Finally Understand PKI & TLS
See It In Action
Interactive visualizations that make complex concepts click
Visual Handshakes
Watch TLS packets fly between client and server. Understand exactly when encryption kicks in.
Read the GuideChain Validation
See how browsers traverse the trust chain from leaf to root, and why intermediate certs matter.
Read the GuideCertificate past validity
Failure Scenarios
Simulate expired certs, revocations, and MITM attacks to learn how to troubleshoot real incidents.
Read the GuideLearn By Doing
Visual, step-by-step demonstrations of PKI concepts. Click through to understand how things actually work.
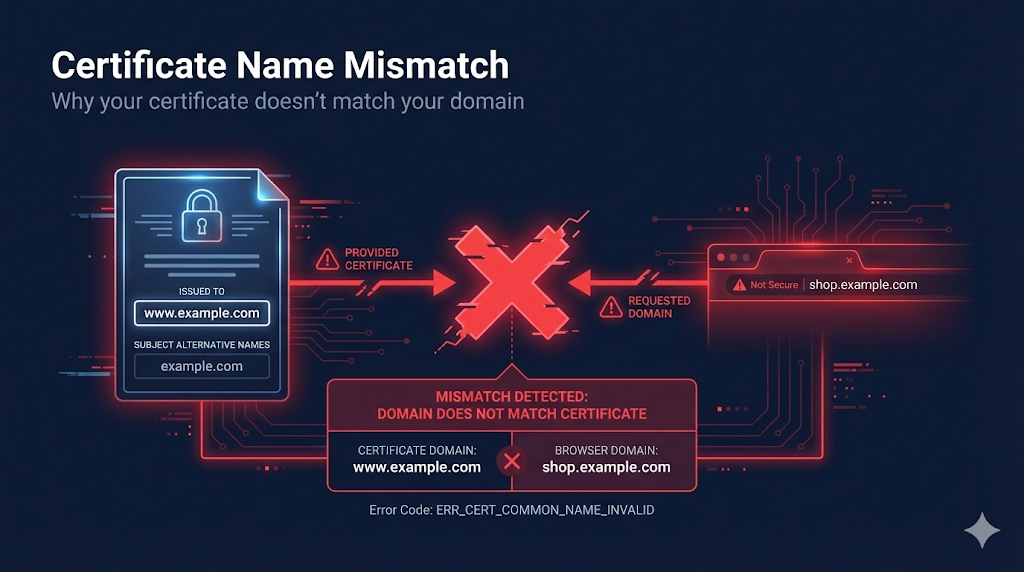
Certificate Name Mismatch
Debug certificate name mismatch errors. Understand CN vs SAN, wildcard scope, and common mistakes.
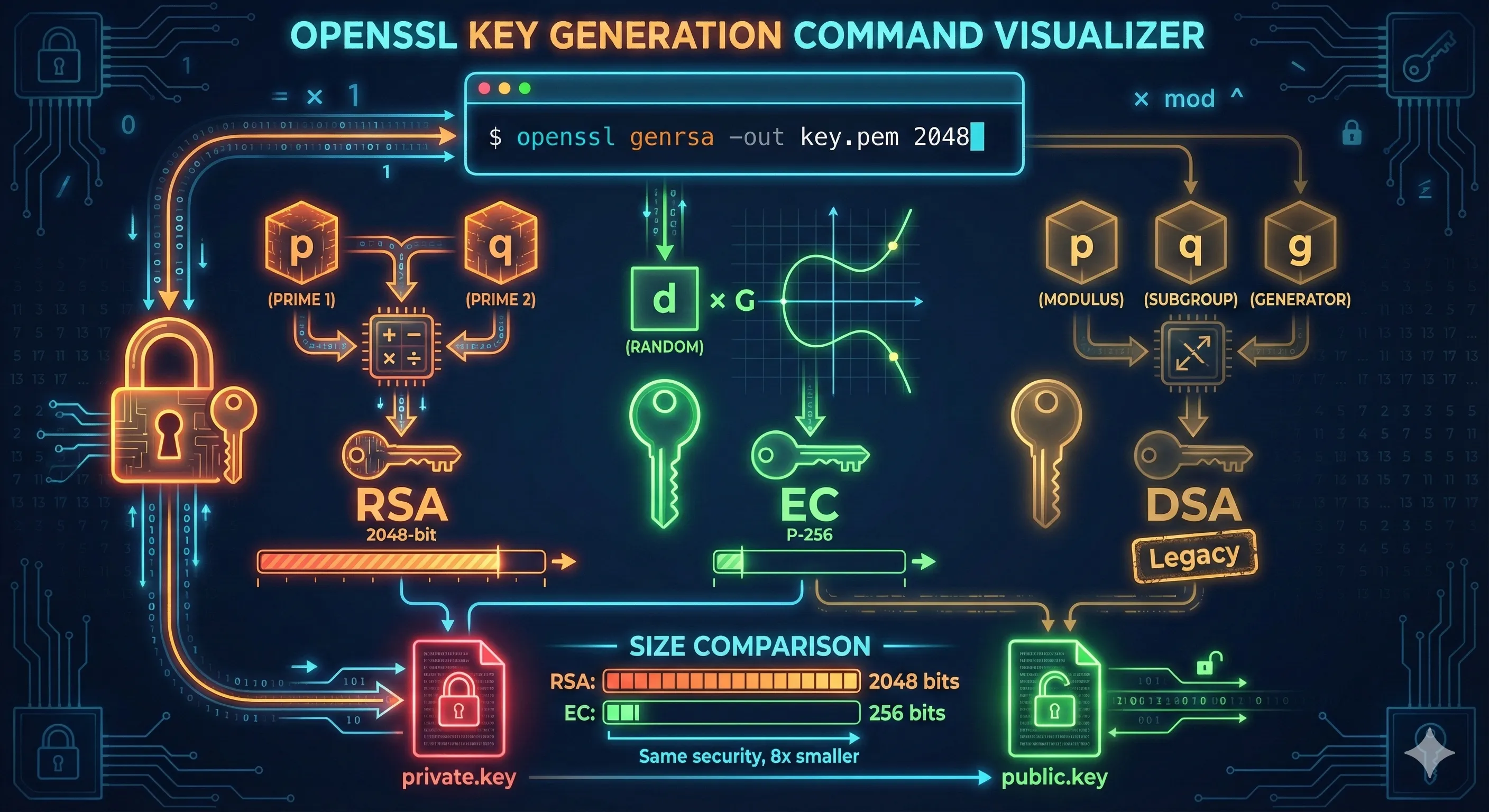
OpenSSL Key Generation
Generate RSA and ECC private keys with OpenSSL. Learn proper key sizes and security parameters for certificates.
