The Math That Should Scare You
Certificate validity is shrinking. Renewal frequency is multiplying. Here's what that looks like for an organization managing 500 publicly-trusted certificates:
| Cert Validity | Renewals/Year (per cert) | 500 Certs = | Status |
|---|---|---|---|
| 398 days (current) | ~1x | ~500 events | Manual possible |
| 200 days (March 2026) | ~2x | ~1,000 events | Strain showing |
| 100 days (March 2027) | ~4x | ~2,000 events | Manual breaking |
| 47 days (March 2029) | ~8x | ~4,000 events | Automation mandatory |
The real question isn't "when do certs expire" — it's "can your pipeline handle 8x the throughput without a human touching it?"
Phase 1 takes effect in
days
hrs
min
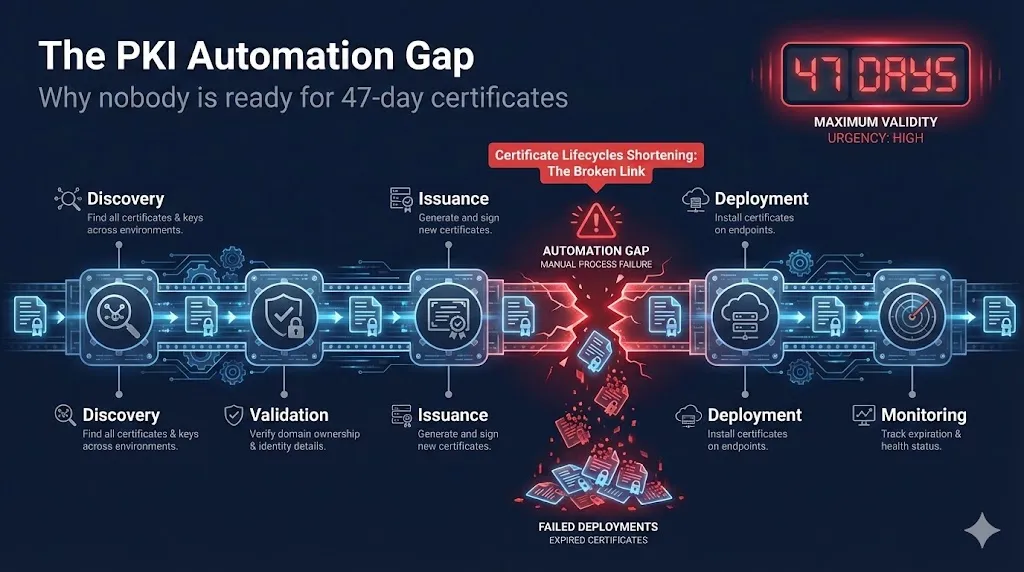
The 5-Stage Automation Pipeline
Certificate lifecycle automation isn't one problem — it's five. Each stage has its own failure modes, and a gap in any one of them breaks the entire chain.
Discovery
"You can't automate renewal of certificates you don't know exist."
The Gap:
- Shadow certificates provisioned outside central IT
- Ephemeral cloud workloads spinning up certificates dynamically
- Developer-provisioned certs in CI/CD pipelines
- IoT/OT device certificates invisible to traditional scanning
Validation
"If your CA still emails admin@ for validation, your pipeline has a human dependency."
The Gap:
- Manual DCV methods being sunset by SC-080, SC-090, SC-091
- By 2028, only DNS-01, HTTP-01, and TLS-ALPN-01 survive
- DNS API access not configured in many organizations
- Split-horizon DNS complicates automated validation
Issuance
"Works in dev, breaks in prod at scale."
The Gap:
- CA API integration and ACME configuration complexity
- Rate limits that throttle high-volume renewal bursts
- Account key management and rotation
- Retry logic and error handling for transient failures
Deployment
"This is where most 'automated' pipelines actually fail."
The Gap:
- The cert renews but never gets deployed — connector failures, config drift
- F5, Nginx, Apache, IIS, Kubernetes, and cloud providers each require different deployment mechanisms
- Service restarts and reload sequences that vary by platform
- Multi-node deployments where one node gets the cert and others don't
See our web server guides (Nginx, Apache, IIS, F5, HAProxy, Caddy, Traefik) for platform-specific deployment patterns.
Monitoring
"The automation ran but threw an error nobody saw."
The Gap:
- No alerting on failed renewals or silent ACME errors
- No monitoring of deployed certificate expiry (post-deployment verification)
- Alert fatigue from noisy dashboards teams learn to ignore
- No distinction between "renewal succeeded" and "deployment verified"
The Honest Assessment — Where Industry Really Is
Vendor marketing says one thing. Production environments say another. Here's the gap between promise and reality:
| Stage | What Vendors Say | Reality |
|---|---|---|
| Discovery | "Full visibility in days" | 60-70% coverage typical; shadow IT and cloud sprawl persist |
| Validation | "Fully automated DCV" | DNS-01 requires API access many orgs don't have configured |
| Issuance | "One-click ACME" | Works for simple cases; complex SANs, wildcards, and EV still manual |
| Deployment | "Automated provisioning" | The #1 failure point; connector ecosystem is fragile |
| Monitoring | "Real-time dashboards" | Alert fatigue; teams ignore warnings until outage |
This isn't a criticism of any specific vendor. It's an honest assessment of where the industry is right now. The tooling is improving — but most organizations haven't deployed it yet.
The 200-Day Wake-Up Call
March 15, 2026 isn't the deadline. It's the dress rehearsal. When certificate validity drops to 200 days, you get your first real test of whether your automation works at 2x throughput. If it breaks at 2x, it will absolutely break at 8x.
200-day validity takes effect in
days
hrs
min
Four Questions to Answer Before March 15
- Can you renew every cert without a human approving the DCV?
- Does deployment happen automatically after issuance?
- Do you get alerted on failures?
- Have you tested failure scenarios?
This is your free trial period for automation — use it.
What to Do Right Now
This Week (Before March 15)
- Inventory: How many certs? Where are they? Which CAs issued them?
- Identify manual dependencies: Which renewals require a human in the loop?
- Use the PKI Priority Planner: Assess your environment →
This Quarter (March–June 2026)
- Migrate all DCV to DNS-01 or HTTP-01
- Automate deployment for top 20% highest-risk certs
- Set up monitoring for renewal failures
This Year (2026)
- Achieve end-to-end automation for all publicly trusted certs
- Build and test failure scenarios
- Document and runbook everything
Resources
PKI Priority Planner
Assess your environment and get a prioritized action plan for automation readiness.
47-Day Certificate Timeline
The complete SC-081v3 timeline with live countdowns and phase breakdowns.
Which DCV Method to Automate
Decision guide for choosing between DNS-01, HTTP-01, and TLS-ALPN-01.
DNS-01 Automation
Complete guide to automating DNS-01 validation with DNS provider APIs.
HTTP-01 Automation
Automating HTTP-01 validation on Nginx, Apache, and IIS.
TLS-ALPN-01 Automation
When and how to use TLS-ALPN-01 for certificate validation.
Certificate Renewal Runbook
Step-by-step runbook for managing certificate renewals at scale.
PKI Compliance Hub
Central hub for all PKI compliance deadlines, frameworks, and requirements.
The PKI Priority Planner analyzes your environment and tells you what to focus on first.
Assess Your PrioritiesThe 47-day deadline isn't March 2029. It's March 2026 — because that's when your automation pipeline needs to start proving it works.
Assess Your Readiness