Quick Answer
This guide is for security, IT, and compliance professionals at essential and important entities who need to demonstrate NIS2-aligned control over cryptographic assets.
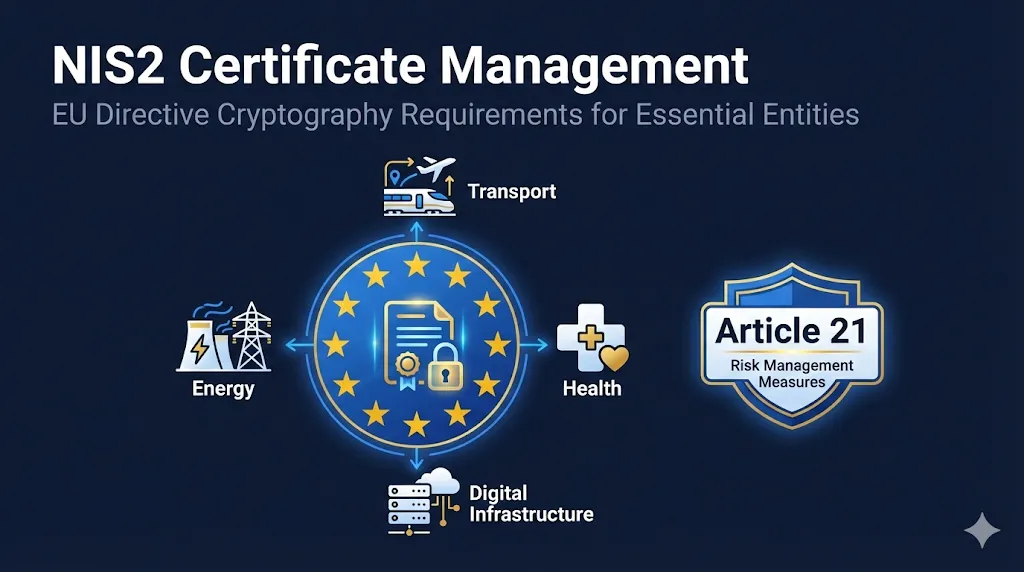
NIS2 (Directive (EU) 2022/2555) is the EU's updated cybersecurity directive requiring organizations operating critical infrastructure to implement comprehensive security measures. Article 21(2)(h) specifically mandates "policies and procedures regarding the use of cryptography and, where appropriate, encryption"—making certificate management directly relevant.
Why this matters: Unlike its predecessor NIS1, NIS2 explicitly calls out cryptography as a required security measure. Certificate outages, weak algorithms, or CA compromises can now trigger regulatory scrutiny—not just IT incidents.
💡 Key Difference from DORA: NIS2 has broader scope (not just financial services) and covers any organization providing essential or important services. If you're a digital infrastructure provider, healthcare entity, or energy company—this applies to you.
Note: This guide provides general educational information, not legal advice. NIS2 is a directive requiring transposition into Member State national law—specific requirements may vary by jurisdiction. Consult with your legal/compliance team and align with your national competent authority's guidance.
What is NIS2?
The Network and Information Security Directive 2 (NIS2) is an EU directive that establishes cybersecurity requirements for entities operating in critical sectors. It replaces the original NIS Directive (2016) with significantly expanded scope and stricter requirements.
Effective Date
October 17, 2024 - Member States were required to transpose NIS2 into national law. Enforcement began October 18, 2024.
Key Difference from NIS1
NIS2 explicitly requires cryptography policies and introduces personal liability for management. Penalties are significantly higher.
Key Deadlines
Who Must Comply?
Essential Entities
Large enterprises (250+ employees or €50M+ turnover)
Max Penalty: €10M or 2% of global turnover
Important Entities
Medium enterprises (50+ employees or €10M+ turnover)
Max Penalty: €7M or 1.4% of global turnover
Article 21: Cryptography Requirements
Article 21(2)(h) - The Cryptography Mandate
"The measures referred to in paragraph 1 shall be based on an all-hazards approach and shall include at least the following: ... (h) policies and procedures regarding the use of cryptography and, where appropriate, encryption."
— Directive (EU) 2022/2555, Article 21(2)(h)
What This Means for Certificate Management
Algorithm Standards
You must document which cryptographic algorithms are approved for use. RSA-2048 minimum, ECC P-256+, SHA-256+ for signing. Weak algorithms (SHA-1, RSA-1024) must be identified and retired.
