The Tweet-Sized Distinction
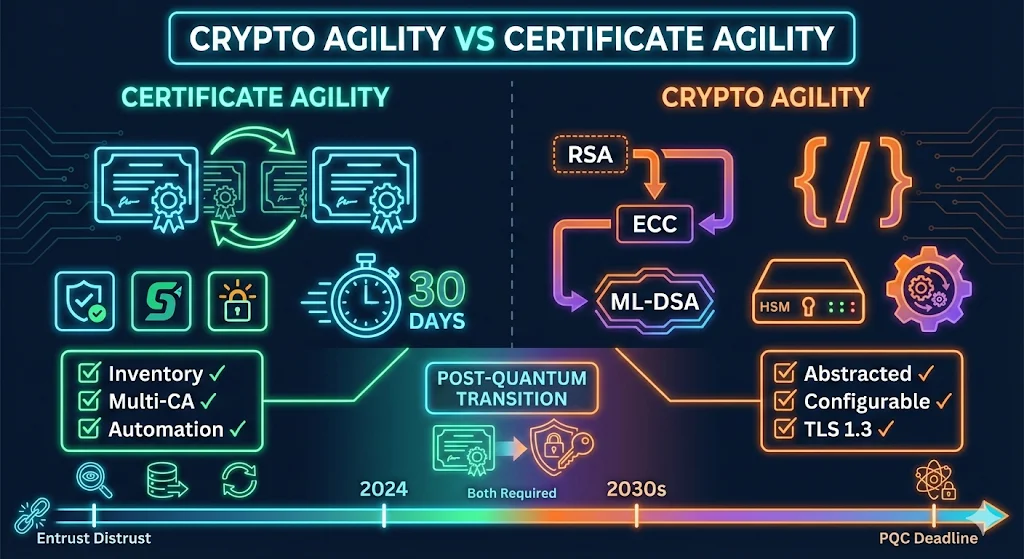
Certificate Agility: Can you replace 10,000 certificates in 30 days?
Crypto Agility: Can your systems handle a new algorithm tomorrow?
Section 1: Definitions
Certificate Agility
The organizational capability to rapidly discover, replace, and deploy certificates across your entire infrastructure when needed.
Triggered by:
- • CA distrust (Entrust, Symantec)
- • CA compromise (DigiNotar)
- • Key compromise incident
- • Mass revocation requirement
- • Validity period reductions (47-day certs coming)
Requires:
- Complete certificate inventory
- Automated provisioning
- Multi-CA relationships
- Tested replacement workflows
- Ownership accountability
Crypto Agility
The technical capability to change cryptographic algorithms, key sizes, or protocols without significant application rewrites or infrastructure changes.
Triggered by:
- • Algorithm deprecation (SHA-1 → SHA-256)
- • Key size requirements (1024 → 2048 → 3072)
- • Protocol updates (TLS 1.2 → 1.3)
- • Post-quantum transition (RSA → ML-DSA)
Requires:
- Abstracted crypto libraries
- Configuration-driven algorithm selection
- Hardware that supports new algorithms
- Testing/validation pipelines
- No hardcoded crypto assumptions
Section 2: Comparison Table
| Aspect | Certificate Agility | Crypto Agility |
|---|---|---|
| Question | How fast can you replace certs? | Can your systems use different algorithms? |
| Scope | Operational / Process | Architectural / Technical |
| Timeframe | Days to weeks | Months to years |
| Primary Tool | CLM platform (Venafi, etc.) | Code/config changes, hardware upgrades |
| Recent Test | Entrust distrust (2024) | SHA-1 deprecation (2017) |
| Coming Test | 47-day certificates (2029) | Post-quantum (2030s) |
| Failure Mode | Outages, manual scramble | Stuck on deprecated algorithms |
| Who Owns It | PKI / Security Ops | Development + Infrastructure |
Section 3: Why You Need Both
Scenario 1: CA Distrust (Certificate Agility Test)
Scenario 2: Algorithm Deprecation (Crypto Agility Test)
Scenario 3: Post-Quantum (Both Required)
Section 4: Certificate Agility Deep Dive
The Entrust Wake-Up Call
- June 2024: Google announces distrust
- November 2024: Enforcement begins
- Organizations with certificate agility: Routine migration
- Organizations without: "Stressed as hell" (actual quote)
Certificate Agility Maturity Levels
| Level | Description | Replace 1,000 Certs |
|---|---|---|
| 0 - None | No inventory, no process | Months (if ever) |
| 1 - Reactive | Spreadsheet, manual renewal | 4-8 weeks |
| 2 - Managed | CLM tool, known inventory | 2-4 weeks |
| 3 - Automated | Auto-provisioning, multi-CA | Days |
| 4 - Continuous | GitOps, short-lived certs | Hours |
Building Certificate Agility
- 1Discovery
Find every certificate (network scans, agent-based, cloud APIs)
- 2Inventory
Central database with ownership, locations, expiry
- 3Multi-CA
Relationships with 2+ CAs (don't be single-vendor)
- 4Automation
ACME, cert-manager, Venafi, or equivalent
- 5Testing
Practice replacements before emergencies
- 6Monitoring
Expiration alerts, compliance dashboards
Section 5: Crypto Agility Deep Dive
The SHA-1 Lesson
- 2005: SHA-1 theoretical weaknesses published
- 2017: Browsers enforce SHA-256 requirement
- 12 years to migrate... and people still scrambled
Why Crypto Agility is Hard
Hardcoded Assumptions
Applications with algorithm choices baked into the code
Hardware Limitations
HSMs may not support new algorithms; load balancers with fixed cipher suites; legacy systems with embedded crypto
Protocol Dependencies
TLS 1.2 doesn't support some PQC key exchange; certificate formats may need extensions
Code Example: Crypto-Agile vs Non-Agile
// ❌ Hardcoded algorithm and key size
KeyPairGenerator kpg = KeyPairGenerator.getInstance("RSA");
kpg.initialize(2048);
Signature sig = Signature.getInstance("SHA256withRSA");// ✅ Configuration-driven algorithm selection
