Quick Answer: What is Key Exchange?
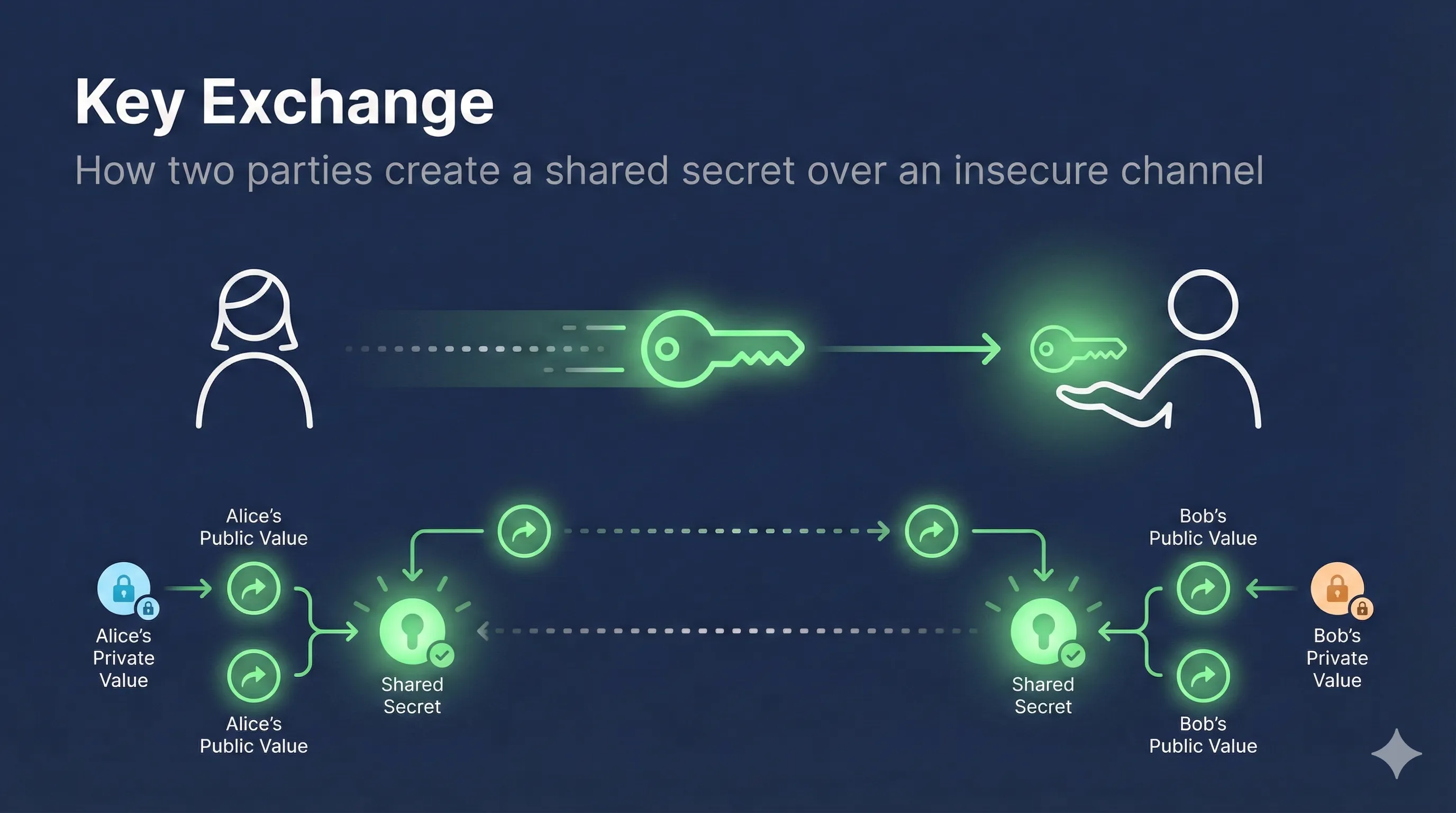
Key exchange is a cryptographic protocol that allows two parties to establish a shared secret key over an insecure channel, without ever transmitting the key itself.
Alice and Bob → agree on shared secret → over public internet → Eve listens but learns nothing
💡 Key Insight: Diffie-Hellman (1976) was revolutionary because it solved the "key distribution problem" - how to share encryption keys without a secure channel.
The Key Distribution Problem
Before Diffie-Hellman, secure communication required pre-sharing secret keys through secure channels (like meeting in person or using couriers). This was the fundamental problem with symmetric encryption.