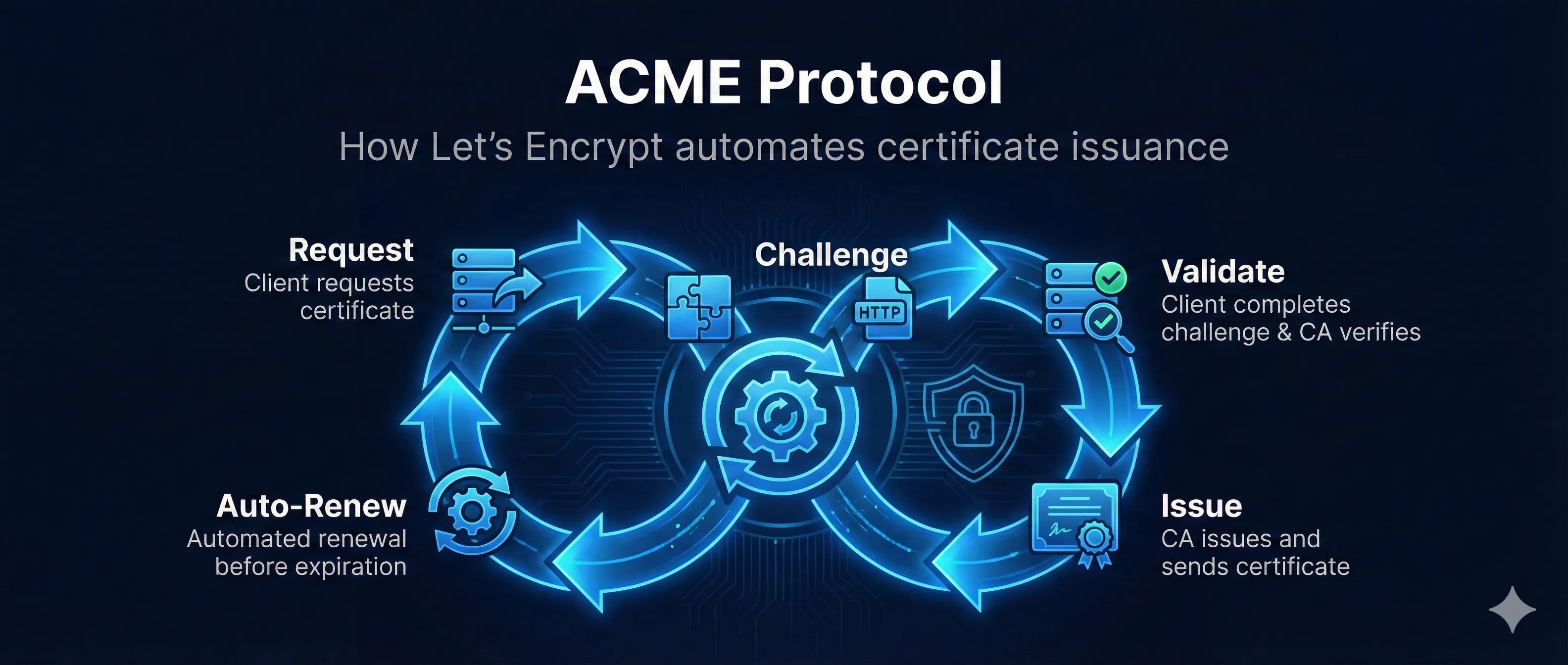
ACME Protocol - Automated Certificate Issuance
Learn how ACME protocol automates certificate issuance with Let's Encrypt. Interactive demo shows the challenge-response flow and DNS/HTTP validation.

Encryption Fundamentals
Learn symmetric vs asymmetric encryption fundamentals. Interactive demo shows AES, RSA, and why TLS uses both.
