Quick Answer
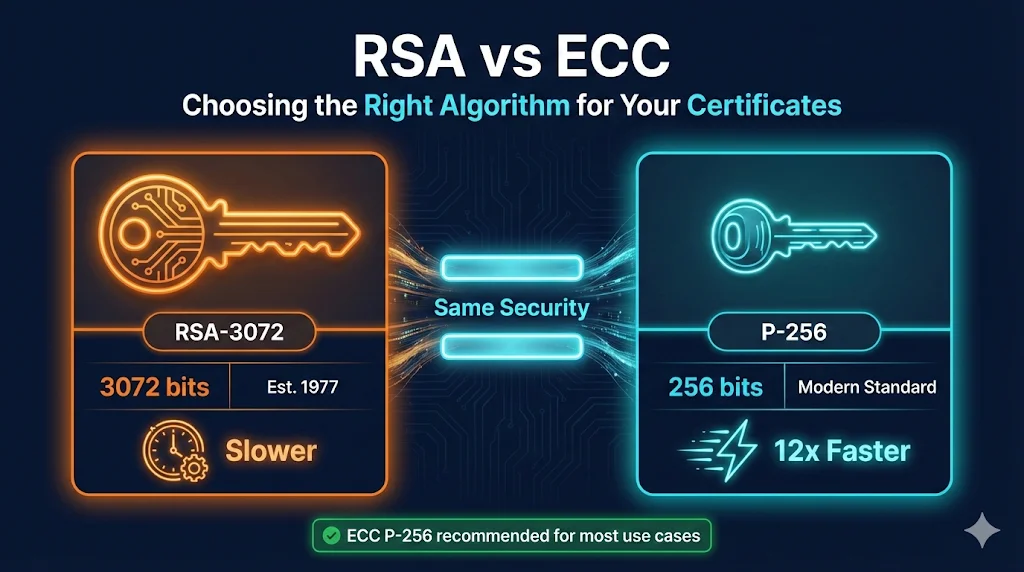
For most modern use cases: Use ECC P-256 (ECDSA).
It's faster, uses smaller keys, and provides equivalent security to RSA-3072 with a 256-bit key. Every major browser, server, and CA supports it.
Stick with RSA-2048 if:
You need compatibility with legacy systems (Windows XP, old Java) or your compliance requirements specifically mandate RSA.
What Are RSA and ECC?
RSA and ECC are both asymmetric encryption algorithms—they use a pair of keys (public and private) for encryption, decryption, and digital signatures. They're the cryptographic foundation of SSL/TLS certificates.
RSA (Rivest-Shamir-Adleman)
- Created: 1977
- How it works: Security based on the difficulty of factoring large prime numbers
- Key sizes: 1024-bit (deprecated), 2048-bit (minimum), 3072-bit, 4096-bit
- Status: The veteran. Battle-tested for 45+ years.
ECC (Elliptic Curve Cryptography)
- Created: 1985 (theoretical), widespread adoption 2010s
- How it works: Security based on the discrete logarithm problem on elliptic curves
- Key sizes: 256-bit (P-256), 384-bit (P-384), 521-bit (P-521)
- Status: The modern choice. Same security, smaller keys, better performance.
Security Strength: How They Compare
Here's the key insight: ECC achieves the same security with much smaller keys.
Security Strength Equivalence
Same protection, dramatically different key sizes
| Security Level | RSA Key Size | ECC Key Size | Symmetric Equivalent |
|---|---|---|---|
| 80-bit | 1024 | 160 | 2DES (deprecated) |
| 112-bit | 2048 | 224 | 3DES |
| 128-bit | 3072 | 256 (P-256) | AES-128 |
| 192-bit | 7680 | 384 (P-384) | AES-192 |
| 256-bit | 15360 | 521 (P-521) | AES-256 |
Key takeaway: A 256-bit ECC key provides the same security as a 3072-bit RSA key. That's 12x smaller.
What This Means in Practice
- • RSA-2048 (the current minimum for public certificates) provides ~112 bits of security
- • ECC P-256 provides ~128 bits of security—actually stronger than RSA-2048
- • RSA-4096 provides ~140 bits of security, but at significant performance cost
The CA/Browser Forum requires a minimum of RSA-2048 or ECC P-256 for publicly trusted certificates. Both meet compliance requirements.
Performance: Why ECC is Faster
Smaller keys don't just save space—they dramatically improve performance.
