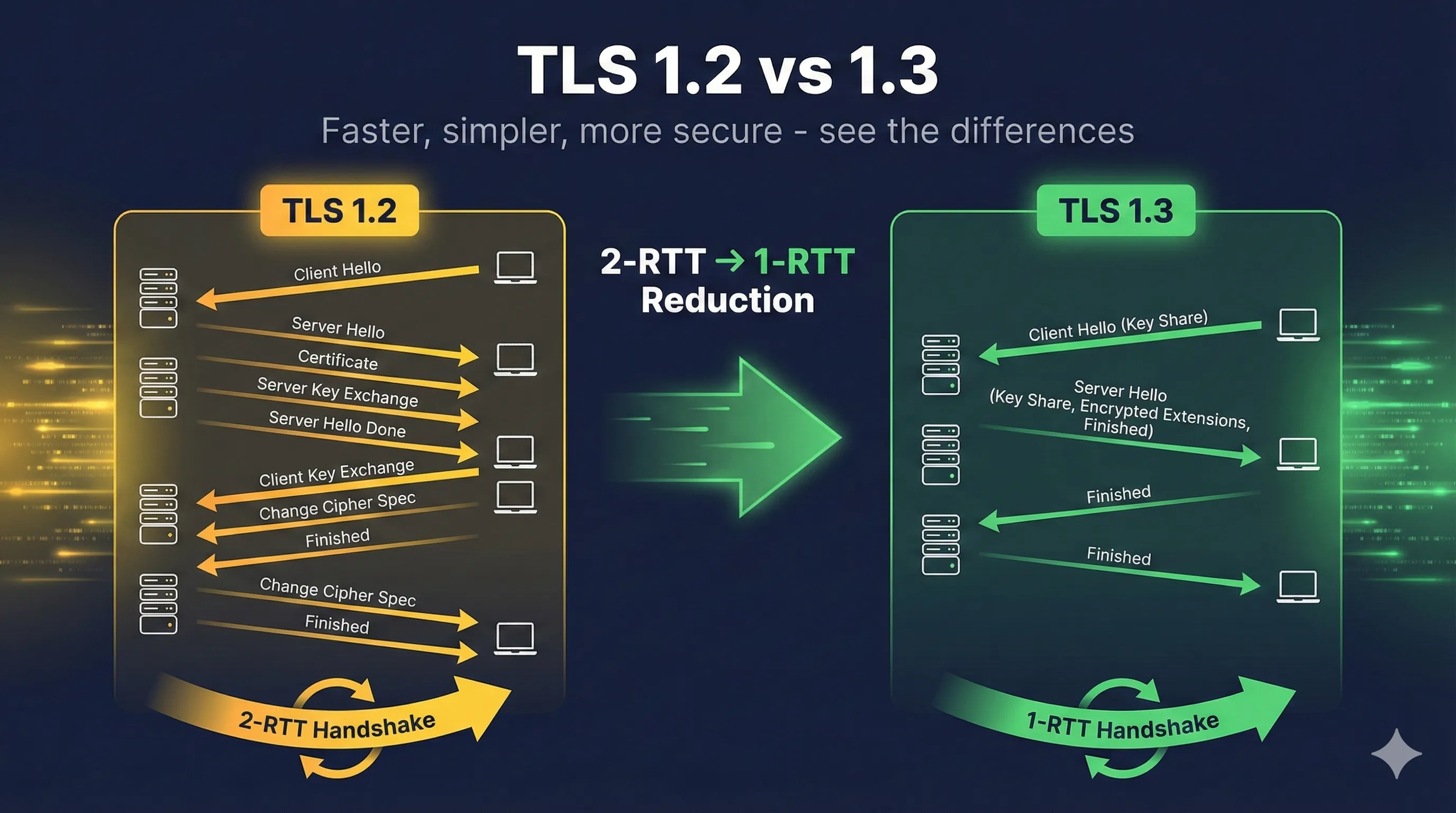
The big picture - TLS 1.2 vs 1.3
NOW VIEWING
The Big Picture
TLS 1.2 (2008)
Handshake:2 round trips
Cipher suites:300+ options (many weak)
Forward secrecy:Optional
0-RTT:Not supported
RSA key exchange:Allowed
Legacy algorithms:Supported (RC4, 3DES, MD5...)