Key Management
Private keys must be protected throughout their lifecycle. Document key generation, storage (HSM for critical keys), rotation, and destruction procedures.
Certificate Lifecycle
Demonstrate control over certificate issuance, renewal, and revocation. Maintain a centralized inventory including third-party SaaS and shadow IT endpoints—regulators are increasingly sensitive to external dependencies. Automated discovery, expiry monitoring, and ownership assignment are now expected controls to evidence NIS2 Article 21(2)(h) compliance.
Encryption in Transit
TLS configuration matters. Document minimum TLS versions (TLS 1.2+), cipher suite policies, and certificate pinning where appropriate.
NIS2 Security Measures Mapped to CLM
Article 21(2) lists ten minimum security measures. Here's how each maps to certificate lifecycle management capabilities:
| Article 21(2) | Requirement | CLM Implementation |
|---|---|---|
| (a) | Risk analysis and security policies | Certificate risk assessment, cryptography policy documentation |
| (b) | Incident handling | Certificate-related incident response, compromise procedures |
| (c) | Business continuity | Certificate failover, CA redundancy, backup procedures |
| (d) | Supply chain security | CA vendor assessment, third-party certificate validation |
| (e) | Acquisition, development, maintenance | Secure certificate deployment in CI/CD pipelines |
| (f) | Vulnerability handling | Weak key detection, algorithm vulnerability scanning |
| (g) | Security measure effectiveness | Certificate expiry metrics, incident frequency tracking |
| (h) | Cryptography policies | Certificate management policy, algorithm standards, key lifecycle |
| (i) | HR security and access control | Certificate-based authentication (mTLS), client certificates |
| (j) | MFA and secure authentication | Certificate-based MFA, smart card certificates, FIDO2 |
Cryptography Policy Requirements
Your cryptography policy must address three key areas. Here's what auditors expect to see:
1Algorithm Standards
| Use Case | Minimum Standard | Recommended |
|---|---|---|
| Asymmetric Keys | RSA-2048, ECC P-256 | RSA-3072+, ECC P-384+ |
| Hash Functions | SHA-256 | SHA-384, SHA-512 |
| TLS Version | TLS 1.2 | TLS 1.3 |
| Key Exchange | ECDHE | X25519 |
These recommendations align with ENISA NIS2 guidance. Review and version these baselines at least annually or upon disclosure of significant cryptographic vulnerabilities.
2Key Management Lifecycle
3Certificate Management Controls
- Complete certificate inventory with ownership assignment
- Automated expiry monitoring with escalation procedures
- Documented renewal procedures with SLAs
- Revocation procedures and CRL/OCSP verification
- CA trust store management and root store policies
- Certificate Transparency log monitoring
Incident Reporting & Certificates
NIS2 introduces strict incident reporting timelines. Certificate-related incidents may trigger these requirements depending on their impact on service continuity, data confidentiality/integrity, and whether they meet your national CSIRT/supervisory authority thresholds—not every minor certificate misconfiguration is automatically reportable.
| Timeline | Requirement | Certificate Context |
|---|---|---|
| 24 hours | Early warning notification | Initial alert that a certificate incident is causing service disruption |
| 72 hours | Incident notification | Root cause (expired cert, revocation, compromise), affected systems, initial remediation |
| 1 month | Final report | Complete analysis, preventive measures, process improvements |
Certificate-Related Incidents to Report
- Certificate expiry causing service outage affecting users or critical operations
- Private key compromise or suspected unauthorized access
- CA compromise affecting your certificates (e.g., DigiNotar-style events)
- Mis-issuance of certificates for your domains by unauthorized parties
- Chain validation failures causing widespread authentication failures
- Revocation infrastructure failures preventing proper certificate checking
Important: Member State transposition laws may define different thresholds for what constitutes a reportable cryptographic incident. Confirm your local CSIRT requirements—some jurisdictions may narrow or broaden these categories.
Supply Chain Security (Article 21(2)(d))
NIS2 requires entities to address security in supplier relationships. For certificate management, this means scrutinizing your CA vendors and third-party certificate dependencies. Both public CAs (used for internet-facing services) and private/internal CAs fall in scope where they support NIS2-relevant services.
