What is a CSR?
A Certificate Signing Request (CSR) is a block of encoded text that contains information about the entity requesting a certificate and the public key that will be included in the certificate. You submit a CSR to a Certificate Authority (CA) to obtain an SSL/TLS certificate.
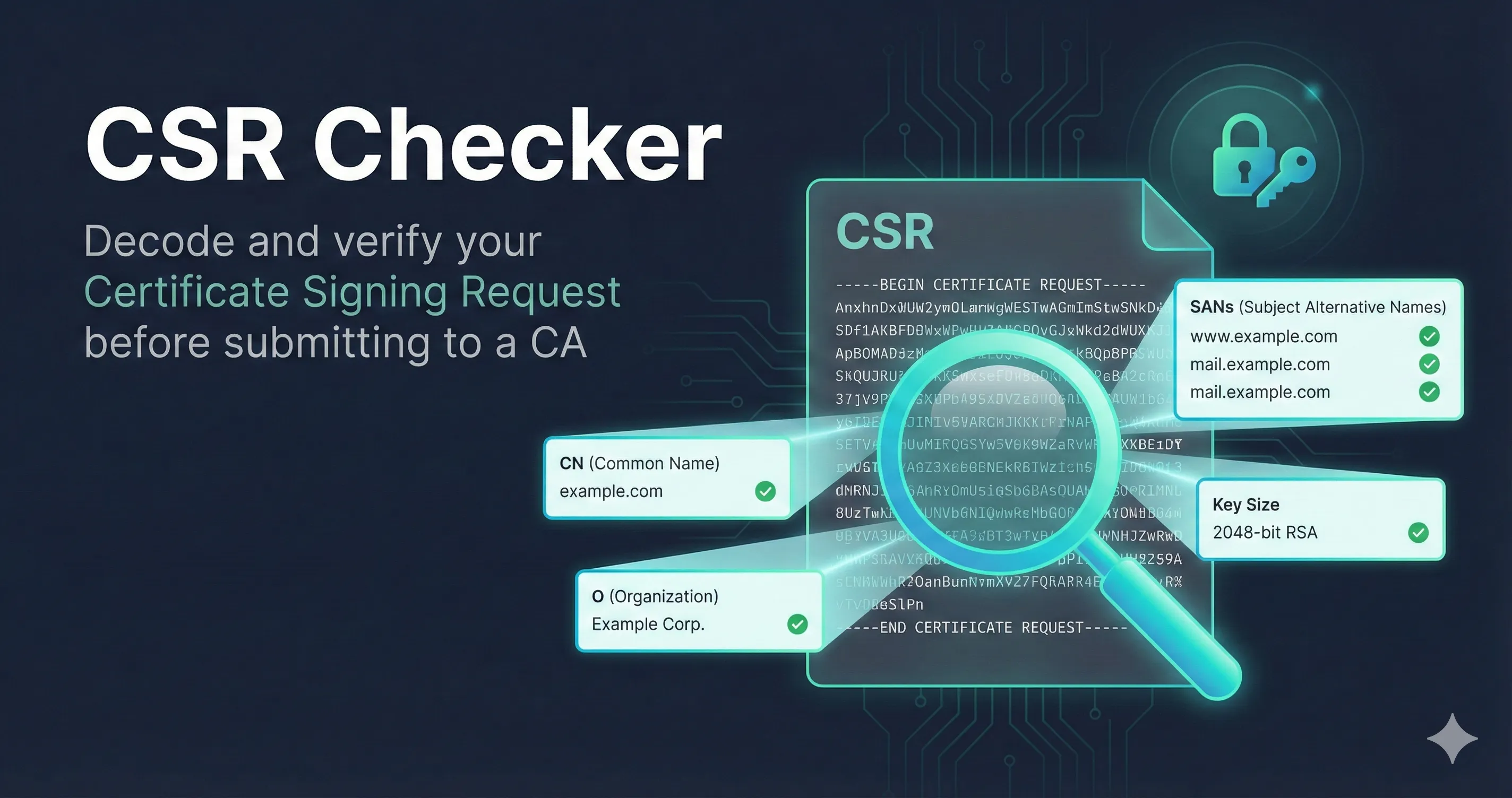
The CSR Checker tool decodes your CSR entirely in your browser—nothing is sent to any server—and shows you exactly what information it contains before you submit it to a CA.