TLS 1.3 (2018)
Handshake:1 round trip
Cipher suites:5 options (all strong)
Forward secrecy:MANDATORY
0-RTT:Supported (resumption)
RSA key exchange:REMOVED
Legacy algorithms:GONE (only modern crypto)
Key Insight:TLS 1.3 isn't just 'newer' - it's a fundamental redesign. Faster handshakes, mandatory security features, and no way to accidentally configure it wrong.
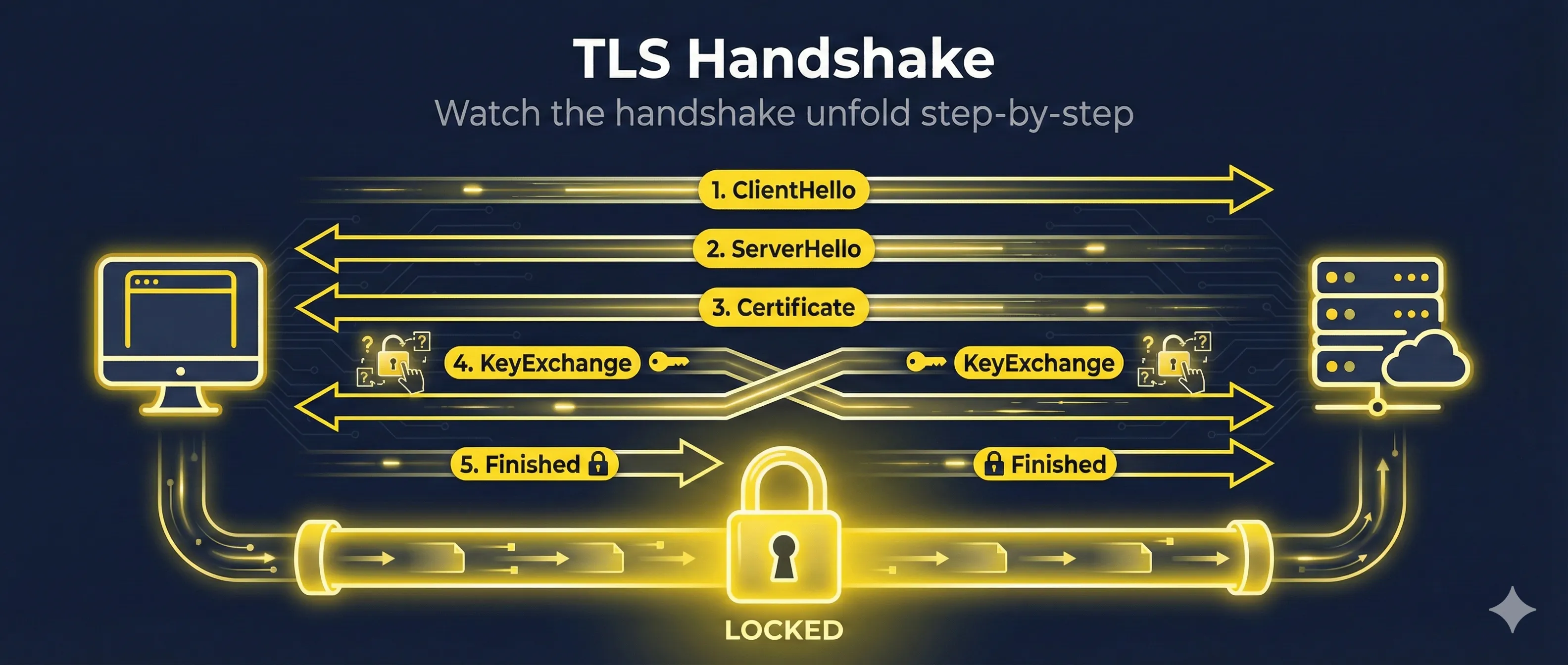
Handshake Comparison
TLS 1.2 Handshake - 2 Round Trips
Client
ClientHello
ServerHello, Cert, KeyExchange
--- Round Trip 1 ---
ClientKeyExch, Finished
ChangeCipherSpec, Finished
--- Round Trip 2 ---
Encrypted Data
Server
Total latency: ~100-300ms depending on distance
Loading a webpage (10 HTTPS resources):
TLS 1.22000ms
TLS 1.31200ms (-40%!)
