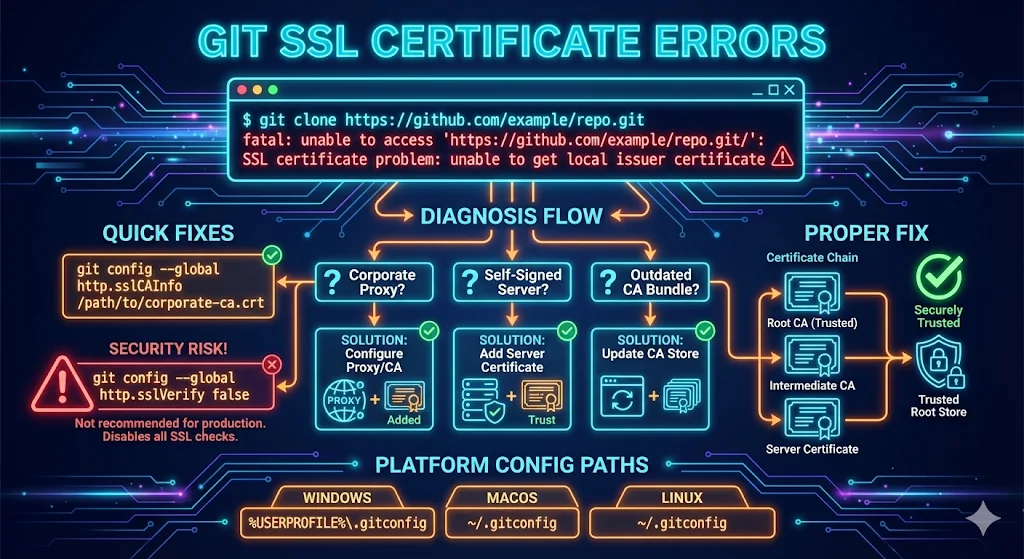
Quick Diagnosis
Corporate network or VPN connected?
→ Proxy CA issue - Jump to Corporate Proxy section
Self-hosted GitLab, Bitbucket, or Gitea?
→ Self-signed cert issue - Jump to Self-Signed section
Works in browser but not Git?
→ Git uses a different cert store than your browser
Did this just start happening?
→ VPN connected, proxy changed, or certificate expired
Understanding Git SSL Errors
Git uses its own certificate bundle, separate from your browser. This is why a site can work perfectly in Chrome but fail with Git. Common causes include:
- Corporate proxies intercepting HTTPS (SSL inspection by Zscaler, Bluecoat, etc.)
- Self-signed certificates on internal Git servers
- Outdated Git with an old CA bundle
- Windows Git vs WSL vs native Linux differences
Common Error Messages
fatal: unable to access 'https://github.com/...': SSL certificate problem: unable to get local issuer certificate fatal: unable to access 'https://gitlab.company.com/...': SSL certificate problem: self signed certificate fatal: unable to access '...': SSL certificate problem: certificate has expired error: RPC failed; curl 60 SSL certificate problem: unable to get local issuer certificate
Quick Fixes (Try These First)
Fix 1: Update Git
Often the simplest solution - newer Git versions have updated CA bundles.
# Windows: Download latest from git-scm.com # macOS brew upgrade git # Linux (Ubuntu/Debian) sudo apt update && sudo apt upgrade git
Fix 2: Update Git's CA Bundle
# Check current bundle git config --global http.sslCAInfo # Point to system bundle (Linux) git config --global http.sslCAInfo /etc/ssl/certs/ca-certificates.crt # macOS with Homebrew git config --global http.sslCAInfo $(brew --prefix)/etc/openssl@3/cert.pem
Fix 3: Use System SSL Backend (Windows)
Tell Git to use the Windows certificate store instead of its bundled certs.
git config --global http.sslBackend schannel
Corporate Proxy and SSL Inspection
This is the #1 cause in corporate environments
Corporate networks (Zscaler, Bluecoat, Palo Alto, Fortinet) intercept HTTPS traffic. They decrypt, inspect, and re-encrypt with their own certificate. Git doesn't trust this certificate.
Step 1: Get Your Corporate Root CA
- Export from browser (Chrome: Settings → Security → Manage certificates)
- Ask IT for the certificate file
- Usually a
.crtor.pemfile
Step 2: Tell Git to Trust It
# Option A: Add to Git's config git config --global http.sslCAInfo /path/to/corporate-ca-bundle.pem # Option B: Append to existing bundle cat corporate-root-ca.pem >> /path/to/git/ssl/certs/ca-bundle.crt # Option C: Windows - use schannel (reads from Windows store) git config --global http.sslBackend schannel # Then add your corporate CA to Windows certificate store
Step 3: Verify
git clone https://github.com/octocat/Hello-World.git
Self-Signed Certificates (Internal Git Servers)
For self-hosted GitLab, Bitbucket, or Gitea with self-signed certificates.