Validation Status
The first thing you'll see is whether the CSR is valid. This checks two things:
The CSR is properly formatted AND the signature matches the public key. This means the CSR was created correctly and hasn't been tampered with.
The CSR could be parsed but signature verification failed. This might be due to an unsupported algorithm or a corrupted CSR. The CA may still accept it.
Subject Information
The subject contains identifying information about who is requesting the certificate. Not all fields are required—it depends on the certificate type.
| Field | Description | When Required |
|---|---|---|
| CN | Common Name - usually the domain name | Optional (SANs preferred) |
| O | Organization - legal company name | OV/EV certificates |
| OU | Organizational Unit - department | Prohibited since 2022 |
| L | Locality - city | OV/EV certificates |
| ST | State or Province | OV/EV certificates |
| C | Country (2-letter ISO code) | OV/EV certificates |
Important: The Organizational Unit (OU) field has been prohibited in public TLS certificates since September 2022 per CA/Browser Forum requirements. If your CSR includes an OU field, the CA will likely ignore it or reject the request.
Public Key Details
The public key section shows the cryptographic strength of your certificate. Here's what to look for:
RSA Keys
| Key Size | Status | Notes |
|---|---|---|
| 1024-bit | Rejected | Will not be accepted by any public CA |
| 2048-bit | Acceptable | Current minimum, consider upgrading |
| 3072-bit | Good | Recommended for new certificates |
| 4096-bit | Strong | Very secure, slightly slower handshakes |
ECDSA Keys
ECDSA (Elliptic Curve) keys offer equivalent security with smaller key sizes and faster performance:
| Curve | Equivalent RSA | Status |
|---|---|---|
| P-256 | ~3072-bit RSA | Recommended |
| P-384 | ~7680-bit RSA | Strong |
| P-521 | ~15360-bit RSA | Very Strong |
Subject Alternative Names (SANs)
SANs are the domains and IP addresses that the certificate will be valid for. This is one of the most important parts of your CSR to verify.
Critical Change: Since 2017, browsers check SANs instead of Common Name to determine certificate validity. If your domain isn't in the SAN list, the certificate won't work—even if it's in the Common Name field.
SAN Types
- •DNS: Domain names like www.example.com or *.example.com (wildcard)
- •IP: IP addresses for direct IP access (less common)
- •Email: Email addresses (for S/MIME certificates)
- •URI: Full URIs (rare in TLS certificates)
No SANs? If your CSR has no SANs, the CA will likely add the Common Name as a SAN automatically. However, it's better to include SANs explicitly—especially if you need multiple domains on one certificate.
Signature Algorithm
The signature algorithm is used to sign the CSR itself (proving you have the private key). The CA will typically use the same algorithm family for the final certificate.
| Algorithm | Status |
|---|---|
| SHA-256 with RSA | Standard (most common) |
| SHA-384 with RSA | Strong |
| SHA-256 with ECDSA | Recommended for EC keys |
| SHA-1 with RSA | Deprecated - will be rejected |
| MD5 with RSA | Insecure - will be rejected |
Common Issues and How to Fix Them
RSA key too small (1024-bit)
Your CSR uses an RSA key that's considered insecure. Generate a new key pair with at least 2048 bits:
openssl genrsa -out server.key 3072
No SANs in CSR
Create a config file to add SANs. Save this as san.cnf:
[req] distinguished_name = req_distinguished_name req_extensions = v3_req [req_distinguished_name] CN = www.example.com [v3_req] subjectAltName = @alt_names [alt_names] DNS.1 = www.example.com DNS.2 = example.com
Then generate your CSR: openssl req -new -key server.key -out server.csr -config san.cnf
SHA-1 signature algorithm
SHA-1 is deprecated. Regenerate your CSR specifying SHA-256:
openssl req -new -sha256 -key server.key -out server.csr
Wrong domain in Common Name
The domain in your CSR doesn't match your website. You'll need to generate a new CSR with the correct domain. Make sure to include it as both the CN and in the SANs for maximum compatibility.
Privacy & Security
CSRs contain only your public key and identifying information—there's nothing secret in them. However:
- •The CSR Checker runs entirely in your browser. Your CSR is never sent to any server.
- •Never paste your private key anywhere online. If you accidentally included a private key, the tool will warn you.
- •CSRs are safe to share with CAs—that's their purpose. But don't share them publicly unless necessary.