Why This Guide Exists
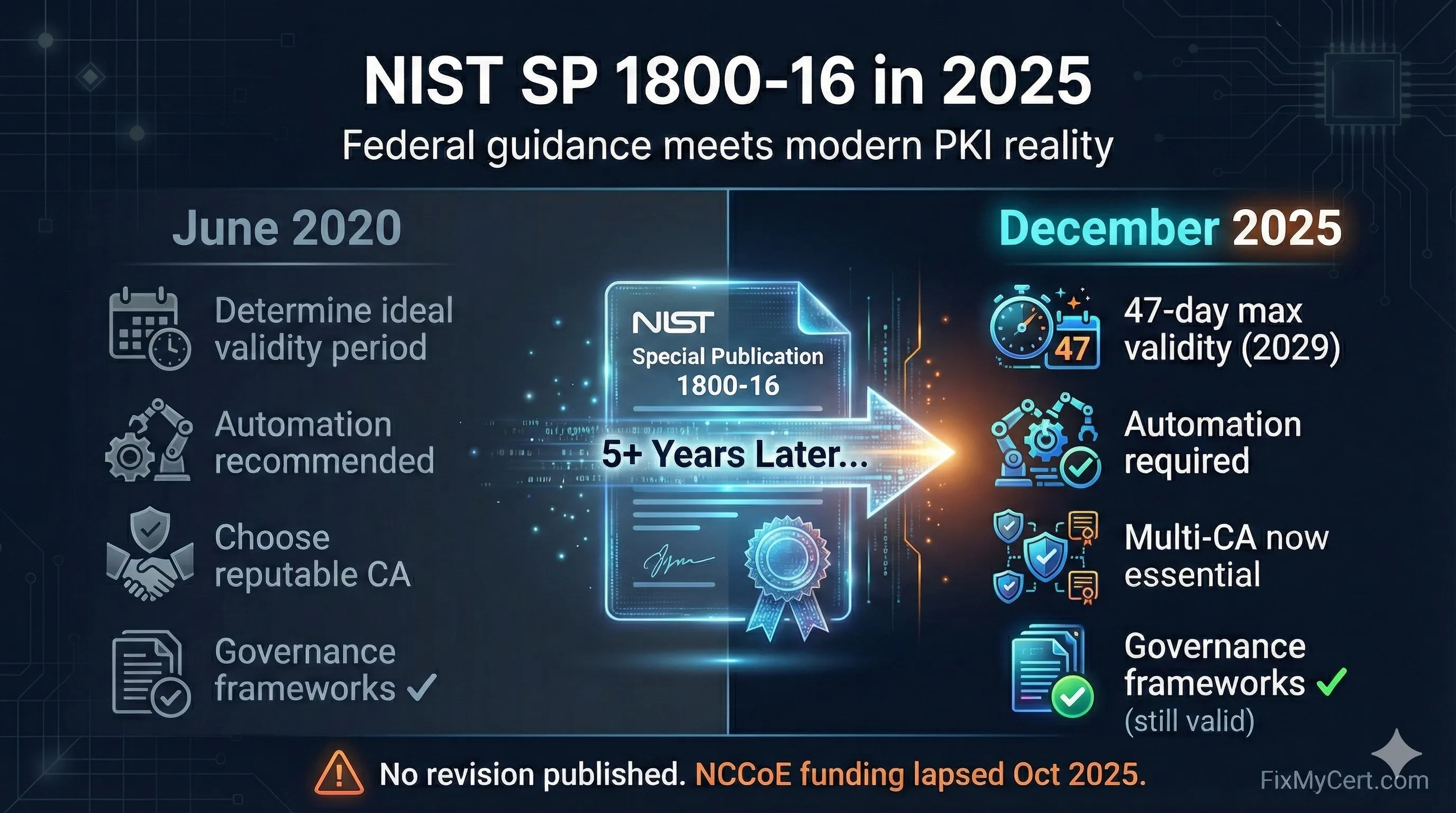
NIST Special Publication 1800-16, "Securing Web Transactions: TLS Server Certificate Management," was published June 16, 2020. It remains the most comprehensive federal guidance on enterprise certificate management.
The problem: 77 days after publication, the CA/Browser Forum enforced 398-day maximum certificate validity. The guidance was outdated before most organizations could implement it.
Five and a half years later:
- The NCCoE website states: "October 1, 2025: Due to a lapse in federal funding, this website is not being updated"
- No revision has been published
- No successor document exists from NIST, CISA, NSA, or any federal agency
- The PKI landscape has fundamentally changed
This guide maps what's still valid, what's outdated, and what practitioners need to know in 2025.