Option 1: Add the Certificate to Git (Recommended)
# Get the cert from server (with SNI support) openssl s_client -connect gitlab.company.com:443 -servername gitlab.company.com </dev/null 2>/dev/null | \ sed -ne '/-BEGIN CERTIFICATE-/,/-END CERTIFICATE-/p' > gitlab-cert.pem # Tell Git to trust it git config --global http."https://gitlab.company.com/".sslCAInfo /path/to/gitlab-cert.pem
Option 2: Trust for Specific Repo Only
cd /path/to/repo git config http.sslCAInfo /path/to/gitlab-cert.pem
Option 3: Disable Verification for Specific Host
Use with caution - only for internal servers you trust
git config --global http."https://gitlab.company.com/".sslVerify false
The Nuclear Option (Disable SSL Verification)
WARNING: This makes you vulnerable to man-in-the-middle attacks
Only use this as a temporary workaround while getting proper CA certificates. Never use for public repositories (GitHub, GitLab.com, Bitbucket.org).
# DON'T DO THIS for public repos (GitHub, GitLab.com, etc.) git config --global http.sslVerify false # Or per-command GIT_SSL_NO_VERIFY=true git clone https://... # Or environment variable export GIT_SSL_NO_VERIFY=true
When it's "acceptable"
- • Temporary workaround while getting proper CA cert
- • Air-gapped lab environments
- • Local development only
When it's NEVER acceptable
- • Production systems
- • Public repositories
- • Any machine that leaves your secure network
Platform-Specific Guides
Windows (Git for Windows)
# Use Windows certificate store (best option) git config --global http.sslBackend schannel # Check current backend git config --global http.sslBackend
Windows (WSL)
# WSL has its own cert store, separate from Windows # Update CA certs sudo apt update && sudo apt install ca-certificates sudo update-ca-certificates # Or point to a specific bundle git config --global http.sslCAInfo /etc/ssl/certs/ca-certificates.crt
Debugging Git SSL Issues
Check What Certificate Git Sees
GIT_CURL_VERBOSE=1 git clone https://github.com/octocat/Hello-World.git
Check with OpenSSL
openssl s_client -connect github.com:443 -showcerts
Check Git's SSL Configuration
git config --global --list | grep -i ssl git config --global http.sslBackend git config --global http.sslCAInfo
Git Configuration Reference
| Config | Purpose | Example |
|---|---|---|
| http.sslVerify | Enable/disable SSL verification | true / false |
| http.sslCAInfo | Path to CA bundle file | /etc/ssl/certs/ca-certificates.crt |
| http.sslCAPath | Path to directory of CA certs | /etc/ssl/certs/ |
| http.sslCert | Client certificate (for mTLS) | /path/to/client.crt |
| http.sslKey | Client private key (for mTLS) | /path/to/client.key |
| http.sslBackend | SSL library to use | openssl / schannel |
Scope Options
# Global (all repos) git config --global http.sslCAInfo /path/to/ca.pem # Per-host git config --global http."https://gitlab.company.com/".sslCAInfo /path/to/ca.pem # Per-repo (run inside repo) git config http.sslCAInfo /path/to/ca.pem
CI/CD Pipelines
GitHub Actions
- name: Configure Git SSL
run: |
git config --global http.sslCAInfo ${{ github.workspace }}/certs/ca-bundle.pemGitLab CI
before_script: - git config --global http.sslCAInfo /etc/ssl/certs/ca-certificates.crt
Jenkins
withEnv(['GIT_SSL_CAINFO=/path/to/ca-bundle.pem']) {
git url: 'https://gitlab.company.com/repo.git'
}Docker
# Add corporate CA COPY corporate-ca.crt /usr/local/share/ca-certificates/ RUN update-ca-certificates # Or for Git specifically RUN git config --global http.sslCAInfo /etc/ssl/certs/ca-certificates.crt
FAQ
Q: Why does Git have SSL errors when my browser works fine?
Git uses its own certificate bundle, separate from your browser. Your browser trusts your corporate CA, but Git doesn't know about it.
Q: Is it safe to disable SSL verification?
No, not for public repositories. You become vulnerable to man-in-the-middle attacks. Only disable for isolated lab environments as a temporary measure.
Q: How do I fix this permanently for my whole team?
Distribute the corporate CA certificate and add it to Git's configuration via a script, or use http.sslBackend schannel on Windows so Git uses the company-managed Windows certificate store.
Q: Why did this start happening suddenly?
Common causes: VPN connected, corporate proxy changed, certificate expired, Git updated, or company rolled out new SSL inspection.
Q: Does this affect SSH Git operations?
No, SSH uses a completely different authentication mechanism. This only affects HTTPS Git URLs.
Related Resources
OpenSSL s_client Guide
Debug what certificate the server sends.
Self-Signed Certificates
Create and manage self-signed certs properly.
Certificate Chain Builder
Understand and fix certificate chain issues.
Python SSL Certificate Errors
Same root cause, different tool.
Certificate Error Decoder
Decode cryptic SSL/TLS errors with fixes.
Certificate Failure Scenarios
Common PKI failures and how to fix them.