TLS 1.3 + 0-RTT900ms (-55%!)
What Got Removed (Security Improvements)
| Removed | Why | Risk It Posed |
|---|---|---|
| RSA key exchange | No forward secrecy | Past traffic decryptable if key stolen |
| Static DH | No forward secrecy | Same problem as RSA |
| RC4 | Broken cipher | Multiple practical attacks |
| 3DES | 64-bit blocks | Sweet32 attack |
| MD5 | Broken hash | Collision attacks |
| SHA-1 | Weak hash | Collision attacks demonstrated |
| CBC mode ciphers | Complex, error-prone | BEAST, Lucky13, Padding oracles |
| Export ciphers | Intentionally weak | FREAK, Logjam attacks |
| Compression | Side channel | CRIME, BREACH attacks |
| Renegotiation | Complex, buggy | Multiple vulnerabilities |
What's left in TLS 1.3:
Key Exchange: ECDHE or DHE (forward secrecy required!)
Authentication: Certificates (RSA or ECDSA signatures)
Encryption: AES-GCM, AES-CCM, or ChaCha20-Poly1305
Hash: SHA-256 or SHA-384
That's it. No weak options exist.
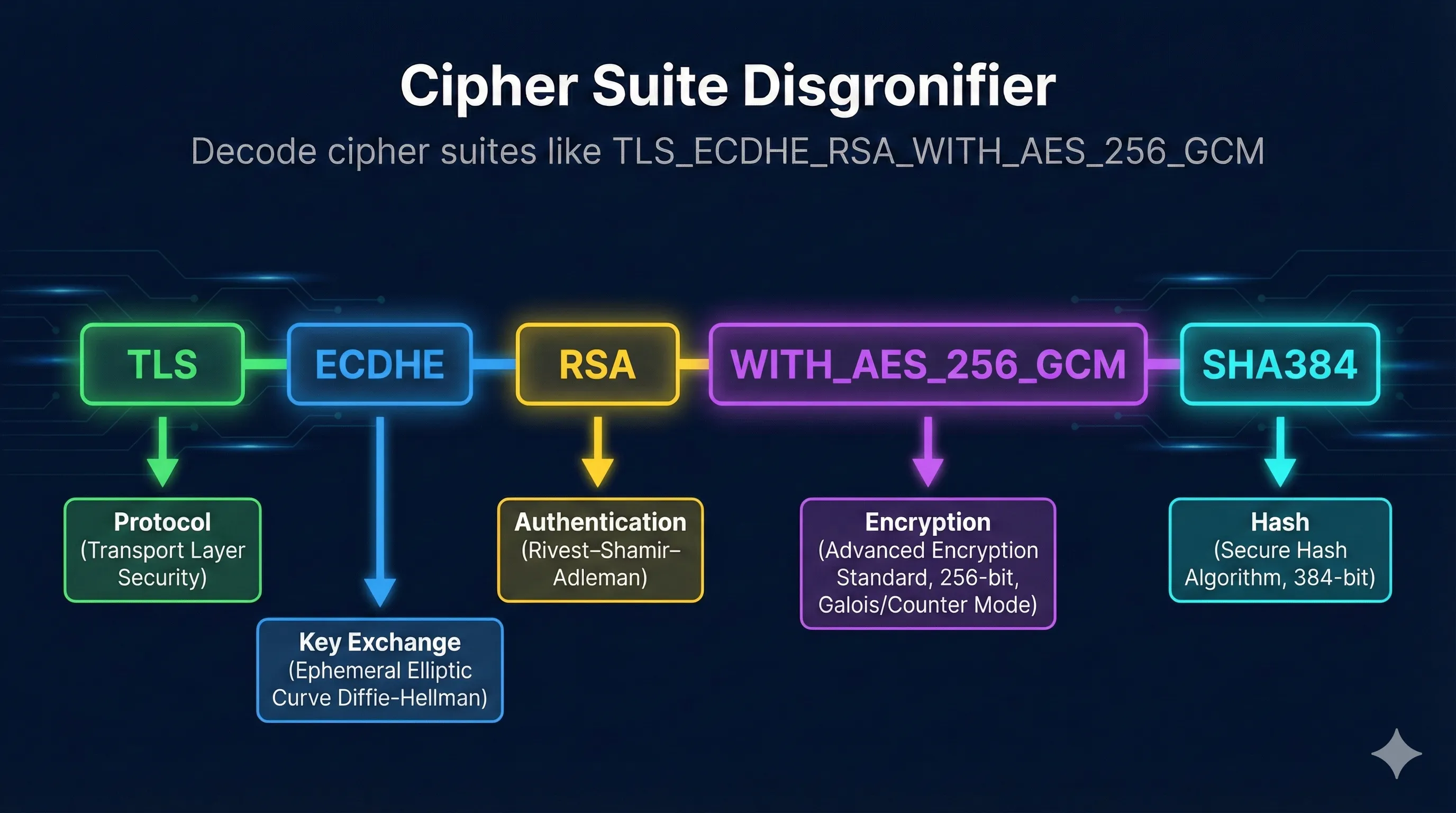
Cipher Suite Comparison
TLS 1.2 - Too Many Choices (300+)
TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
Recommended
TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256
Fast, modern
TLS_RSA_WITH_AES_256_CBC_SHA256
No forward secrecy
TLS_DHE_RSA_WITH_AES_256_CBC_SHA
CBC mode
TLS_RSA_WITH_3DES_EDE_CBC_SHA
Weak cipher
TLS_RSA_WITH_RC4_128_SHA
Broken!
Problem: Easy to misconfigure. Weak ciphers still negotiated.
TLS 1.3 - Only 5 Options (All Secure!)
TLS_AES_256_GCM_SHA384
AES-256, strongest
TLS_AES_128_GCM_SHA256
AES-128, fast
TLS_CHACHA20_POLY1305_SHA256
Great for mobile
TLS_AES_128_CCM_SHA256
IoT/constrained