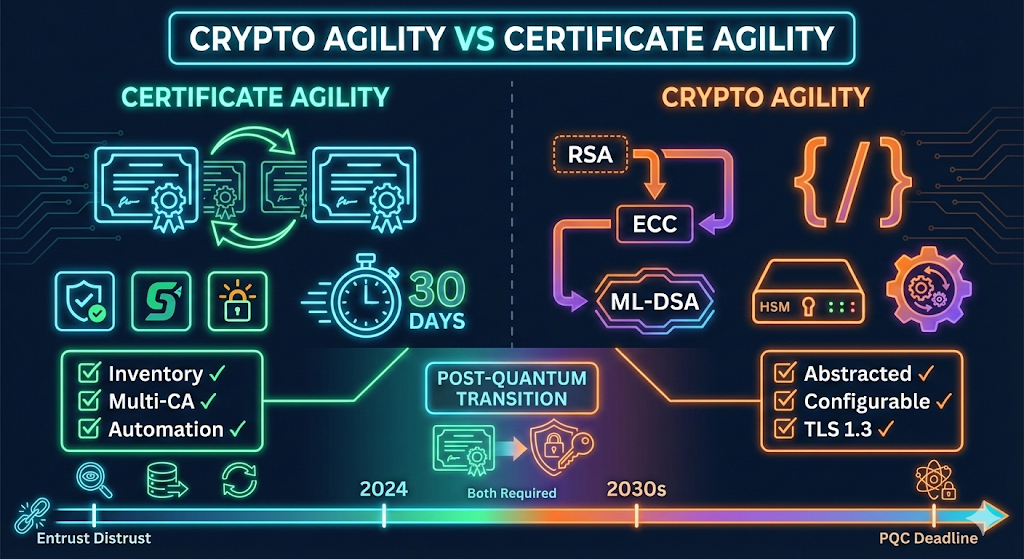
Crypto Agility vs Certificate Agility
Understand the critical difference between crypto agility and certificate agility. Learn why you need both to survive CA distrust events and the post-quantum transition.

S/MIME Email Security
See how S/MIME certificates enable encrypted and signed email. Understand the difference from PGP.

Self-Signed Certificates
Understand when self-signed certificates are appropriate and their security implications.
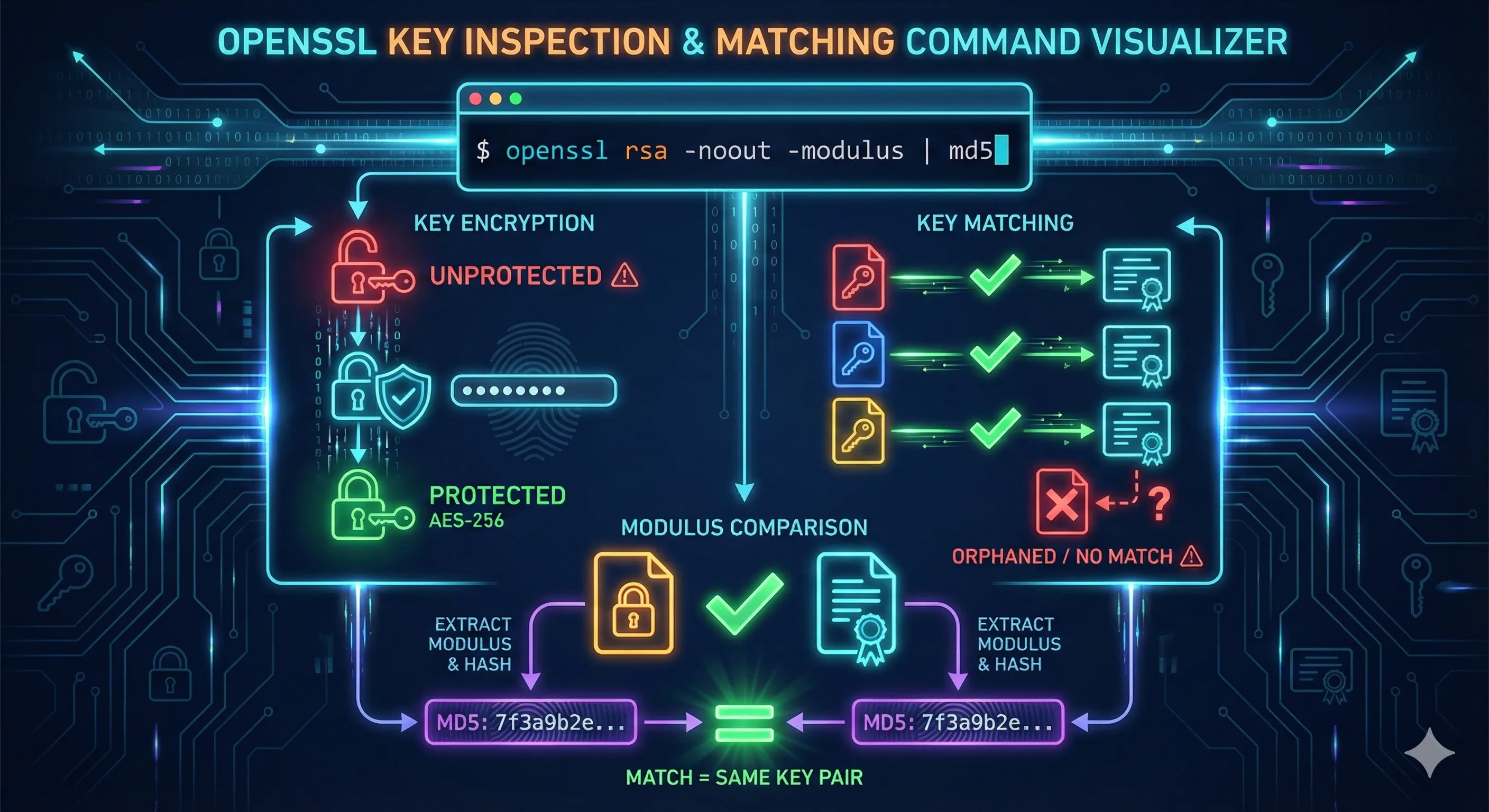
OpenSSL Certificate Inspection
Inspect certificates with OpenSSL commands. View subject, issuer, validity, SANs, and extensions from the command line.
