CloudFront SSL Architecture
Like other CDNs, CloudFront uses two separate SSL/TLS connections:
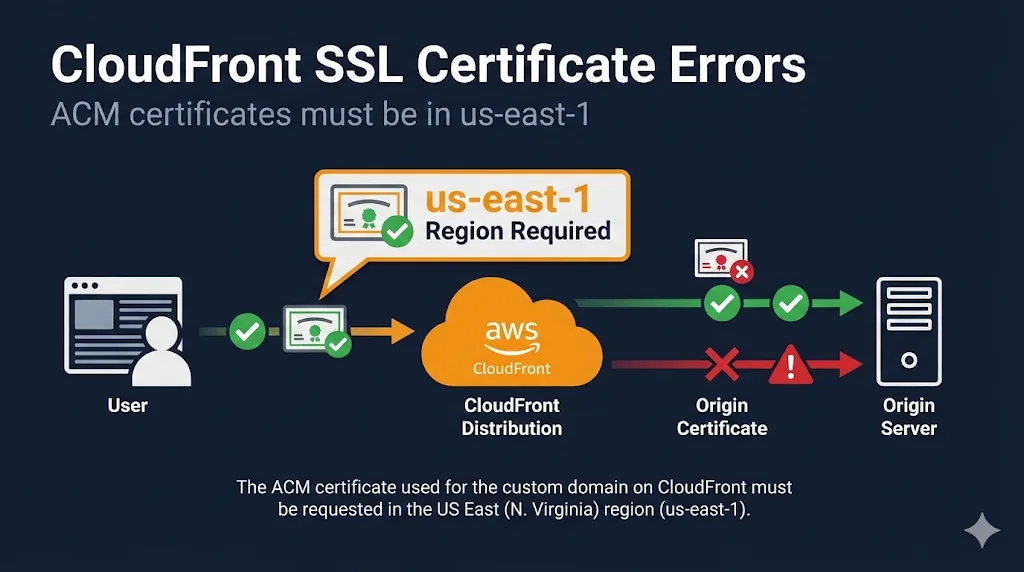
The us-east-1 Requirement
CloudFront is a global service that reads certificates from us-east-1 only.
- • Certificates in other regions (eu-west-1, ap-southeast-1, etc.) are invisible to CloudFront
- • You cannot move ACM certificates between regions
- • You must request a new certificate in us-east-1
Other us-east-1 Requirements
These AWS services also require us-east-1 for CloudFront:
- • Lambda@Edge - Functions must be created in us-east-1
- • WAF WebACL - Must be created in us-east-1 (for CloudFront)
- • CloudFront Functions - Associated with us-east-1
Viewer Certificate Options
These options control the certificate visitors see when connecting to your CloudFront distribution:
| Option | Cost | Region | Renewal | Best For |
|---|---|---|---|---|
| Default CloudFront | Free | N/A | Auto | Testing only (*.cloudfront.net) |
| ACM Certificate | Free | us-east-1! | Auto | Production ✓ |
| IAM Certificate | Cert cost | N/A | Manual | Legacy / Non-ACM certs |
Origin SSL Settings
Origin Protocol Policy
| Setting | What It Does | Security |
|---|---|---|
| HTTP Only | Unencrypted to origin | ⚠️ Insecure |
| HTTPS Only | Encrypted to origin | ✓ Recommended |
| Match Viewer | Matches visitor's protocol | Transitional |
Origin SSL Protocols
Recommended minimum: TLSv1.2
- • SSLv3: Deprecated - never use
- • TLSv1.0/1.1: Legacy - avoid if possible
- • TLSv1.2: Recommended minimum
Common Errors & Fixes
ACM Validation Methods
DNS Validation (Recommended)
- • Add a CNAME record to your DNS
- • Automatic renewal (no action needed)
- • Route 53 Tip: One-click "Create record in Route 53" button
# Example CNAME record _abc123.example.com. CNAME _xyz789.acm-validations.aws.
Email Validation
ACM sends emails to these addresses:
- • admin@example.com
- • administrator@example.com
- • hostmaster@example.com
- • postmaster@example.com
- • webmaster@example.com
Plus WHOIS contact if available
CloudFront + S3
S3 Website Endpoint Does NOT Support HTTPS
If using S3 static website hosting (bucket-name.s3-website-region.amazonaws.com), CloudFront to origin is HTTP only. Use REST API endpoint instead for HTTPS.
| Endpoint Type | Format | HTTPS to Origin |
|---|---|---|
| REST API | bucket.s3.region.amazonaws.com | ✓ Supported |
| Website | bucket.s3-website-region.amazonaws.com | ✗ HTTP only |
Origin Access Control (OAC)
Use OAC to restrict S3 access to CloudFront only. This is more secure than Origin Access Identity (OAI) and supports all S3 features including SSE-KMS.
Debugging Checklist
Work through this checklist when troubleshooting CloudFront SSL:
CDN SSL Comparison
| Feature | CloudFront | Cloudflare | Akamai |
|---|---|---|---|
| Region Requirement | us-east-1 only! | None | None |
| Free Edge Cert | ACM (free) | Universal SSL | Standard TLS |
| Auto-Renewal | ✓ ACM | ✓ | ✓ |
| Origin Validation | Protocol Policy | SSL Mode | Verify Setting |
Frequently Asked Questions
Why doesn't my certificate appear in CloudFront?
99% of the time, it's because the certificate is not in us-east-1 (N. Virginia). Check your ACM region in the AWS Console. You cannot move certificates between regions - you must request a new one in us-east-1.
Can I use non-ACM certificates with CloudFront?
Yes, via IAM certificate store, but it's more complex and requires manual renewal. ACM is free and auto-renews, so it's strongly recommended unless you have specific requirements for external certificates.
Does CloudFront support Let's Encrypt?
For the viewer certificate (edge), use ACM instead - it's free and auto-renews like Let's Encrypt. For origin certificates, you can absolutely use Let's Encrypt on your origin server.
How do I force HTTPS on CloudFront?
Set Viewer Protocol Policy to "Redirect HTTP to HTTPS" in your distribution's cache behavior settings. This redirects all HTTP requests to HTTPS.
Can I share an ACM certificate between CloudFront and ALB?
Yes, but with limitations. CloudFront requires us-east-1, while ALB uses the certificate in its own region. You'll need the same certificate in both regions, or use a wildcard certificate.
How long does ACM validation take?
DNS validation typically completes within minutes once the CNAME record is created. Email validation depends on how quickly you click the approval link. After validation, certificate issuance is usually instant.
Related Resources
Cloudflare Error 526
Fix Invalid SSL Certificate errors when using Cloudflare Full (Strict) mode.
Akamai SSL Certificate Errors
Edge vs origin certificates and Property Manager SSL configuration.
AWS ACM Complete Guide
Master ACM validation, auto-renewal, and the us-east-1 CloudFront requirement.
Chain Builder & Troubleshooting
Build complete certificate chains and diagnose chain validation failures.
How TLS Works
Understand the TLS handshake and certificate validation process.
Certificate Anatomy
Learn what's inside an X.509 certificate and how each field affects validation.