TLS Handshake Performance
Speed comparison for cryptographic operations
| Operation | RSA-2048 | ECC P-256 | Winner |
|---|---|---|---|
| Key Generation | ~300ms | ~15ms | 20x FASTER |
| Signing | ~1.5ms | ~0.15ms | 10x FASTER |
| Verification | ~0.05ms | ~0.3ms | RSA |
| Certificate Size | ~1,200 bytes | ~600 bytes | 50% SMALLER |
TLS Handshake Comparison
| Operation | RSA-2048 | ECC P-256 | Winner |
|---|---|---|---|
| Key Generation | ~300ms | ~15ms | ECC (20x faster) |
| Signing | ~1.5ms | ~0.15ms | ECC (10x faster) |
| Verification | ~0.05ms | ~0.3ms | RSA (6x faster) |
| Key Exchange | ~1.5ms | ~0.3ms | ECC (5x faster) |
| Certificate Size | ~1KB | ~500B | ECC (2x smaller) |
Wait—RSA verification is faster?
Yes, but it doesn't matter much. In a TLS handshake, signing and key exchange happen on every connection. Verification happens once. ECC wins overall because it dominates where it counts.
Real-World Impact
RSA-2048: Higher CPU load, more servers needed, higher latency
ECC P-256: Lower CPU load, faster connections, better user experience
RSA: Drains battery, slow on weak processors
ECC: Efficient, fast even on limited hardware
The Math (Without the Math)
You don't need to understand the cryptographic details, but here's the conceptual difference:
RSA Security
Based on factoring large numbers.
Given n = p × q (where p and q are very large prime numbers), it's computationally hard to find p and q from n.
The problem: To make this hard enough, you need really big numbers. That's why RSA keys are 2048+ bits.
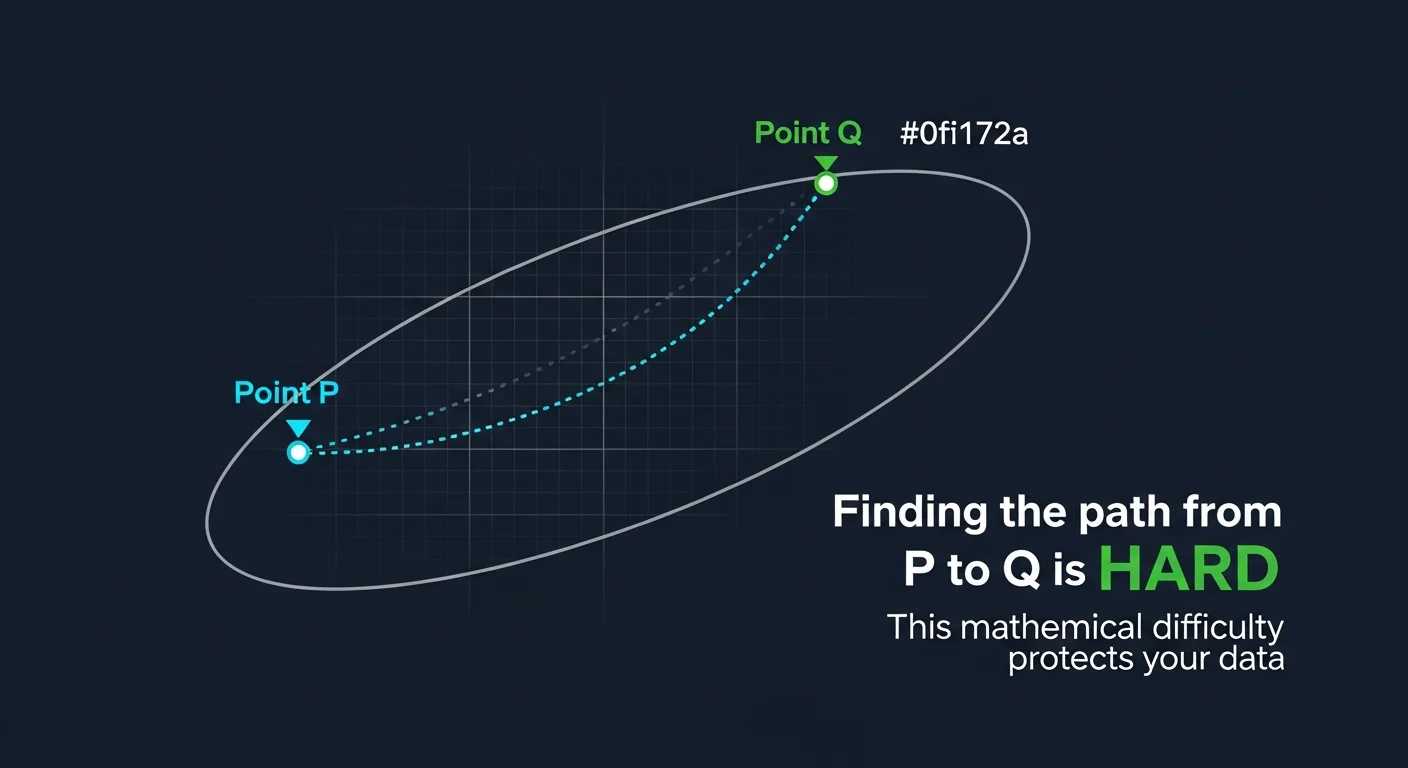
ECC Security
Based on the discrete logarithm problem on elliptic curves.