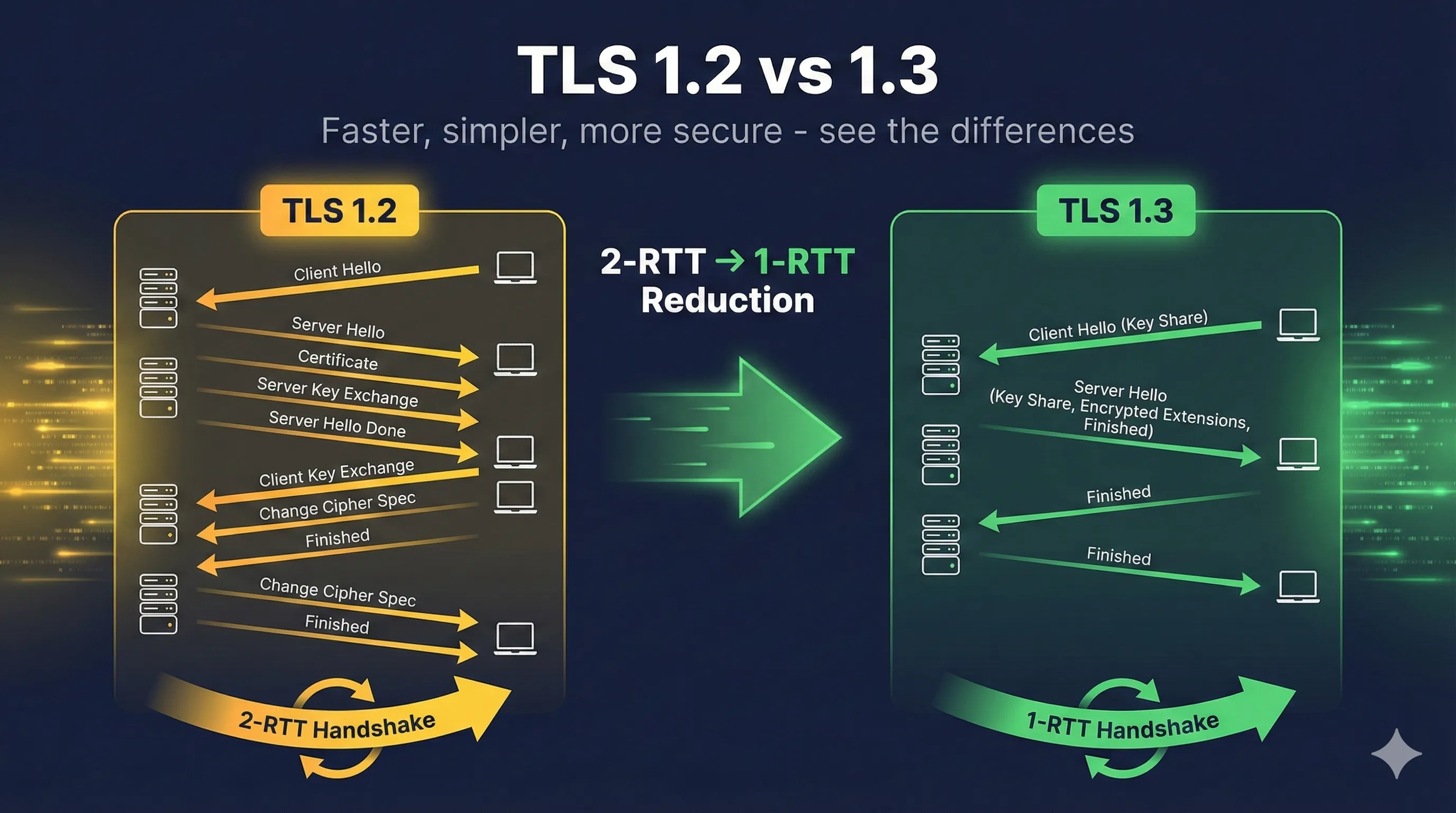
TLS Version Comparison
Compare TLS 1.0, 1.1, 1.2, and 1.3. Understand security improvements and migration requirements.

Subject Alternative Names (SAN)
Master SANs for multi-domain certificates. See SAN types: DNS, IP, email, and URI with real examples.
Start Learning
In-depth guides for real-world PKI challenges. From installation to troubleshooting.

NIST Certificate Management
Map NIST key management and cryptography standards to certificate lifecycle management. Covers SP 800-57, 800-52, 800-131A with practical CLM implementation guidance.
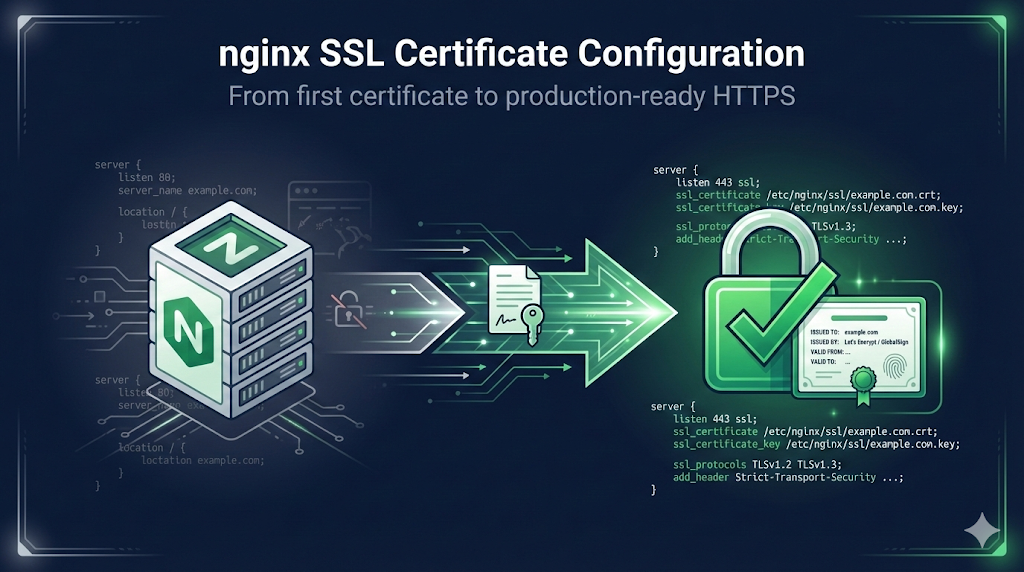
nginx SSL Certificate Configuration
Complete guide to configuring SSL/TLS in nginx. From first certificate to A+ grade - production-ready HTTPS.