Important: This is a companion guide, not a replacement. NIST SP 1800-16's governance frameworks, risk models, and SP 800-53 control mappings remain excellent foundations.
Document Verification
| Verification Item | Status | Source |
|---|---|---|
| NIST SP 1800-16 Final | June 16, 2020 | csrc.nist.gov |
| Revisions Published | None | NIST CSRC |
| Successor Documents | None | NIST, CISA, NSA, OMB, DoD |
| NCCoE Project Status | Dormant (funding lapse) | nccoe.nist.gov |
| Verification Date | December 16, 2025 | FixMyCert research |
If you're aware of updated guidance we missed, please contact us. We commit to updating this guide within 48 hours of any successor publication.
Understanding the NIST Ecosystem
SP 800-53 Rev. 5 = WHAT to implement
- 1,000+ security controls across 20+ families
- Required for FISMA, FedRAMP compliance
- Certificate management: SC-8, SC-12, SC-13, SC-17, CM-2, CM-3, CM-8, IA-5, IA-9
SP 1800-16 = HOW to implement
- Vendor-specific examples
- Lab builds and configurations
- Mapping to 800-53 controls
The value: SP 1800-16's control mappings remain valid. The implementation details need updating.
What Still Applies
The Four Core Risks (Volume B)
NIST identified four risks that remain completely valid:
Outages from expired certificates
Still the #1 certificate incident type. With 47-day certificates coming (2029), this risk multiplies.
Attacks from server impersonation
Fundamentals unchanged. 2025 addition: Certificate Transparency now provides detection capability.
Crypto-agility failures
NIST was prescient here. 2025 validation: Entrust distrust (2024) proved organizations without agility suffered.
Encrypted threat blindness
TLS inspection guidance still relevant. Must now account for CT logging of inspection certificates.
Governance Framework
The organizational recommendations remain excellent:
| NIST Recommendation | Still Valid? | 2025 Enhancement |
|---|---|---|
| Executive sponsorship | Yes | Add: Board-level reporting for CA distrust risk |
| Central certificate team | Yes | Add: Authority to force emergency replacements |
| Defined ownership | Yes | Add: Include automation method owner |
| Written policies | Yes | Add: Must address multi-CA strategy |
| Certificate inventory | Yes | Add: CT log monitoring, CAA records |
SP 800-53 Control Mappings
Volume C's mappings to SP 800-53 remain valid for compliance programs:
What's Outdated
Certificate Validity Periods
NIST SP 1800-16 says:
"Organizations should determine the ideal certificate validity period"
2025 Reality:
You don't determine anything. CA/Browser Forum mandates it.
| Date | Maximum Validity | Source |
|---|---|---|
| Pre-Sep 2020 | 825 days | CA/B Forum |
| Sep 2020 | 398 days | Ballot SC-31 |
| March 15, 2026 | 200 days | Ballot SC-081 |
| March 15, 2027 | 100 days | Ballot SC-081 |
| March 15, 2029 | 47 days | Ballot SC-081 |
CA Trust Assumptions
NIST SP 1800-16 implies:
CAs in browser trust stores are reliable partners
2025 Reality:
Being in root programs ≠ staying there
| CA | What Happened | Year |
|---|---|---|
| DigiNotar | Hacked, fake Google certs, bankrupt | 2011 |
| WoSign/StartCom | Backdated certs, fully distrusted | 2016 |
| Symantec | Mass mis-issuance, sold to DigiCert | 2017 |
| Entrust | Pattern of compliance failures, distrusted | 2024 |
Essential practice: Multi-CA strategy is now essential. Single-CA reliance is considered an unacceptable business continuity risk after Entrust proved organizations can lose CA trust with months of warning but still struggle to switch.
Algorithm Guidance
| Algorithm | NIST 1800-16 Era | 2025 Status |
|---|---|---|
| RSA 2048 | Acceptable | Acceptable (3072+ recommended) |
| RSA 1024 | Deprecated | Disallowed |
| ECDSA P-256 | Acceptable | Preferred for performance |
| ECDSA P-224 | Acceptable | Deprecated (disallowed for TLS) |
| SHA-1 | Legacy use only | Disallowed for TLS |
| SHA-256 | Required minimum | Required minimum |
Automation Stance
NIST SP 1800-16 says:
Automation is "recommended" for efficiency
2025 Reality:
Automation is required for survival
| Certificate Validity | Renewals/Year | Manual Feasible? |
|---|---|---|
| 398 days | ~1 | Maybe |
| 200 days | ~2 | Difficult |
| 100 days | ~4 | No |
| 47 days | ~8 | Absolutely not |
What's New (Not in SP 1800-16)
Chrome Root Program Dominance
Not mentioned in SP 1800-16 because Chrome's Root Program launched in late 2020. Chrome has ~65% browser market share. When Chrome distrusts a CA, that CA is effectively dead for public TLS.