Given two points P and Q on a curve where Q = kP, it's computationally hard to find k.
The advantage: Elliptic curves provide more "hardness per bit." A 256-bit ECC key is as hard to crack as a 3072-bit RSA key.
Analogy: RSA is like securing a door with a really long combination lock. ECC is like using a shorter combination on a lock that's fundamentally harder to pick.
Common ECC Curves Explained
When you choose ECC, you also choose a curve. Here's what you'll encounter:
Common ECC Curves for TLS
Same curve, different names - don't get confused!
P-256
Best for most use cases
P-384
Government & financial
P-521
Compatibility issues
P-256 = prime256v1 = secp256r1 — These are ALL the same curve! OpenSSL uses 'prime256v1'
NIST Curves (Most Common for Certificates)
| Curve | Also Called | Security | Recommendation |
|---|---|---|---|
| P-256 | prime256v1, secp256r1 | 128-bit | Default choice |
| P-384 | secp384r1 | 192-bit | Higher security |
| P-521 | secp521r1 | 256-bit | Overkill, compatibility issues |
For SSL/TLS certificates, use P-256. It's the sweet spot of security, performance, and compatibility.
Other Curves (Special Purposes)
| Curve | Purpose | Notes |
|---|---|---|
| Ed25519 | Signatures (SSH, code signing) | Very fast, modern, not for TLS certs |
| X25519 | Key exchange (TLS 1.3) | Used automatically in TLS 1.3 |
| brainpool | EU government compliance | Limited browser support |
Common confusion: P-256, prime256v1, and secp256r1 are all the same curvewith different names. Same for P-384/secp384r1 and P-521/secp521r1.
When to Use RSA vs ECC
Which Algorithm Should You Use?
Follow the path to your answer
Modern choice for 99% of use cases
Use ECC P-256 When:
- Building modern web applications
- Performance matters (high-traffic sites)
- Resource-constrained environments (IoT, mobile)
- You want smaller certificates and faster handshakes
- All your clients are modern (post-2015)
Use RSA-2048+ When:
- Supporting legacy clients (Windows XP, IE6, Java 6)
- Compliance explicitly requires RSA
- Hardware/HSM doesn't support ECC
- Code signing (RSA has longer track record)
- Interoperating with older systems
Consider Both (Dual Certificates) When:
- Transitioning gradually from RSA to ECC
- Need maximum compatibility AND performance
- Uncertain about client capabilities
Compatibility Matrix
ECC P-256 Compatibility
Supported everywhere that matters (since 2008)
Unless you're supporting 15+ year old systems
Browser Support for ECC
| Browser | ECC Support Since | Notes |
|---|---|---|
| Chrome | Version 1 (2008) | Full support |
| Firefox | Version 2 (2006) | Full support |
| Safari | Version 4 (2009) | Full support |
| Edge | All versions | Full support |
| IE | Version 7 on Vista+ | No support on XP |
Bottom line: Unless you're supporting Windows XP users, ECC works everywhere.