The Chicken-and-Egg Problem
- → To send encrypted messages, you need a shared key
- → To share a key securely, you need encryption
- → But you don't have encryption without the key!
Diffie-Hellman's Solution
Instead of sending the key, both parties contribute to building the key together. Each side shares public information, but the combination creates a secret that only they know - and no eavesdropper can compute.
How Diffie-Hellman Works
Diffie-Hellman uses the mathematical properties of modular exponentiation. Here's the step-by-step process:
The Exchange Protocol
Public Agreement
Alice and Bob agree on two public numbers: a large prime p and a generator g. These can be known by everyone.
Generate Private Keys
Alice picks a secret number a. Bob picks a secret number b. These are never shared.
Compute and Exchange
Alice computes A = g^a mod p and sends it publicly.
Bob computes B = g^b mod p and sends it publicly.
Derive Shared Secret
Alice computes B^a mod p = g^(ab) mod p
Bob computes A^b mod p = g^(ab) mod p
They get the same result!
The Color Mixing Analogy
The classic way to understand Diffie-Hellman is with paint colors. Mixing is easy, but "unmixing" is practically impossible.
The Process
- 1. Alice and Bob agree on a common color (Yellow)
- 2. Alice picks a secret color (Red), Bob picks Blue
- 3. They mix their secret with the common color
- 4. They exchange the mixed colors publicly
- 5. Each adds their secret to the received mix
- 6. Both end up with the same final color!
Why Eve Can't Win
Eve cannot "unmix" to find the secret colors, so she can't compute the final shared color.
The Color Mixing Analogy
Mixing is easy, "unmixing" is impossible
The Mathematics Behind DH
The security of Diffie-Hellman relies on the Discrete Logarithm Problem (DLP): given g^x mod p, finding x is computationally infeasible for large numbers.
# Diffie-Hellman Mathematical Steps Public parameters (known to everyone): p = large prime number (2048+ bits) g = generator (primitive root mod p) Alice: a = random secret (private key) A = g^a mod p (public key, sent to Bob) Bob: b = random secret (private key) B = g^b mod p (public key, sent to Alice) Shared Secret Computation: Alice: s = B^a mod p = (g^b)^a mod p = g^(ab) mod p Bob: s = A^b mod p = (g^a)^b mod p = g^(ab) mod p Both compute the SAME value: g^(ab) mod p
Why This Works
The magic is in the commutativity of exponents: (g^a)^b = (g^b)^a = g^(ab). This means order doesn't matter - both parties reach the same result despite using different paths.
Attacker's View
- • Sees: p, g, A (g^a mod p), B (g^b mod p)
- • Must solve: find a from g^a (discrete log)
- • Complexity: infeasible for large primes
Parties' View
- • Alice knows: a (secret), B (received)
- • Bob knows: b (secret), A (received)
- • Both compute: same shared secret g^(ab)
DH vs DHE vs ECDHE
| Variant | Full Name | Key Type | Forward Secrecy |
|---|---|---|---|
| DH | Diffie-Hellman (static) | Fixed keys | ❌ No |
| DHE | DH Ephemeral | New keys per session | ✅ Yes |
| ECDHE | Elliptic Curve DHE | New EC keys per session | ✅ Yes |
DHE (Ephemeral)
New DH keys are generated for each session. Even if long-term keys are compromised later, past sessions remain secure (forward secrecy).
ECDHE
Uses elliptic curve cryptography for the same security with smaller keys. 256-bit ECDHE ≈ 3072-bit DHE in security. Much faster and default in TLS 1.3.
DH Variant Comparison
From basic to modern key exchange
Static Diffie-Hellman
Vulnerable if key leaked
DH Ephemeral
Forward secrecy
Elliptic Curve DHE
Best: FS + speed
Security Considerations
Parameter Requirements
- ✓ Use at least 2048-bit DH parameters (3072+ recommended)
- ✓ Use well-known groups (RFC 7919) or generate parameters securely
- ✓ Prefer ECDHE over DHE for better performance
DH Parameter Strength Timeline
Known Attacks
Man-in-the-Middle (MITM)
Basic DH doesn't authenticate parties. An attacker could perform separate exchanges with each party. Solution: Combine with authentication (certificates in TLS).
Logjam Attack (CVE-2015-4000)
Exploits weak 512/1024-bit DH parameters. Many servers shared common parameters, making precomputation attacks feasible. Solution: Use 2048+ bit parameters.
