Quick Answer
This guide is for technology, risk, and security leaders who need to demonstrate DORA-aligned control over certificates.
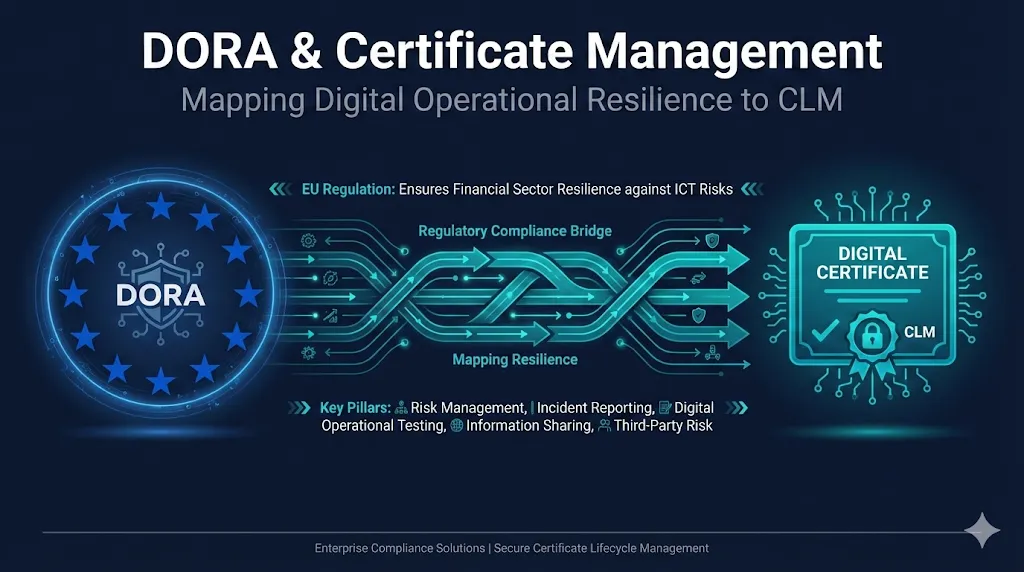
DORA (Digital Operational Resilience Act) is an EU regulation requiring financial entities to demonstrate operational resilience against ICT risks. Certificates—the digital IDs that secure logins, APIs, and data in transit—are critical ICT assets. Certificate lifecycle management (how certificates are issued, renewed, revoked, and tracked across your estate) is now directly relevant to DORA compliance.
Why this matters: Unmanaged certificates can now trigger outages, regulatory findings, and board-level scrutiny—not just IT incidents.
💡 Rule of Thumb: If you cannot show "who owns which cert" and produce a complete inventory within minutes, you have both an operational and a regulatory risk problem.
Most organizations aren't there yet—that's normal. This guide and our Maturity Assessment give you a path to get there.
What is DORA?
The Digital Operational Resilience Act (EU 2022/2554) is an EU regulation that establishes a uniform framework for managing ICT risks in the financial sector. Unlike voluntary frameworks, DORA is mandatory with penalties.
Effective Date
January 17, 2025 - DORA is now in force. In-scope entities are expected to demonstrate progress and preparedness to their competent authority.
Key Difference
Unlike NIST CSF or ISO 27001, DORA is legally binding for in-scope entities, with enforcement by national supervisory authorities.
Who Does DORA Apply To?
- Banks & Credit Institutions
- Insurance Companies
- Investment Firms
- Crypto-Asset Providers
- Payment Institutions
- ICT Third-Party Providers
Key Deadlines
The Five Pillars of DORA & Certificate Touchpoints
DORA is built on five pillars. Each has direct implications for certificate and PKI management.
Use this section to brief executives and risk partners on why PKI work matters for DORA.