Platform/Language Support
| Platform | ECC Support |
|---|---|
| Java | 7+ (limited), 8+ (full P-256/P-384) |
| .NET | 4.5+ |
| Node.js | All modern versions |
| Python | 2.6+/3.x with OpenSSL |
| OpenSSL | 1.0.1+ |
How to Generate RSA and ECC Keys
RSA Key Generation
# Generate RSA-2048 key (minimum) openssl genrsa -out private.key 2048 # Generate RSA-4096 key (stronger, slower) openssl genrsa -out private.key 4096 # View RSA key details openssl rsa -in private.key -text -noout
ECC Key Generation
# Generate ECC P-256 key (recommended) openssl ecparam -genkey -name prime256v1 -out private.key # Generate ECC P-384 key (higher security) openssl ecparam -genkey -name secp384r1 -out private.key # View ECC key details openssl ec -in private.key -text -noout # List all available curves openssl ecparam -list_curves
Create CSR with ECC Key
# Generate key and CSR in one command openssl req -new -newkey ec -pkeyopt ec_paramgen_curve:prime256v1 \ -keyout private.key -out request.csr -nodes \ -subj "/CN=www.example.com/O=Example Corp/C=US"
Migrating from RSA to ECC
Step 1: Audit Your Environment
- • Check all client applications and browsers
- • Review any compliance requirements
- • Test with a non-production certificate first
- • Inventory HSMs and hardware that handle keys
Step 2: Generate New ECC Key and CSR
openssl ecparam -genkey -name prime256v1 -out new-private.key openssl req -new -key new-private.key -out new-request.csr
Step 3: Submit CSR to Your CA
Most CAs automatically detect the algorithm from your CSR and issue the appropriate certificate type.
Step 4: Test Before Deployment
Use SSL Labs or similar tools to verify:
- • Certificate chain is complete
- • All target clients can connect
- • No mixed algorithm issues
Step 5: Deploy and Monitor
Replace your RSA certificate with the new ECC certificate. Monitor for any client connection failures.
Algorithm Requirements by Standard
CA/Browser Forum
- • Min RSA: 2048 bits
- • Min ECC: P-256
- • SHA-1: Prohibited
- • SHA-256: Required
NIST SP 800-131A
- • RSA-2048: OK through 2030
- • RSA-3072+: Recommended
- • ECC P-256: OK through 2030
- • ECC P-384: Higher security
PCI DSS v4.0
- • Requires "strong cryptography"
- • RSA-2048 or ECC P-256 minimum
- • Follow industry best practices
The Future: Post-Quantum Cryptography
Both RSA and ECC are vulnerable to future quantum computers. While practical quantum computers don't exist yet, organizations should be aware:
- Timeline: 10-20 years before quantum computers threaten current cryptography (estimates vary)
- Solution: NIST has standardized post-quantum algorithms (CRYSTALS-Kyber, CRYSTALS-Dilithium)
- Action now: Build "crypto agility" into your systems so you can switch algorithms when needed
For now, ECC P-256 or RSA-2048 remain secure. But design your systems to handle algorithm changes.
Read the Full Post-Quantum Cryptography GuideCommon Questions
Is ECC more secure than RSA?
At equivalent key sizes, they provide equivalent security. ECC's advantage is achieving that security with smaller keys, which improves performance.
Why do some sites still use RSA?
Legacy compatibility, compliance requirements, or simply "if it ain't broke." RSA isn't wrong—it's just less efficient.
Can I use ECC for code signing?
Yes, but RSA is more common for code signing because of broader tool compatibility and the long-term nature of signed code. Code you sign today might need verification in 20 years.
What's ECDSA vs ECDH?
ECDSA (Elliptic Curve Digital Signature Algorithm) is used for signatures (certificate signing). ECDH (Elliptic Curve Diffie-Hellman) is used for key exchange (TLS handshake). Both use elliptic curves; they serve different purposes.
Should I use P-384 instead of P-256?
For most uses, P-256 is sufficient. Use P-384 if you need 192-bit security or compliance requires it. The performance difference is measurable but not dramatic.
Summary: Decision Flowchart
Need a certificate algorithm? │ ├─ Supporting Windows XP / Java 6? → RSA-2048 │ ├─ Compliance requires RSA? → RSA-2048 or RSA-3072 │ ├─ Code signing for long-term? → RSA-3072 or RSA-4096 │ ├─ High-traffic web server? → ECC P-256 │ ├─ Mobile / IoT device? → ECC P-256 │ └─ Modern environment, no constraints? → ECC P-256
When in doubt: ECC P-256 is the safe, modern choice for SSL/TLS certificates.
Related Resources
References
- • NIST SP 800-57 Part 1 Rev 5: Recommendation for Key Management
- • NIST SP 800-131A Rev 2: Transitioning the Use of Cryptographic Algorithms
- • CA/Browser Forum Baseline Requirements
- • RFC 8446: TLS 1.3 Specification
Last Updated: December 2024