Key Exchange in TLS
TLS uses key exchange to establish the "master secret" from which all session keys are derived.
RSA vs (EC)DHE Key Exchange
| Feature | RSA Key Exchange | (EC)DHE Key Exchange |
|---|---|---|
| Forward Secrecy | ❌ No - compromised key decrypts all past traffic | ✅ Yes - each session uses unique keys |
| Performance | 1 RTT, single decrypt | Key generation per session (ECDHE is fast) |
| TLS 1.3 Support | ❌ Removed | ✅ Required |
| Risk | High - "harvest now, decrypt later" | Low - ephemeral keys discarded |
| Recommendation | Disable immediately | Use ECDHE with X25519 or P-256 |
TLS 1.3 Key Exchange
Client → Server: ClientHello - Supported cipher suites - Key share (ECDHE public key) Server → Client: ServerHello - Selected cipher suite - Key share (ECDHE public key) - Encrypted extensions, certificate, finished # Both derive shared secret from key shares # All subsequent traffic encrypted with derived keys
TLS 1.3 requires forward-secret key exchange (ECDHE or DHE). RSA key exchange was removed.
Cipher Suite Examples
# TLS 1.3 (ECDHE only, key exchange not specified in name) TLS_AES_256_GCM_SHA384 TLS_CHACHA20_POLY1305_SHA256 # TLS 1.2 with ECDHE (forward secrecy) TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 TLS_ECDHE_ECDSA_WITH_CHACHA20_POLY1305_SHA256 # TLS 1.2 with DHE (forward secrecy, slower) TLS_DHE_RSA_WITH_AES_256_GCM_SHA384 # TLS 1.2 with RSA key exchange (NO forward secrecy - deprecated) TLS_RSA_WITH_AES_256_GCM_SHA384
OpenSSL Commands
Generate DH Parameters
# Generate 2048-bit DH parameters (may take a while) openssl dhparam -out dhparam.pem 2048 # Generate 4096-bit DH parameters (very slow, more secure) openssl dhparam -out dhparam.pem 4096 # View DH parameters openssl dhparam -in dhparam.pem -text -noout
Generate ECDHE Keys
# List available curves openssl ecparam -list_curves # Generate ECDHE key pair (P-256 curve) openssl ecparam -genkey -name prime256v1 -out ecdhe_private.pem # Extract public key openssl ec -in ecdhe_private.pem -pubout -out ecdhe_public.pem # Generate X25519 key (modern, preferred) openssl genpkey -algorithm X25519 -out x25519_private.pem openssl pkey -in x25519_private.pem -pubout -out x25519_public.pem
Test Server Key Exchange
# Check what key exchange a server uses openssl s_client -connect example.com:443 2>/dev/null | grep -E "Server Temp Key|Cipher" # Force specific cipher suite to test openssl s_client -connect example.com:443 -cipher ECDHE-RSA-AES256-GCM-SHA384
Related Resources
Encryption Basics
Understand symmetric vs asymmetric encryption fundamentals.
Forward Secrecy
Learn why ephemeral key exchange protects past sessions.
How TLS Works
See how key exchange fits into the TLS handshake process.
TLS Handshake
Deep dive into the handshake protocol and message flow.
RSA vs ECC
Compare key exchange algorithms and their security properties.
Hash Functions
How hashing is used in key derivation and authentication.
Frequently Asked Questions
Why is Diffie-Hellman considered secure?
DH relies on the discrete logarithm problem: computing x from g^x mod p is computationally infeasible for large numbers. The best known algorithms still require exponential time.
What is forward secrecy?
Forward secrecy (or perfect forward secrecy) means that if long-term keys are compromised, previously recorded sessions cannot be decrypted. DHE and ECDHE provide this by using fresh keys for each session.
Should I use DHE or ECDHE?
Use ECDHE. It provides equivalent security with smaller keys and faster computation. X25519 (Curve25519 for ECDH) is the modern choice for TLS 1.3.
Can quantum computers break Diffie-Hellman?
Yes, Shor's algorithm can solve the discrete logarithm problem efficiently on a quantum computer. Post-quantum key exchange algorithms (like Kyber/ML-KEM) are being standardized as replacements.
Why does TLS 1.3 require ECDHE?
TLS 1.3 mandates forward secrecy. RSA key exchange (where the client encrypts a pre-master secret with the server's public key) was removed because compromising the server's private key would allow decryption of all past sessions.
Ready to See It in Action?
Watch the Diffie-Hellman key exchange step-by-step with our interactive color mixing demo.
Try the Interactive Demo