TLS_AES_128_CCM_8_SHA256
IoT, truncated tag
That's the complete list. Every option is secure.
Key Insight:In TLS 1.3, there's no 'cipher suite configuration' to mess up. All options are good. You literally cannot pick a weak cipher.
More Encryption, Sooner
TLS 1.2 - Certificate Sent in Clear
ClientHello🔓 Plaintext
ServerHello🔓 Plaintext
Certificate🔓 Plaintext ← Visible!
ServerKeyExchange🔓 Plaintext
ClientKeyExchange🔓 Plaintext
Finished🔒 Encrypted
Application Data🔒 Encrypted
Network observers can see which certificate (website) you're connecting to.
TLS 1.3 - Certificate Encrypted
ClientHello🔓 Plaintext
ServerHello🔓 Plaintext
EncryptedExtensions🔒 Encrypted
Certificate🔒 Encrypted ← Hidden!
CertificateVerify🔒 Encrypted
Finished🔒 Encrypted
Application Data🔒 Encrypted
Certificate is encrypted. More privacy.
Check & Configure TLS Versions
Check what a server supports
# Check TLS version with OpenSSL openssl s_client -connect example.com:443 -tls1_3 # Detailed check with nmap nmap --script ssl-enum-ciphers -p 443 example.com
Nginx - Enable TLS 1.3
ssl_protocols TLSv1.2 TLSv1.3; ssl_prefer_server_ciphers off;
Apache - Enable TLS 1.3
SSLProtocol all -SSLv3 -TLSv1 -TLSv1.1 # TLS 1.2 and 1.3 only
Should You Upgrade?
All modern browsers support TLS 1.3 (Chrome, Firefox, Safari, Edge)
All major cloud providers support TLS 1.3
OpenSSL 1.1.1+ supports TLS 1.3
Some old clients (IE, old Android) may need TLS 1.2 fallback
TLS 1.2 (2008) - 2 round trips
TLS 1.3 (2018) - 1 round trip
0-RTT - Zero latency resumption
Read the Complete TLS 1.2 vs 1.3 Guide
Deep dive into handshake differences, 0-RTT, removed features, and migration tips