Chrome Root Program requirements now drive:
- Certificate Transparency enforcement
- Automation requirements for CAs
- Multi-purpose root phase-out
- Mass revocation capability requirements
Certificate Transparency Enforcement
SP 1800-16 mentions CT briefly. In 2025, CT is mandatory infrastructure.
| Requirement | Status |
|---|---|
| SCTs required for trust | Mandatory (Chrome, Apple, Mozilla) |
| CT log monitoring | Essential for detecting mis-issuance |
| Private CT logs | Emerging for internal PKI visibility |
CAA Records
Mentioned briefly in SP 1800-16. Now critical for CA-agility.
Why CAA matters in 2025:
- Prevents unauthorized CA issuance
- Required for rapid CA switching during distrust events
- Some organizations discovered during Entrust distrust they couldn't switch CAs because CAA blocked it
Domain Control Validation Changes
| Method | Status | Deadline |
|---|---|---|
| Email to domain contact | Sunset | July 15, 2025 |
| Email to WHOIS contact | Prohibited | Already in effect |
| HTTP-01 / DNS-01 | Preferred | Current standard |
| ACME automation | Recommended | Enables short-lived certs |
Multi-CA Strategy (Now Essential)
SP 1800-16 assumes a primary CA relationship. Real-world events prove explicit backup is essential for resilience.
Minimum Multi-CA Posture:
- Primary CA relationship established
- Backup CA relationship established (tested, not just contractual)
- CAA records authorize both CAs
- Automation supports both CAs
- Annual CA switchover drill completed
Updated Best Practices Matrix
| Area | NIST 1800-16 | 2025 Enhancement |
|---|---|---|
| Validity Period | "Determine ideal period" | Follow CA/B Forum mandates (47 days by 2029) |
| CA Selection | Choose reputable CA | Multi-CA strategy essential |
| Key Algorithm | RSA 2048 or ECDSA | ECDSA P-256/P-384 preferred; RSA 3072+ |
| Automation | Recommended | Required |
| Inventory | Maintain certificate list | Add: CT monitoring, CAA records |
| Discovery | Periodic network scans | Continuous discovery + CT monitoring |
| Revocation | Implement OCSP/CRL | Note: Chrome uses CRLSets |
| Incident Response | Have revocation process | Add: CA distrust playbook |
Implementation Checklist
30 Days: Foundation
- Identify executive sponsor for certificate management
- Assign central certificate team ownership
- Complete certificate inventory (include cloud, containers, IoT)
- Document current CA relationships
90 Days: Compliance
- Verify all certificates ≤398 days validity
- Audit and update CAA records
- Establish backup CA relationship
- Begin automation implementation for high-volume certificates
180 Days: Maturity
- Achieve 80%+ automation coverage
- Implement CT log monitoring
- Complete CA switchover drill
- Document incident response procedures for CA distrust
Ongoing
- Monitor CA/B Forum ballots (cabforum.org)
- Track Chrome Root Program updates
- Review CCADB for CA incidents
- Quarterly certificate posture reviews
Resources
NIST Sources
FixMyCert Tools
Industry Sources
About This Guide
This guide is an independent analysis by FixMyCert.com. We are not affiliated with NIST, NCCoE, or any government agency.
NIST SP 1800-16 remains an excellent foundational resource. Its governance frameworks, risk models, and SP 800-53 control mappings are still valuable. This companion guide addresses implementation details that have changed since June 2020.
Verification date: December 16, 2025
Sources checked: NIST CSRC, NCCoE, CISA, NSA, OMB, DoD
Next scheduled review: March 2026
Related Resources
Post-Quantum Cryptography
Preparing for quantum-resistant certificates
Crypto Agility vs Certificate Agility
Understanding PKI flexibility for compliance
PKI Compliance Hub
Industry standards and regulatory requirements
Encryption Basics
Foundation for understanding NIST crypto requirements
Cipher Suite Decoder
Verify your cipher suites meet NIST recommendations