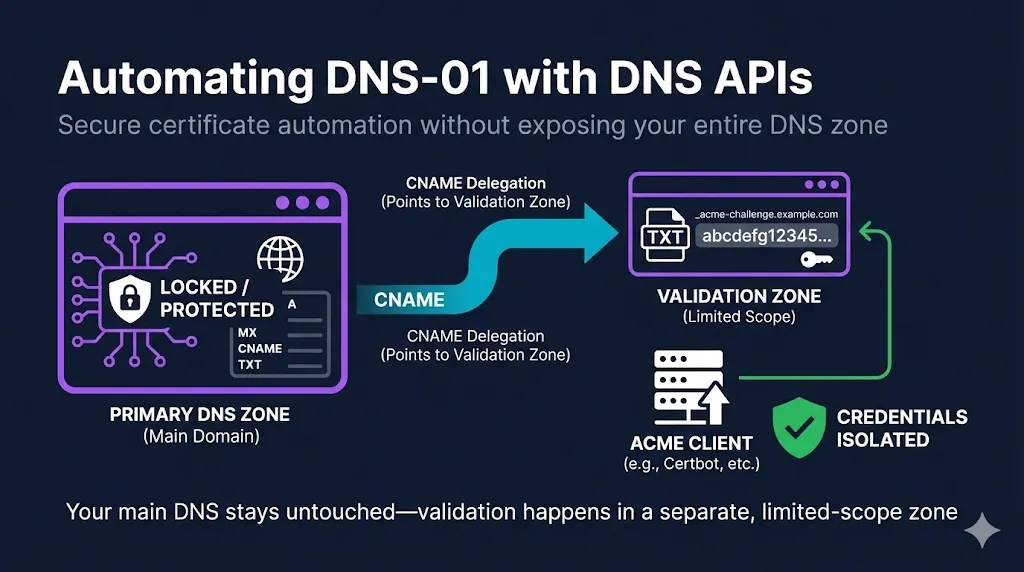
Automating DNS-01 with DNS APIs
Complete guide to DNS-01 automation with DNS provider APIs. Learn CNAME delegation, security best practices, and provider-specific configurations for Cloudflare, Route53, Azure DNS, and more.

SSH Certificate Authority Setup
Create your own SSH CA with native OpenSSH. Key generation, protection levels, distribution, signing workflow, and operational procedures.

SSH User Certificates
Authenticate users without authorized_keys files. Signing commands, principals, extensions, short-lived certificates, and migration strategy.

What is the CA/Browser Forum?
Learn how the CA/Browser Forum sets the rules for SSL/TLS certificates, who's involved, how ballots work, and why their decisions affect your certificate management.
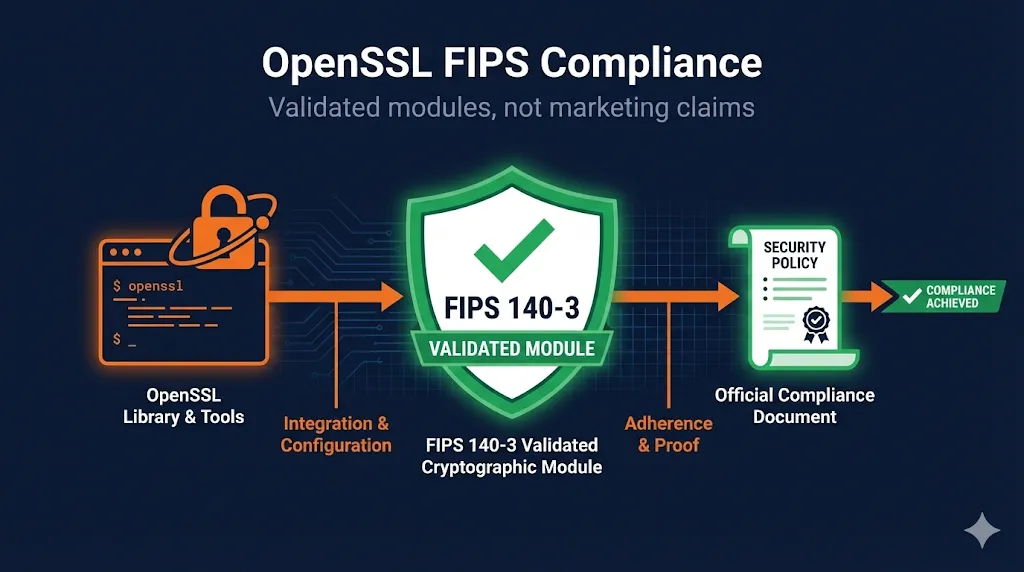
OpenSSL FIPS Compliance Guide
Implement FIPS 140-3 validated cryptography with OpenSSL 3.x. Learn FIPS capable vs compliant, configure the FIPS provider, and document for auditors.