CA Trust Decisions
- Document CA selection criteria and approval process
- Assess CA security practices (WebTrust, ETSI audits)
- Review CA incident history and response capabilities
- Maintain CA exit strategy and migration plans
Vendor Certificate Requirements
- Require TLS 1.2+ for all vendor integrations
- Validate vendor certificate chains before trusting
- Monitor Certificate Transparency for vendor domains
- Include certificate security in vendor contracts
Concentration Risk (Article 21(2)(d) & Article 23): Avoid relying on a single CA for all certificates. Auditors reviewing supply-chain security under NIS2 will look for documented CA diversification and exit strategies. If that CA is distrusted (as happened with Symantec and Entrust), you need the ability to rapidly migrate to alternatives. See our CA Migration Runbook.
Implementation Checklist
Use this checklist to assess your NIS2 readiness for certificate management:
Documentation Requirements
Technical Controls
Process Controls
How to Evidence This to Auditors
When auditors ask "show me where NIS2 cryptography requirements live in your controls," be ready to produce:
- Cryptography Policy — Approved, versioned, with management sign-off
- CLM Dashboard — Certificate inventory with ownership, expiry status, algorithm breakdown
- CA Due Diligence Records — Selection criteria, audit reports (WebTrust/ETSI), risk assessments
- Incident Post-Mortems — Certificate-related incidents with root cause, timeline, and improvements
- Management Reports — Periodic certificate posture briefings to demonstrate Article 32 oversight
Benchmark Your Readiness
Take our comprehensive assessment to score your PKI governance maturity and get prioritized recommendations.
Take the Maturity AssessmentPenalties & Enforcement
NIS2 introduces significant penalties and, notably, personal liability for management.
NIS2 Maximum Administrative Fines (Article 34) for Cybersecurity Failures Including Cryptography
| Entity Type | Maximum Fine | Management Liability |
|---|---|---|
| Essential Entities | €10,000,000 or 2% of global turnover (whichever is higher) | Personal liability for senior management; possible temporary bans |
| Important Entities | €7,000,000 or 1.4% of global turnover (whichever is higher) | Management accountability required; supervisory measures possible |
Management Liability (Article 32)
NIS2 explicitly holds management bodies personally accountable for cybersecurity. This means the board and C-suite can face personal consequences for inadequate security measures, including those related to cryptography and certificate management. Management must approve and oversee cybersecurity risk management measures.
For PKI: Article 32 obligations are exercised through documented approval of the cryptography policy and regular reporting on certificate posture. Ensure management formally signs off on algorithm standards, CA selection decisions, and receives periodic briefings on certificate risk metrics.
Cross-References
Related FixMyCert Resources
- DORA Certificate Management Guide
Financial services-specific compliance mapping
- Mutual TLS (mTLS) Guide
Certificate-based authentication for NIS2 Article 21(i)
- Certificate Lifecycle Guide
End-to-end certificate management fundamentals
- PKI Disasters Hall of Fame
Learn from CA compromises and certificate failures
- Compliance Hub
Track NIS2, DORA, and browser program deadlines
Official EU Resources
- NIS2 Directive Full Text
Official EUR-Lex publication
- EC NIS2 Policy Page
European Commission overview and updates
- ENISA NIS2 Resources
Implementation guidance from EU cybersecurity agency
Integration with Existing Frameworks
Don't treat NIS2 as greenfield—reuse existing PKI controls from other frameworks:
| Framework | Relevant Controls | NIS2 Mapping |
|---|---|---|
| ISO 27001 | A.10 Cryptography, A.12 Operations | Art. 21(2)(h), 21(2)(b) |
| NIST 800-53 | SC-12, SC-13, SC-17 | Art. 21(2)(h) |
| SOC 2 | CC6.1, CC6.7 (Encryption) | Art. 21(2)(h) |
| PCI DSS 4.0 | Req 3 (Crypto), Req 4 (Transmission) | Art. 21(2)(h) |
If you already maintain ISO 27001 or SOC 2 attestations, you likely have most cryptography documentation in place. Map existing controls to NIS2 requirements rather than duplicating effort.
If You Only Do Three Things...
Short on time? Focus on these three priorities to make immediate NIS2 progress:
Document
Write your cryptography policy. Cover algorithms, keys, and certificates.
Inventory
Know every certificate. Deploy discovery and assign owners.
Plan
Create incident response procedures for certificate events.
Related Resources
PKI Governance Maturity Assessment
Score your certificate management maturity across 6 categories.
DORA Certificate Management
If you're in financial services, you may also need to comply with DORA.
Compliance Hub
Track deadlines across CA/Browser Forum, DORA, NIS2, and browser programs.
Checklists & Runbooks
Actionable procedures for certificate operations and incident response.