| DORA Pillar | Certificate/PKI Relevance |
|---|---|
| ICT Risk Management | Certificate inventory, expiry tracking, CA trust decisions, weak key detection |
| ICT Incident Reporting | Certificate-related outages, compromise reporting timelines, root cause analysis |
| Digital Operational Resilience Testing | Certificate failover testing, revocation response drills, CA compromise exercises |
| ICT Third-Party Risk | CA vendor assessment, CLM provider SLAs, multi-CA strategy, exit planning |
| Information Sharing | Threat intel on CA compromises, industry ISAC participation, CT log monitoring |
Mapping CLM Capabilities to DORA Requirements
Articles 5-15: ICT Risk Management Framework
| DORA Requirement | CLM Capability | Resource |
|---|---|---|
| Asset inventory (Art. 8) | Certificate discovery & inventory | Certificate Discovery Guide |
| Risk identification (Art. 8) | Expiry monitoring, weak key detection | Failure Scenarios Demo |
| Protection measures (Art. 9) | Automated renewal, key rotation | Certificate Lifecycle Guide |
| Detection capabilities (Art. 10) | CT log monitoring, anomaly detection | Certificate Transparency Guide |
| Response & recovery (Art. 11) | Emergency replacement procedures | Emergency Replacement Runbook |
Articles 17-23: ICT Incident Management
| DORA Requirement | CLM Capability | Resource |
|---|---|---|
| Incident classification | Certificate outage severity matrix | Failure Scenarios Guide |
| Root cause analysis | Chain validation, revocation checking | Cert Error Decoder |
| Reporting timelines | Automated alerting with audit trail | Certificate Lifecycle Guide |
Articles 24-27: Resilience Testing
| DORA Requirement | CLM Capability | Resource |
|---|---|---|
| Scenario-based testing | Certificate expiry simulations | Failure Scenarios Demo |
| Threat-led penetration testing | CA compromise response drills | Key Compromise Runbook |
Articles 28-44: Third-Party Risk Management
| DORA Requirement | CLM Capability | Resource |
|---|---|---|
| Due diligence on ICT providers | CA selection criteria, root store trust | Root Stores Guide |
| Contractual arrangements | SLA requirements for cert issuance/revocation | What is a CPS? |
| Concentration risk | Multi-CA strategy, avoiding single points of failure | Wildcard Dangers Guide |
| Exit strategies | CA migration planning | CA Migration Runbook |
The 10-Minute Auditor Test
Auditor Heuristic: As one industry expert put it: "If you cannot stand up in front of an auditor and give your full online services and private services that you are certifying within 10 minutes, that auditor is going to consider that to be a failure." This isn't a literal legal requirement, but it's a useful rule of thumb for operational readiness.
Use this self-assessment checklist to evaluate your DORA readiness for certificate management:
Self-Assessment Checklist
If you can't check all of these, you're not DORA-ready yet for certificates:
Benchmark Your Readiness
Take our comprehensive assessment to score your PKI governance maturity and get prioritized recommendations.
Take the Maturity AssessmentImplementation Roadmap
Phase 1: Discovery
Weeks 1–4• PKI + Infra- Deploy certificate discovery across all environments
- Classify certificates by business criticality
- Map certificates to ICT services inventory
Phase 2: Documentation
Weeks 5–8• Security + Risk- Document certificate ownership and accountability
- Create/update certificate management procedures
- Establish SLAs with CA vendors
Phase 3: Automation
Weeks 9–12• PKI + DevOps- Implement automated expiry alerting
- Deploy automated renewal where possible
- Integrate with ITSM for incident tracking
Phase 4: Testing
Ongoing• All teams- Quarterly certificate failover drills
- Annual CA compromise tabletop exercises
- Document lessons learned
Country-Level Considerations
Key Insight: DORA enforcement varies by country. While the regulation is EU-wide, national supervisory authorities have different focus areas and enforcement approaches. This helps compliance and legal teams prioritize regulator conversations and evidence preparation.
Note: The focus areas below are illustrative, not exhaustive or official positions. Always verify with your local authority.
| Country | Supervisory Authority | Known Focus Areas |
|---|---|---|
| Germany | BaFin | Strict ICT risk documentation |
| France | ACPR/AMF | Third-party concentration risk |
| Netherlands | DNB/AFM | Operational resilience testing |
| Ireland | CBI | Cross-border service providers |
| UK | FCA/PRA | Post-Brexit dual compliance (DORA + UK CSR) |
Frequently Asked Questions
Does DORA apply to my organization if we use a third-party CA?
Yes. DORA requires due diligence on all ICT third-party providers, including Certificate Authorities. You must assess CA vendor risk, document SLAs for certificate issuance and revocation, and have exit strategies in place.
Is certificate management explicitly mentioned in DORA?
Not explicitly, but certificates are critical ICT assets that fall under the asset inventory, risk management, and third-party risk requirements. Any ICT asset that could cause service disruption is in scope.
What counts as a "major ICT-related incident" for certificate issues?
A certificate expiry causing service outage to customers, a CA compromise affecting your certificates, or a key compromise would likely qualify. Thresholds and materiality criteria are defined by each competent authority and Regulatory Technical Standards (RTS), so always cross-reference your local guidance.
How often should we test certificate failover?
DORA requires "regular" digital operational resilience testing. Best practice is quarterly certificate failover drills and annual CA compromise tabletop exercises.
Does DORA apply to UK firms?
DORA applies to UK firms if they operate within the EU or serve EU clients. UK-only operations fall under the upcoming UK Cyber Security and Resilience (CSR) Bill instead. Many firms are "dual-regulated" and need to prepare for both.
If You Only Do Three Things...
Short on time? Focus on these three priorities to make immediate DORA progress:
Inventory
Know every certificate. Deploy discovery and map to business services.
Ownership
Assign clear owners. Someone must be accountable for every cert.
Automation
Automate alerts and renewals. Humans forget; systems don't.
Related Resources
PKI Governance Maturity Assessment
Score your certificate management maturity across 6 categories.
Certificate Discovery Guide
How enterprise platforms find every certificate in your environment.
Compliance Hub
Track deadlines across CA/Browser Forum, DORA, NIS2, and browser programs.
Checklists & Runbooks
Emergency replacement, key compromise response, and CA migration procedures.