Traefik SSL Certificate Configuration
Automatic HTTPS for containers and services. Let's Encrypt automation, Docker labels, Kubernetes IngressRoute, and manual certificate configuration.
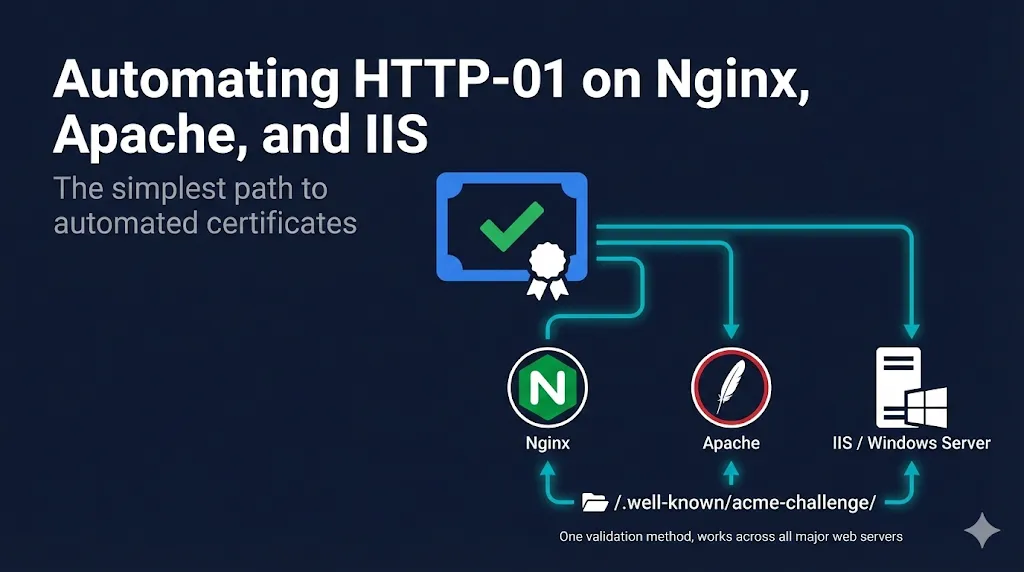
Automating HTTP-01 on Nginx, Apache, and IIS
Complete guide to HTTP-01 automation on Nginx, Apache, and IIS. The simplest path to automated certificates with Certbot, win-acme, and production-ready configurations.
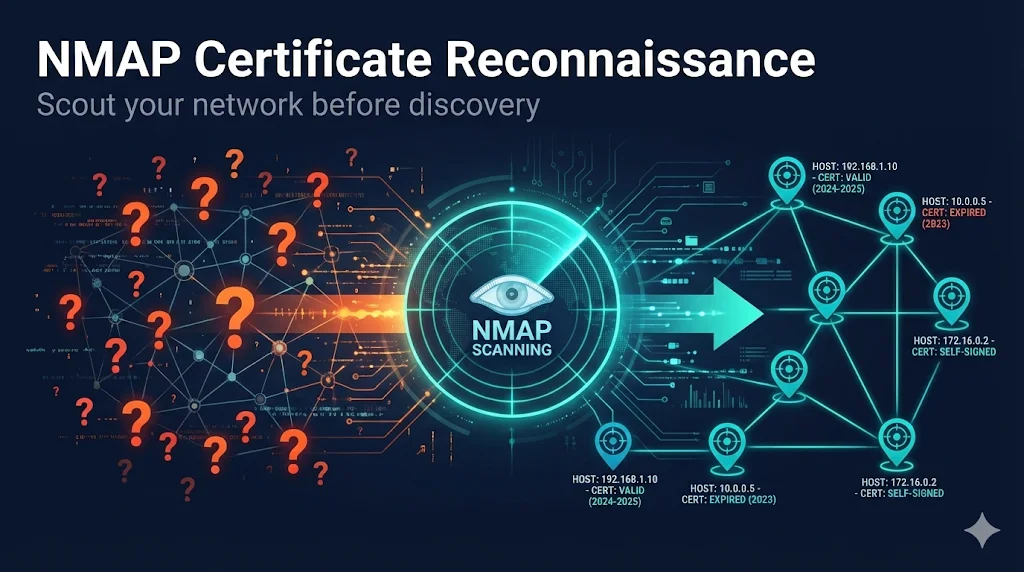
NMAP Certificate Reconnaissance
Use NMAP to find all SSL/TLS certificates before running expensive CLM discovery jobs. Reduce 12-hour scans to 30 minutes.