String algorithm = config.get("key.algorithm"); // "RSA" or "EC" or "ML-DSA"
int keySize = config.get("key.size");
KeyPairGenerator kpg = KeyPairGenerator.getInstance(algorithm);
kpg.initialize(keySize);
String sigAlgorithm = config.get("signature.algorithm");
Signature sig = Signature.getInstance(sigAlgorithm);Crypto Agility Checklist
- Crypto libraries abstracted (not hardcoded)
- Algorithm selection via configuration
- HSMs support algorithm upgrades
- No SHA-1 or RSA-1024 dependencies
- TLS 1.3 supported (required for some PQC)
- Hybrid certificate support tested
- Certificate validation handles new algorithms
Section 6: Post-Quantum Convergence
Why PQC Requires Both Agility Types
| Task | Agility Type |
|---|---|
| Replace RSA certificates with ML-DSA | Certificate Agility |
| Applications accept ML-DSA signatures | Crypto Agility |
| HSMs support ML-KEM key exchange | Crypto Agility |
| Issue hybrid certificates during transition | Certificate Agility |
| Validate hybrid cert chains | Crypto Agility |
Timeline Pressure
The Organizations That Survive
- • Started building certificate agility after Entrust
- • Started building crypto agility after NIST announcement
- • Will combine both for PQC transition
Section 7: Assessment Quizzes
Certificate Agility Quiz
Crypto Agility Quiz
Section 8: Action Plan
If You're Starting from Zero
- • Deploy certificate discovery
- • Build initial inventory
- • Establish second CA relationship
- • Document current state
- • Implement CLM tool or automation
- • Define ownership for all certs
- • Create replacement runbooks
- • Test emergency procedures
- • Audit hardcoded crypto in applications
- • Inventory HSM capabilities
- • Plan TLS 1.3 migration
- • Evaluate PQC readiness
If You Have Certificate Agility
Section 9: Tools & Resources
Certificate Agility Tools
| Tool | Type | Notes |
|---|---|---|
| Venafi | Enterprise CLM | Full lifecycle management |
| cert-manager | Kubernetes | Cloud-native automation |
| Certbot/ACME | Open source | Let's Encrypt automation |
| Keyfactor | Enterprise CLM | Alternative to Venafi |
Crypto Agility Resources
| Resource | Purpose |
|---|---|
| NIST PQC Standards | Algorithm specifications (ML-DSA, ML-KEM, SLH-DSA) |
| Open Quantum Safe | PQC testing libraries |
| Cloudflare PQC | Hybrid TLS testing |
| NSA CNSA 2.0 | Timeline guidance for federal systems |
Frequently Asked Questions
Which is more urgent - certificate agility or crypto agility?
Certificate agility. You could face a CA distrust event any day. Crypto agility has a longer runway (5-10 years for PQC), but both are necessary.
Does Venafi provide crypto agility?
Venafi provides certificate agility (lifecycle management). Crypto agility requires changes to your applications and infrastructure that CLM tools can't solve alone.
Can I have certificate agility without automation?
Technically yes, but not at scale. If you have >100 certificates, manual processes will fail under pressure.
How did organizations with certificate agility handle Entrust?
They ran discovery queries to find Entrust certs, used existing automation to request replacements from alternate CAs, and deployed within their normal change windows. Total effort: days, not weeks.
When do I need to worry about post-quantum?
If you handle data that needs to stay confidential for 10+ years, now. "Harvest now, decrypt later" attacks mean encrypted data captured today could be decrypted by future quantum computers. For most organizations, 2027-2030 is the action window.
Related Resources
Post-Quantum Cryptography
NIST FIPS 203/204/205 standards and the 2035 migration timeline.
Certificate Discovery
Find all certificates in your environment before migration.
Venafi Integration Series
Enterprise certificate lifecycle management and automation.
Cipher Suite Decoder
Understand which algorithms your cipher suites use.
CA Hierarchy Design
Plan algorithm-agile CA infrastructure for the quantum transition.