Quick Answer: Why Are Wildcards Risky?
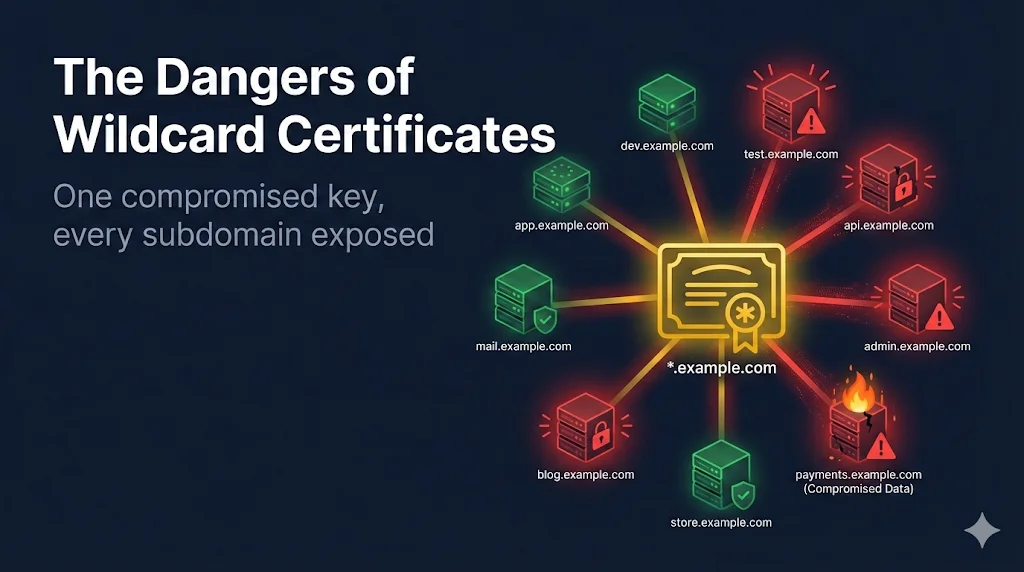
A wildcard certificate (*.example.com) covers unlimited subdomains with a single certificate and private key. While convenient, this creates significant security risks:
Danger 1: Massive Compromise Scope
When you use a wildcard certificate, every service on every subdomain shares the same private key. If an attacker compromises any one of these services, they can impersonate all of them.
Real-World Attack Scenario
- Attacker exploits vulnerability in dev.example.com
- Extracts private key from /etc/ssl/private/
- With the wildcard private key, creates fake www.example.com
- Performs man-in-the-middle attacks on production traffic
- Steals customer credentials, payment info, session tokens
Impact by Service Type
| Compromised Service | Can Now Impersonate | Risk Level |
|---|---|---|
| dev.example.com | www, api, mail, admin, shop | CRITICAL |
| staging.example.com | All production services | CRITICAL |
| blog.example.com | All business-critical services | CRITICAL |
Danger 2: Key Distribution Challenges
A wildcard certificate requires the same private key on every server that needs to terminate TLS for any subdomain. This creates multiple copies of your most sensitive cryptographic material.
Attack Surface Multiplication
With 10 servers using the same wildcard certificate, you have:
- 10 locations where the private key can be stolen
- 10 attack vectors for key extraction
- 10 server teams who need key access
- 10 servers to update during key rotation
Key Rotation Nightmare
When it's time to rotate keys (either routinely or after an incident), you must:
- Generate new private key and CSR
- Obtain new wildcard certificate from CA
- Deploy to ALL servers simultaneously
- Verify all services are working
- Securely delete old keys from ALL locations
# Checking for key copies across servers (security audit) for server in web1 web2 api1 api2 mail lb1 lb2; do ssh $server "find / -name '*.key' -o -name '*.pem' 2>/dev/null | wc -l" done
Danger 3: Revocation Cascade Effect
With individual certificates, you can revoke just the compromised service. With a wildcard, revoking the certificate brings down every serviceusing that certificate.
Incident Response Comparison
Individual Certificates
- 1. Revoke mail.example.com cert
- 2. Mail goes offline (expected)
- 3. Other services unaffected
- 4. Issue new mail cert at leisure
- Downtime: 1 service, minutes
Wildcard Certificate
- 1. Revoke *.example.com cert
- 2. ALL services go offline
- 3. Emergency cert reissuance
- 4. Deploy to ALL servers
- Downtime: All services, hours
Danger 4: Certificate Transparency Visibility
Certificate Transparency (CT) logs publicly record all issued certificates. While this provides valuable security monitoring, wildcards create a visibility tradeoff.