Explore Our Guide Series
Multi-part deep dives into complex PKI topics
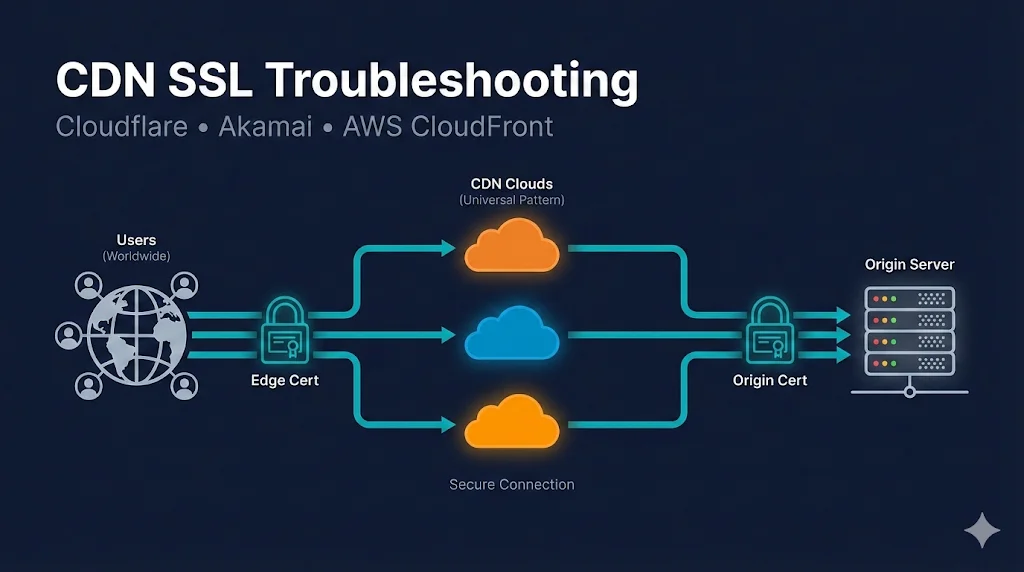
CDN SSL Troubleshooting
Cloudflare, Akamai, AWS CloudFront
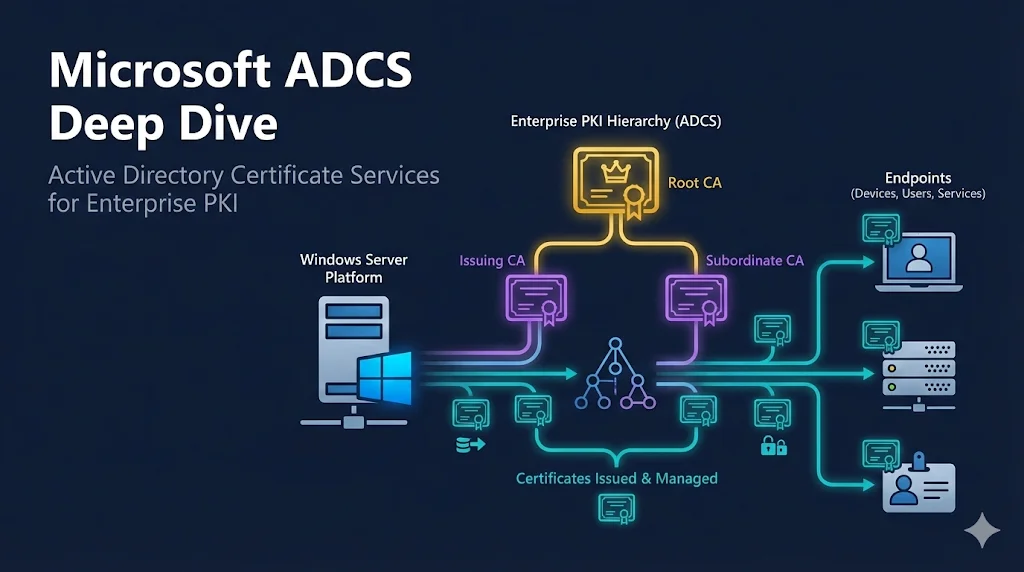
Microsoft ADCS Deep Dive
Active Directory Certificate Services for Enterprise PKI
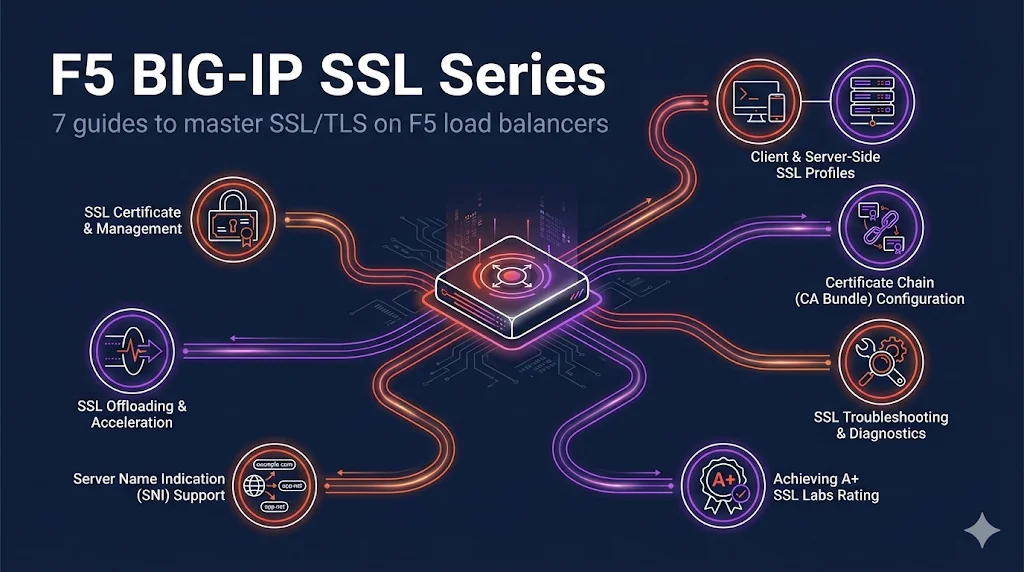
F5 BIG-IP SSL Series
Master SSL/TLS on F5 load balancers
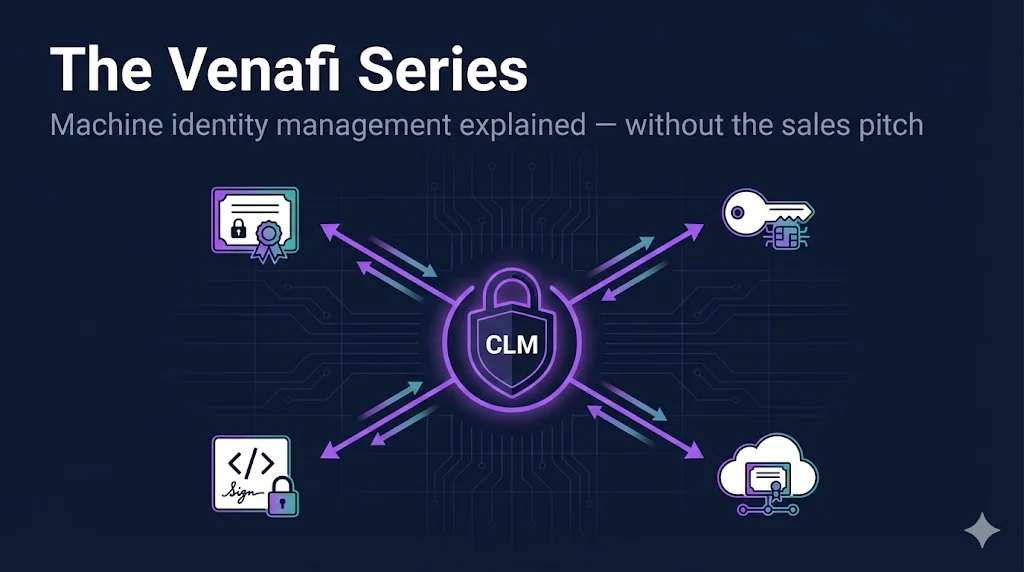
The Venafi Series
Machine identity management explained
What's New
Here's what we've been building for you
New Blog: Key Ceremony Best Practices — What Your Script Should Include
A practitioner-level guide to PKI key ceremony scripts covering what to include, what auditors verify, and the common mistakes that create findings
We published a deep-dive blog post on key ceremony scripts — the formal, witnessed process of generating cryptographic keys for a Certificate Authority. This isn't the academic "what is a key ceremony" overview you find elsewhere. It's a practitioner's breakdown of what your script should actually contain: pre-ceremony checklists, HSM operations structure, key backup procedures, witness requirements, and the specific documentation gaps that generate audit findings. The post includes five custom infographics — roles diagram, pre-ceremony checklist flow, ceremony script flow, audit red flags, and common mistakes — plus a video walkthrough. We also added cross-links from 6 related pages (HSM guide, CA Hierarchy guide, What Is a CPS guide, Internal CA CPS blog, and PCI DSS checklist) so readers can discover it naturally.
Key Ceremony Best PracticesCompliance Hub v2.3.0: Chrome Root Program 1.8, Mozilla MRSP 3.0, and New Deadline Categories
Major update to the PKI Compliance Hub with Chrome Root Program v1.8 and Mozilla Root Store Policy v3.0 data, 7 new deadlines, and new filtering categories for root store, platform, automation, and certificate transparency events
The PKI compliance landscape shifted significantly this month. Chrome Root Program v1.8 brings CT pre-logging requirements, root store consolidation plans, and a firm March 2027 deadline for subordinate CA automation. Mozilla Root Store Policy v3.0 introduces dual-purpose root transition plans due April 2026 with full migration by end of 2028. We also added the Microsoft Secure Boot certificate expiration (June 2026) — a high-impact event that affects enterprise device fleets. The Compliance Hub now tracks all of these with 7 new deadlines, an updated root store comparison table with two new rows (Dual-Purpose Root Deadline and CT Pre-Logging), and four new category filters so you can quickly find what matters to your team. The Compliance-in-a-Box page also got a visual upgrade — a 47-day certificate urgency timeline and an inline Kit form so you can preview Section 1 of the CP/CPS template before purchasing.