Wildcard Advantage
Attackers can't enumerate your subdomains by watching CT logs. They only see *.example.com, not your full infrastructure.
Wildcard Disadvantage
You can't detect when an attacker obtains a rogue certificate for a specific subdomain - all wildcards look the same in CT logs.
CT Log Monitoring Commands
# Search CT logs for your domain curl -s "https://crt.sh/?q=%.example.com&output=json" | jq '.' # Monitor for new certificates (individual certs are more visible) # With wildcards, you'll only see *.example.com entries
Compliance Considerations
Several security frameworks and compliance standards have specific guidance about wildcard certificate usage:
PCI DSS
While not explicitly prohibited, PCI DSS requires minimizing attack surface. Wildcards increase risk and may require additional compensating controls during audits.
NIST Guidelines
NIST SP 800-52 recommends careful consideration of wildcard certificates and suggests limiting their use to specific, controlled environments.
CA/Browser Forum
Baseline Requirements prohibit issuing wildcard EV certificates. Only DV and OV wildcards are permitted, limiting their use for high-assurance applications.
Related: Visit our PKI Compliance Hub for upcoming certificate validity deadlines and industry requirements.
When Wildcards Are Appropriate
Despite the risks, wildcards can be appropriate in specific scenarios with proper controls:
Internal/Private Networks
When all services are on a private network with strong access controls, the compromise risk is significantly reduced.
Development/Staging Environments
Non-production environments with no real customer data can use wildcards for convenience (but never share keys with production!).
Centralized TLS Termination
When all TLS terminates at a single, hardened load balancer with HSM key storage, the private key only exists in one secured location.
Dynamic/Ephemeral Subdomains
Multi-tenant SaaS platforms where subdomains are created dynamically (customer1.app.example.com) often need wildcards for practical reasons.
Safer Alternatives
1. SAN Certificates (Multi-Domain)
Subject Alternative Name certificates list specific subdomains explicitly:
# SAN Certificate includes: DNS:www.example.com DNS:api.example.com DNS:mail.example.com DNS:shop.example.com # Each subdomain is explicitly listed - more control, easier revocation
2. Automated Certificate Management (ACME)
Use Let's Encrypt or similar to issue individual certificates automatically:
# Certbot for individual certificates certbot certonly --standalone -d www.example.com certbot certonly --standalone -d api.example.com # Each service gets its own key - compromise is isolated
3. Service Mesh with mTLS
In Kubernetes/microservices, use per-service certificates with automatic rotation:
# Istio/Linkerd issues unique certificates per pod # Certificates are short-lived (often 24 hours) # Automatic rotation - no manual key management # Compromise of one service doesn't affect others
4. Centralized HSM for Wildcards
If you must use wildcards, store the private key in a Hardware Security Module at your load balancer. Keys never leave the HSM, limiting exposure.
Frequently Asked Questions
Can I get an EV wildcard certificate?
No. The CA/Browser Forum Baseline Requirements explicitly prohibit Extended Validation (EV) wildcard certificates. You can only get Domain Validation (DV) or Organization Validation (OV) wildcards. For high-assurance applications, you'll need individual EV certificates.
Does a wildcard cover sub-subdomains?
No. A wildcard certificate for *.example.com only covers one level of subdomain. It covers www.example.com and api.example.com, but NOT deep.api.example.com. For sub-subdomains, you'd need *.api.example.com (and most CAs don't issue these).
Are wildcards cheaper than individual certificates?
Depends on your scale. One wildcard might cost $200-500/year, while individual DV certs from Let's Encrypt are free. The real cost is operational: wildcards reduce certificate management overhead but increase security risk. Calculate total cost of ownership including incident response.
How do I audit where my wildcard private key is stored?
Search all servers for key files (find / -name '*.key' -o -name '*.pem'), check configuration management systems, review deployment scripts, and audit load balancer configurations. Any location with the private key is a potential attack vector.
What's the maximum validity for wildcard certificates?
Same as any public certificate: 398 days (approximately 13 months) as of September 2020. Industry is moving toward shorter validity periods - check our Compliance Hub for upcoming changes that may affect wildcard strategy.
See the Risks in Action
Try the interactive demo to visualize compromise scope, revocation cascades, and more.
Related Resources
Subject Alternative Names
Multi-domain certificates as a safer alternative to wildcards
Name Mismatch Guide
When wildcard scope limits cause domain mismatches
Certificate Anatomy
How wildcards are encoded in certificate extensions
Certificate Lifecycle
Managing wildcard certificate renewal and rotation
ACME Protocol Guide
Automate individual certificates as a safer alternative