PKI Compliance HubNew: DNS-PERSIST-01 Guide + Security Analysis Blog Post
Comprehensive guide to the new persistent ACME DNS validation method (SC-088v3) plus a companion blog post analyzing 5 security assumptions that change with persistent authorization
DNS-PERSIST-01 is the biggest change to ACME certificate validation since DNS-01 was introduced. The CA/Browser Forum approved it unanimously, Let's Encrypt announced support, and production rollout is expected Q2 2026. We published a full guide covering how it works, how it compares to DNS-01, scope controls, security tradeoffs, implementation timeline, and a decision framework to help you decide when to adopt. We also wrote a companion blog post that goes deeper on the security side — five specific assumptions that change when your certificate validation becomes persistent, and what your team should do about each one. Both resources include video walkthroughs.
DNS-PERSIST-01 GuideStay Compliant
Certificate validity periods are shrinking. Track deadlines and requirements with our live compliance hub.
Practical Tools
Validate CSRs, diagnose issues, and track compliance. All the tools you need in one place.
PKI Priority Planner
Find out if your team is working on the right PKI priorities. Get a personalized action plan based on your environment and compliance deadlines.
CSR Checker
Validate and decode Certificate Signing Requests. Check for common issues before submitting to a CA.
PKI Troubleshooter
AI-powered diagnostic tool for SSL/TLS certificate issues. Get step-by-step solutions.
Practical TLS by Ed Harmoush
The most comprehensive TLS course available. Real Wireshark captures, hands-on labs, and explanations that actually make sense. Use code FixMyCert for 50% off.
Disclosure: I earn a commission if you purchase through this link, at no extra cost to you.
Built for IT Professionals
DevOps & SREs
Debug ingress issues and automate certificate rotation with confidence.
Security Engineers
Visualize threat models and explain PKI concepts to stakeholders.
Network Engineers
Deep dive into TLS 1.2 vs 1.3, ciphers, and handshake performance.